A security group is a virtual firewall that controls inbound and outbound traffic of Application Load Balancer (ALB) based on inbound and outbound rules. To allow or reject access from specific IP addresses to an ALB instance, you can add the ALB instance to a security group. A security group can function as a blacklist or whitelist for an ALB instance. You can create security group rules to implement finer-grained access control.
Scenarios
Before the ALB instance is added to a security group, the listener ports of the ALB instance allow all requests by default.
After the ALB instance is added to a security group which does not contain Deny rules, the listener ports of the ALB instance allow all requests by default. If you want to allow requests only from specific IP addresses to your ALB instance, you must also create a Deny rule.
For more information about how to allow or deny access from specific IP addresses, see Use security groups as blacklists or whitelists.
For more information about how to configure access control based on protocols and ports, see Use security groups to control access based on ports.
If your ALB instance has access control requirements and you want to control inbound traffic to the ALB instance, you can add the ALB instance to a security group and configure security group rules based on your business requirements.
ALB outbound traffic refers to response packets that are returned to users. To ensure service continuity, ALB security groups do not block outbound packets. You do not need to create outbound rules.
After an ALB instance is created, a managed security group is automatically created within the VPC where the instance resides. ALB manages the security group. You can view but cannot operate on it. Managed security groups for ALB include the following types of security group rules:
Rules whose priority is 1: These rules are used to allow local IP addresses of the ALB instance to enable communication between ALB and backend servers.
When you create a security group, we recommend that you do not add local IP addresses of ALB to Deny rules whose priority is 1. Otherwise, the security group rules may conflict with the managed security groups of ALB and interrupt communication between ALB and backend servers. To view the local IP addresses of an ALB instance, log on to the ALB console and go to the details page of the ALB instance.
Rules whose priority is 100: These rules are used to allow all IP addresses. This means that, for an ALB instance that is added to security groups without any Deny rules, the listener ports of the ALB instance allow all requests.
At the same time, default access control rules of both basic and advanced security groups include a rule that deny all requests. With basic or advanced security groups and the managed security group both working for an ALB instance, the default allow rules in the managed security group prioritize the rules in the basic or advanced security groups.
This topic describes how to use a security group as a blacklist and a whitelist in two scenarios. For more information about security group rule priorities, see Sorting policy of security group rules.
Blacklist: Configure the ALB security group to deny access from specific IP addresses
A company deployed businesses on ALB in a region of Alibaba Cloud. Security inspection detects malicious requests and attacks from an IP address, such as 121.XX.XX.12. Such behaviors can cause business risks and security risks such as data leaks.
To resolve this issue, the company can configure a security group rule for the ALB instance to deny access from specific IP addresses, such as 121.XX.XX.12. The security group rule can block malicious requests and attacks from specific IP addresses to improve business security and stability.

Whitelist: Configure the ALB security group to allow access from specific IP addresses
A company deployed businesses that contain sensitive data on ALB in a region of Alibaba Cloud. To restrict access to the ALB instance, the company can configure a security group rule to allow access only from specific IP addresses, such as 121.XX.XX.12. Requests from other IP addresses are rejected.

Limits
Upgraded ALB instances support both security groups and access control lists (ACLs) to control incoming traffic, while non-upgraded ALB instances support only ACLs. If you want to use security groups for ALB, create ALB instances, which are the upgraded version by default, or contact your account manager to apply for an upgrade on your existing non-upgraded instances.
Category | Security group type | Description |
Security groups supported by ALB |
|
For more information about basic security groups and advanced security groups, see Basic security groups and advanced security groups. |
Security groups not supported by ALB | Managed security group | For more information about managed security groups, see Managed security groups. |
Prerequisites
A virtual private cloud (VPC) named VPC1 is created in the China (Hangzhou) region. A vSwitch named VSW1 is created in Zone H and another vSwitch named VSW2 is created in Zone I. For more information, see Create a VPC and a vSwitch.
Two Elastic Compute Service (ECS) instances are created in VSW1, and applications are deployed on ECS01 and ECS02.
For more information about how to create an ECS instance, see Create an instance by using the wizard.
The following commands show how to deploy applications on ECS01 and ECS02:
A domain name is registered, and an Internet content provider (ICP) number is obtained for the domain name. For more information, see Register a domain name on Alibaba Cloud and Overview.
The following table describes the IP addresses of the clients and servers. The IP addresses are for reference only.
Category | IP | Description |
ECS01 (server) |
| The backend servers of the ALB instance. |
ECS02 (server) |
| |
Client03 | Public: 121.XX.XX.12 | The client that accesses the ALB instance. |
Client04 | Public: 121.XX.XX.45 |
Procedure
Step 1: Create a server group
Log on to the ALB console.
In the top navigation bar, select the region in which you want to create a server group. In this example, China (Hangzhou) is selected.
In the left-side navigation pane, choose .
On the Server Groups page, click Create Server Group.
In the Create Server Group dialog box, configure the parameters and click Create.
The following table describes the parameters that are relevant to this topic. You can use the default values for the other parameters. For more information, see Create and manage server groups.
Parameter
Description
Server Group Type
Specify a type of server group. In this example, Server is selected.
Server Group Name
Enter a name for the server group.
VPC
Select the VPC in which you want to create the server group. In this example, VPC1 is selected.
Backend Server Protocol
Select a backend protocol. HTTP is selected in this example.
Scheduling Algorithm
The scheduling algorithm. In this example, Weighted Round-robin is selected.
In the The server group is created dialog box, click Add Backend Server.
On the Backend Servers tab, click Add Backend Server.
In the Add Backend Server panel, select ECS01 and ECS02 and click Next.
Specify ports and weights for the backend servers and click OK.
Step 2: Create an ALB instance and add a listener
Log on to the ALB console.
On the Instances page, click Create ALB.
On the buy page, configure the following parameters.
The following table describes only some of the parameters. Other parameters use the default values. For more information, see Create and manage an ALB instance.
Region: the region in which you want to create the ALB instance. In this example, China (Hangzhou) is selected.
Network Type: the network type of the ALB instance. In this example, Internet is selected.
VPC: the VPC in which you want to create the ALB instance. In this example, VPC1 is selected.
Click Buy Now and complete the payment.
Return to the Instances page and click the ID of the ALB instance.
Click the Listener tab and then click Quick Create Listener.
In the Quick Create Listener dialog box, configure the parameters and click OK. In this example, an HTTP listener that listens on port 80 is created. The following table describes the parameters.
Parameter
Description
Listener Protocol
Select a listener protocol. In this example, HTTP is selected.
Listener Port
Enter a listener port. In this example, 80 is specified.
Server Group
Select a server group type in the left-side drop-down list and select a server group from the right-side drop-down list. In this example, the server group created in Step 1 is selected.
Step 3: Configure a CNAME record
In actual business scenarios, we recommend that you use CNAME records to map custom domain names to the domain name of your ALB instance.
In the left-side navigation pane, choose .
On the Instances page, copy the domain name of the ALB instance.
Perform the following steps to create a CNAME record:
NoteIf your domain name is not registered by using Alibaba Cloud Domains, you must add your domain name to Alibaba Cloud DNS before you can configure a DNS record. For more information, see Manage domain names.
Log on to the Alibaba Cloud DNS console.
On the Authoritative DNS Resolution page, find your domain name and click DNS Settings in the Actions column.
On the DNS Settings tab of the domain name details page, click Add DNS Record.
In the Add DNS Record panel, configure the parameters and click OK. The following table describes the parameters.
Parameter
Description
Record Type
Select CNAME from the drop-down list.
Hostname
Enter the prefix of the domain name. In this example, @ is entered.
NoteIf you use a root domain name, enter
@.DNS Request Source
Select Default.
Record Value
Enter the CNAME, which is the domain name of the ALB instance.
TTL Period
Select a time-to-live (TTL) value for the CNAME record to be cached on the DNS server. In this example, the default value is used.
Step 4: Create security groups
Create a security group in the ECS console. In this example, two security groups are created.
Use Security Group 1 as a blacklist
Add a Deny rule that denies access from specified IP addresses. In this example, a security group that denies access from the public IP address 121.XX.XX.12 is created. You can retain the default security group rules.
Action
Priority
Protocol Type
Port Range
Authorization Object
Deny
1
All
Destination: -1/-1
Source: 121.XX.XX.12
Use Security Group 2 as a whitelist
Add an Allow rule that allows access from specific IP addresses and a Deny rule that denies access from specific IP addresses. In this example, an Allow rule that allows access from the public IP address 121.XX.XX.12 and a Deny rule are created.
Action
Priority
Protocol Type
Port Range
Authorization Object
Allow
1
All
Destination: -1/-1
Source: 121.XX.XX.12
Deny
100
All
Destination: -1/-1
Source: 0.0.0.0/0
Log on to the ECS console.
In the left-side navigation pane, choose .
In the top navigation bar, select the region in which you want to create a security group. In this example, China (Hangzhou) is selected.
On the Security Groups page, click Create Security Group.
On the Create Security Group page, set the parameters in the Basic Information section.
Specify the following parameters. For more information about other parameters, see Create a security group.
Network: In this example, VPC is selected.
Security Group Type: In this example, Basic Security Group is selected.
On the Create Security Group page, set the parameters in the Access Rule section.
On the Inbound tab, click Add Rule to add rules based on the configurations of the rules in Security Group 1 and Security Group 2.
Click Create Security Group.
Step 5: Test access control before the ALB instance is added to a security group
Use Client03 and Client04 to test the availability of ECS01 and ECS02.
Log on to Client03 and run the
curl http://Custom domain namecommand. TheHello World! This is ECS01.packet is returned, as shown in the following figure. This packet indicates that Client03 can access the ALB instance.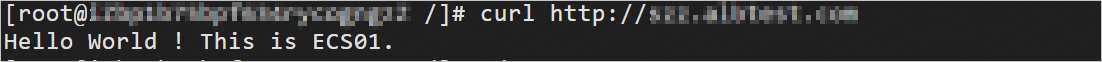
Log on to Client04 and run the
curl http://Custom domain namecommand. TheHello World! This is ECS02.packet is returned, as shown in the following figure, which indicates that Client04 can access the ALB instance.
Step 6: Add the ALB instance to the security groups and verify the result
Use Security Group 1 as a blacklist
Add the ALB instance to Security Group 1 created in Step 4: Create a security group to test whether the rules in Security Group 1 take effect on the ALB instance.
Log on to the ALB console.
In the top navigation bar, select the region of the ALB instance. In this example, China (Hangzhou) is selected.
On the ALB Instance page, click the ID of the ALB instance that you want to manage. On the instance details page, click the Security Groups tab.
On the Security Groups tab, click Create Security Group. In the Add ALB to Security Group dialog box, select Security Group 1 created in Step 4: Create security groups and click OK.
In the left-side panel, click the ID of the security group that you want to manage. You can click the Inbound Policies or Outbound Policies tab to view the security group rules.
The following table describes only the inbound security group rule that is relevant to this topic.
Action
Priority
Protocol Type
Port Range
Authorization Object
Deny
1
All
Destination: -1/-1
Source: 121.XX.XX.12
Add the ALB instance to the security group and test the result.
Log on to Client03 and run the
curl http://Custom domain namecommand. A response is received, as shown in the following figure, which indicates that access from Client03 is denied by the ALB instance.
Log on to Client04 and run the
curl http://Custom domain namecommand. TheHello World! This is ECS01.packet is returned, as shown in the following figure. This packet indicates that Client04 can access the ALB instance.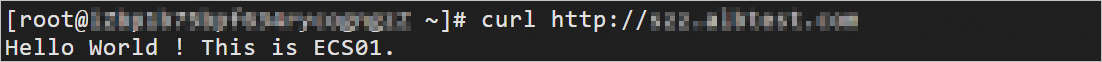
The results show that after the ALB instance is added to Security Group 1 which functions as a blacklist, the Deny rule of Security Group 1 denies access from the specified IP address to the ALB instance. IP addresses that are not specified in the Deny rule can access the ALB instance.
Use Security Group 2 as a whitelist
Add the ALB instance to Security Group 2 created in Step 4: Create security groups and test whether the rules of Security Group 2 take effect on the ALB instance.
Log on to the ALB console.
In the top navigation bar, select the region of the ALB instance. In this example, China (Hangzhou) is selected.
On the ALB Instance page, click the ID of the ALB instance that you want to manage. On the Instance Details tab, click the Security Groups tab.
On the Security Groups tab, click Create Security Groups. In the Add ALB to Security Group dialog box, select Security Group 2 created in Step 4: Create security groups and click OK.
In the left-side panel, click the ID of the security group that you want to manage. You can click the Inbound Policies or Outbound Policies tab to view the security group rules.
The following table describes only parameters that are relevant to this topic.
Action
Priority
Protocol Type
Port Range
Authorization Object
Yes
1
All
Destination: -1/-1
Source: 121.XX.XX.12
Deny
100
All
Destination: -1/-1
Source: All IPv4 Addresses (0.0.0.0/0)
Add the ALB instance to the security group and test the result.
Log on to Client03 and run the
curl http://Custom domain namecommand. TheHello World! This is ECS01.packet is returned, as shown in the following figure. This packet indicates that Client03 can access the ALB instance.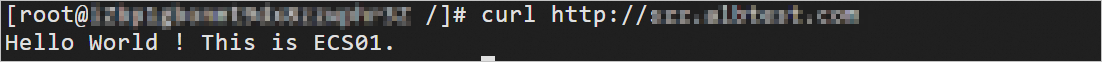
Log on to Client04 and run the
curl http://Custom domain namecommand. A response is received, as shown in the following figure. This packet indicates that access from Client04 is denied by the ALB instance.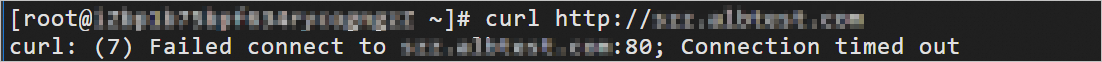
The test results show that after the ALB instance is added to Security Group 2 which functions as a whitelist, only IP addresses in the Allow rule can access the ALB instance.
References
Console documentation
For more information about how to add ALB instances to and remove ALB instances from security groups, see Add an ALB instance to a security group.
For more information about how to implement access control for ALB based on listeners and ports, see Use security groups to control access based on ports.
For differences between basic and advanced security groups, see Basic security groups and advanced security groups.
API
LoadBalancerJoinSecurityGroup: adds an ALB instance to a security group.
LoadBalancerLeaveSecurityGroup: removes an ALB instance from a security group.