Limitations in the new network architecture prevent some features of Alibaba Cloud Elasticsearch clusters from working as expected. To overcome these limitations, you can use PrivateLink together with Server Load Balancer (SLB) to establish a private connection between an Alibaba Cloud Elasticsearch cluster and other cloud resources, such as Elastic Compute Service (ECS) instances, elastic network interfaces (ENIs), elastic container instances (ECIs), or network resources at a specific IP address. This topic covers how to use Classic Load Balancer (CLB) or Network Load Balancer (NLB) and and PrivateLink to establish a private connection for Alibaba Cloud Elasticsearch.
Configuring a private connection is the only way to overcome the limitations that the new network architecture imposes on features such as X-Pack Watcher, reindex, Lightweight Directory Access Protocol (LDAP) authentication, and Active Directory (AD) user authentication.
Clusters created in or after October 2020 are deployed in the new network architecture and support private connections. Clusters created before October 2020 use the original network architecture and do not support private connections. This restriction also applies to clusters in Alibaba Finance Cloud and Alibaba Gov Cloud.
Application scenarios
Scenario 1: Access external service resources from an Elasticsearch cluster
An Elasticsearch cluster may need to access service resources in an external network for features such as Watcher alerts, LDAP authentication, or Active Directory authentication. You can configure a private connection between an Alibaba Cloud Elasticsearch cluster and an ECS instance. The ECS instance acts as a business server or a proxy server to forward network traffic.
The following table describes the applicable features and scenarios.
The following table describes the scenarios and features.
Feature | Scenario description | References |
Watcher | X-Pack Watcher monitors system information based on query conditions and provides an external alert service. | |
Alibaba Cloud ES security features | X-Pack supports cluster-level security settings such as LDAP and AD user authentication. | |
Custom plug-ins accessing external dictionaries | Custom plug-ins dynamically access dictionaries on an external network. | |
Cross-cluster reindex | Write data from a self-managed Elasticsearch cluster to an Alibaba Cloud Elasticsearch cluster by using cross-cluster reindex. |
Scenario 2: Migrate data between two Alibaba Cloud Elasticsearch clusters
You can use cross-cluster reindex to migrate data between two Alibaba Cloud Elasticsearch clusters. In this scenario, two Elasticsearch clusters are deployed in VPC_1 and VPC_2 respectively. You configure a private connection for the ES_1 cluster in VPC_1, connecting the endpoint in VPC_1 to the endpoint service in VPC_2 to establish a private connection between the two clusters.
The following table describes the scenarios and features.
Feature | Scenario description | References |
reindex | Write data from one Alibaba Cloud Elasticsearch cluster to another by using cross-cluster reindex. | Create private connections with NLB and PrivateLink between Alibaba Cloud Elasticsearch clusters |
Key concepts
Endpoint service: This is the service you want to make privately accessible. You manually create it and link it to your target service resources (e.g., an SLB instance forwarding to an ECS).
Endpoint: This represents the connection from your Elasticsearch cluster's VPC to an Endpoint Service. When you configure a private connection for an Alibaba Cloud Elasticsearch cluster, an endpoint is automatically created within the Elasticsearch cluster's network environment.
Create a private connection with CLB and PrivateLink between Elasticsearch and ECS
Prerequisites
An Alibaba Cloud Elasticsearch cluster was created in VPC_1 in or after October 2020. For more information, see Create an Alibaba Cloud Elasticsearch cluster.
An ECS instance was created in VPC_2, with the required applications deployed. For more information, see Custom launch.
The ECS instance serves as a backend server that receives requests forwarded by the SLB instance. When you create the ECS instance, select a region and zone that support PrivateLink. For supported regions, see Regions and zones that support PrivateLink.
The Alibaba Cloud ES, ECS, and SLB instances must be in the same zone and region.
Step 1: Create and configure an CLB instance
-
Log on to the CLB console.
Create an CLB instance that supports PrivateLink.
On the Instances page, click Create CLB.
On the purchase page, select the same region as the Alibaba Cloud Elasticsearch cluster, set Instance Type to Intranet, enter an instance name, and click Buy Now.
For more information, see Create and manage a CLB instance.
Configure the CLB instance.
On the Instances page, find the instance and click Configure Listener in the Actions column.
On the Configure Server Load Balancer page, configure the listener, backend servers, and health check, and then review the configuration.
For more information, see Configure a CLB instance and CLB listeners.
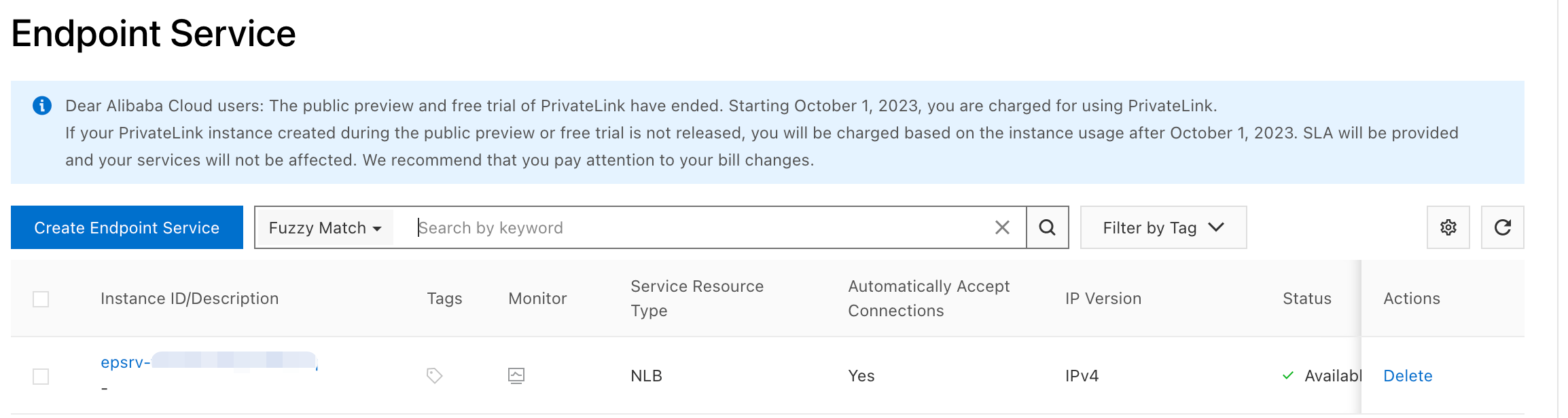
Step 2: Create an endpoint service
The private connection feature automatically creates an endpoint in the network environment of the Elasticsearch cluster. You only need to manually create an endpoint service in the environment of the ECS instance.
In the top navigation bar, select the same region as the CLB instance.
Click Create Endpoint Service.
On the Create Endpoint Service page, set Service Resource Type to CLB, select your CLB instance for Service Resource, configure other parameters as needed, and then click OK.
For more information, see Create an endpoint service.
Step 3: Configure a private connection for the Alibaba Cloud Elasticsearch cluster
Log on to the Alibaba Cloud Elasticsearch console.
In the left navigation menu, choose Elasticsearch Clusters.
Navigate to the target cluster.
In the top navigation bar, select the resource group to which the cluster belongs and the region where the cluster resides.
On the Elasticsearch Clusters page, find the cluster and click its ID.
In the left navigation menu, choose .
In the Network Settings section, click Edit next to Configure Private Connection.
In the Configure Private Connection panel, click +Add Private Connection.
In the Create Private Connection dialog box, set Associated Endpoint Service and Zone, select the acknowledgment checkbox, and then click OK.
You'll return to the Configure Private Connection panel. After the endpoint and the endpoint service are connected, the Endpoint Connection Status changes to Connected, indicating that communication is enabled between the Elasticsearch cluster in VPC_1 and client in VPC_2.
(Optional) View the endpoint domain name.
You can use the endpoint domain name for other service configurations, such as Watcher, single sign-on (SSO), and LDAP.
In the Configure Private Connection panel, click the target Endpoint ID.
On the Endpoint Connections tab, click the
 icon next to the endpoint ID to view the corresponding domain name.
icon next to the endpoint ID to view the corresponding domain name.
Create private connections with NLB and PrivateLink between Alibaba Cloud Elasticsearch clusters
This section describes how to use a NLB instance to connect an ES_1 cluster to an ES_2 cluster by mounting the IP address of the ES_2 cluster to the NLB instance. This method is typically used when two Alibaba Cloud Elasticsearch clusters cannot communicate because of network architecture limitations.
After a private connection is established, you can migrate data from the ES_2 cluster to the ES_1 cluster.
Alibaba Cloud NLB supports IP address mounting. For more information, see Functions and features.
Prerequisites
Two Alibaba Cloud Elasticsearch clusters are created in the same region and zone.
The selected region and zone support PrivateLink. For supported regions, see Regions and zones that support PrivateLink.
Step 1: Create and configure an NLB instance
An NLB instance receives client requests and forwards them to backend servers based on listening rules.
Create an NLB instance.
Log on to the NLB console.
On the Instances page, click Create NLB.
On the purchase page, select the same region as the Elasticsearch clusters, set the network type to Internal-facing, and select the zone.
For more information, see Create and manage an NLB instance.
Click Create Now.
Create an NLB server group.
A server group routes client requests to backend servers. NLB verifies backend server availability through health checks.
Go to the NLB Server Groups page.
On the Server Groups page, click Create Server Group.
In the dialog box, set Server Group Type to IP, enter a name, and select the VPC associated with the ES_2 cluster.
Add the ES_2 cluster as a backend server.
Add the private IP address and port of the ES_2 cluster to the server group.
In the Actions column for the server group, click Modify Backend Server.
On the Backend Servers tab, click Add Backend Server.
In the Add Backend Server wizard, select the ES_2 cluster and click Next.
Specify the port. For example, reindex requires port 9200.
Click OK.
Add a listener.
Log on to the NLB console.
On the Instances page, click Create Listener in the Actions column for the NLB instance.
Set the listener protocol to TCP and the listener port to 9200, and then click Next.
Set Server Group to IP, select the backend server group, and click Next.
Click Submit.
Step 2: Create an endpoint service
PrivateLink automatically creates an endpoint in the network environment of the Elasticsearch cluster. You only need to manually create an endpoint service in the environment of the other Elasticsearch cluster.
Click Create Endpoint Service.
Configure the endpoint service with the following settings:
Parameter
Description
Region
Select the same region as the Elasticsearch clusters.
Service Resource Type
Select NLB.
Service Resource
Selecy the NLB instance that you created.
Service Payer
You can select either option.
For more information, see Create and manage endpoint services.
Click OK.
After the endpoint service is created, it is attached to the NLB instance and appears in the Endpoint Service section.
Step 3: Configure a private connection on the ES_1 cluster
Alibaba Cloud Elasticsearch automatically creates an endpoint in the network environment of the ES_1 cluster to connect to the endpoint service.
Log on to the Alibaba Cloud Elasticsearch console.
In the left navigation menu, choose Elasticsearch Clusters.
Navigate to the target cluster.
In the top navigation bar, select the resource group to which the cluster belongs and the region where the cluster resides.
On the Elasticsearch Clusters page, find the cluster and click its ID.
In the left navigation menu, choose .
In the Network Settings section, click Edit next to Configure Private Connection.
In the Configure Private Connection panel, click +Add Private Connection.
In the dialog box, select the endpoint service you created, set Zone, and click OK.
After the endpoint and the endpoint service are connected, the Endpoint Connection Status changes to Connected, indicating that the ES_1 and ES_2 clusters are connected.
(Optional) View the domain name of the endpoint.
You can use the endpoint domain name and add it to a whitelist for service configurations such as Watcher, SSO, and LDAP.
In the Configure Private Connection panel, click the ID of the destination Endpoint ID.
On the Endpoint Connections tab, click the
 icon next to the destination endpoint ID to view the domain name that corresponds to the endpoint.
icon next to the destination endpoint ID to view the domain name that corresponds to the endpoint.
(Optional) Step 4: Verify connectivity by using reindex
You can use reindex to migrate an index from the ES_2 cluster to the ES_1 cluster to verify network connectivity.
Configure a reindex whitelist in the YML file of the ES_1 cluster.
On the details page of the ES_1 cluster, choose .
In the YML File Configuration section, click Modify Configuration in the upper-right corner and add the following entry:
reindex.remote.whitelist: ["Domain name of the endpoint:9200"]
Prepare the data to migrate in the ES_2 cluster. Then, create an index in the ES_1 cluster and run the following reindex command:
POST _reindex { "source": { "remote": { "host": "http://ep-bp1i4db71e6adaa29718-cn-hangzhou-i.epsrv-bp1fm3v8kc2qr2td6lrm.cn-hangzhou.privatelink.aliyuncs.com:9200", "username": "Username", "password": "Password" }, "index": "myindex" }, "dest": { "index": "myindex2" } }Category
Parameter
Description
source
host
The access address of the PrivateLink endpoint service. The address must contain the protocol, endpoint domain name, and port number. Example:
https://<Endpoint domain name>:9200.username
Optional. The default username for an Alibaba Cloud Elasticsearch cluster is elastic.
password
The password for the username.
index
The name of the source index in the remote cluster.
query
Optional. Use a query to specify the data to migrate. For more information, see Reindex API.
dest
index
The name of the destination index in the local cluster.
Verify the migration results.
In the ES_1 cluster, check whether the data from the ES_2 cluster was successfully migrated. You can run the following command to verify:
GET myindex2/_countCompare the document count with the source index in the ES_2 cluster to confirm that the migration completed successfully.