If you want to manage outbound traffic from resources such as an Elastic Compute Service (ECS) instance or elastic container instance in a virtual private cloud (VPC) to the Internet over a NAT gateway, you can enable a NAT firewall for the NAT gateway and configure an access control policy to perform fine-grained management on traffic from internal-facing resources to the Internet.
When internal-facing resources in a VPC directly access the Internet over a NAT gateway, risks such as unauthorized access, data leaks, and traffic attacks may occur. You can create a NAT firewall to allow only the required traffic by specifying items such as the source address, destination address, port, protocol, and application. This effectively restricts unauthorized access from internal-facing resources to the Internet.
After you enable a NAT firewall for a NAT gateway, the NAT firewall manages all outbound traffic from the internal-facing resources in a VPC to the NAT gateway. The resources include resources that are deployed in the same VPC and resources across VPCs.
Prerequisites
A NAT firewall is created and enabled. For more information, see NAT firewalls.
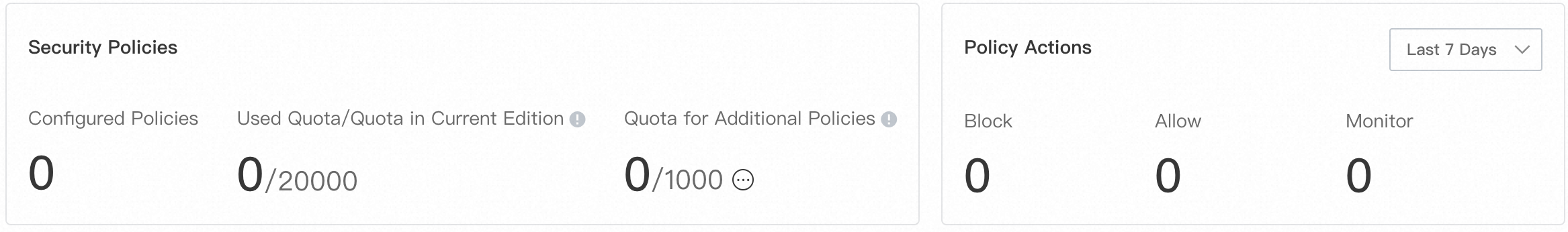
The quota for access control policies is sufficient. You can view the quota for access control policies on the page. For more information about how to calculate quota usage, see Overview of access control policies.
If the quota is insufficient, you can click Increase Quota to increase the value of Quota for Additional Policy. For more information, see Purchase Cloud Firewall.
If you want to specify multiple items as source or destination addresses, you can create an address book. For more information, see Manage address books.
Procedure
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose .
On the NAT Border page, find the NAT gateway for which you want to create an access control policy and click Create Policy.
The NAT gateways within the current Alibaba Cloud account are automatically synchronized to Cloud Firewall.

In the Create Policy - NAT Border panel, configure the following parameters and click OK.
Parameter
Description
Source Type
The initiator of network traffic. You must select a source type and enter source addresses from which network traffic is initiated based on the selected source type.
If you set Source Type to IP, specify one or more CIDR blocks, such as 192.168.0.0/16. You can specify up to 2,000 CIDR blocks. Separate multiple CIDR blocks with commas (,).
If you enter multiple CIDR blocks at a time, Cloud Firewall automatically creates an address book that includes the entered CIDR blocks. When you save the access control policy, Cloud Firewall prompts you to specify a name for this address book.
If you set Source Type to Address Book, make sure that an IP address book is configured. For more information about how to create an address book, see Manage address books.
Source
Destination Type
The receiver of network traffic. You must select a destination type and enter destination addresses to which network traffic is sent based on the selected destination type.
If you set Source Type to IP, specify one or more CIDR blocks, such as 192.168.0.0/16. You can specify up to 2,000 CIDR blocks. Separate multiple CIDR blocks with commas (,).
If you enter multiple CIDR blocks at a time, Cloud Firewall automatically creates an address book that includes the entered CIDR blocks. When you save the access control policy, Cloud Firewall prompts you to specify a name for this address book.
If you set Source Type to Address Book, make sure that an IP address book is configured. For more information about how to create an address book, see Manage address books.
If you set Destination Type to Domain Name, select a domain name identification mode. Valid values:
FQDN-based Dynamic Resolution (Extract Host and SNI Fields): If you want to manage HTTP, HTTPS, SMTP, SMTPS, and SSL traffic, we recommend that you select this mode.
DNS-based Dynamic Resolution: If you want to manage traffic except HTTP, HTTPS, SMTP, SMTPS, and SSL traffic, we recommend that you select this mode.
ImportantThis mode does not support wildcard domain names.
FQDN and DNS-based Dynamic Resolution (Support for HTTP, HTTPS, SSL, SMTP, and STMPS): If you want to manage HTTP, HTTPS, SMTP, SMTPS, and SSL traffic, but specific or all traffic does not contain the HOST or SNI field, we recommend that you use this mode.
ImportantThis mode takes effect only if the ACL Engine Management mode is Strict.
If you set Destination Type to Region, select one or more locations of traffic destinations for Destination. You can select one or more locations in or outside China.
Destination
Protocol Type
The transport layer protocol. Valid values: TCP, UDP, ICMP, and ANY. If you do not know the protocol type, select ANY.
Port Type
The port type and port number of the destination.
If you set Port Type to Port, enter port ranges. Specify a port range in the Port number/Port number format. Examples: 22/22 or 80/88. Separate multiple port ranges with commas (,). You can enter up to 2,000 port ranges.
If you enter multiple port ranges, Cloud Firewall automatically creates an address book that includes the entered port ranges. When you save the access control policy, Cloud Firewall prompts you to specify a name for this address book.
If you set Port Type to Address Book, make sure that a port address book is configured. For more information about how to create an address book, see Manage address books.
Port
Application
The application type of the traffic.
If you set the Domain Name Identification Mode parameter to DNS-based Dynamic Resolution, you can select all applications.
If you set the Domain Name Identification Mode parameter to FQDN-based Dynamic Resolution (Extract Host and SNI Fields), you can select only HTTP, HTTPS, SMTP, SMTPS, or SSL.
If you set the Domain Name Identification Mode parameter to FQDN and DNS-based Dynamic Resolution, you can select HTTP, HTTPS, SMTP, SMTPS, or SSL.
Action
The action on the traffic if the traffic meets the preceding conditions that you specify for the access control policy. Valid values:
Allow: The traffic is allowed.
Deny: The traffic is denied, and no notifications are sent.
Monitor: The traffic is recorded and allowed. You can observe the traffic for a period of time and change the policy action to Allow or Deny based on your business requirements.
Description
The description of the access control policy. Enter a description that can help identify the policy.
Priority
The priority of the access control policy. Default value: Lowest. Valid values:
Highest: The access control policy has the highest priority.
Lowest: The access control policy has the lowest priority.
Policy Validity Period
The validity period of the access control policy. The policy can be used to match traffic only within the validity period.
Status
Specifies whether to enable the policy. If you turn off Status when you create an access control policy, you can enable the policy in the list of access control policies.
Configure the access control engine mode
After an access control policy is created, the access control engine mode of the NAT firewall is Loose Mode by default. In this mode, the traffic whose application type or domain name is identified as Unknown is automatically allowed to avoid impacts on your workloads. You can change the mode to Strict Mode based on your business requirements.
On the page, click ACL Engine Management in the upper-right corner of the access control policy list.
In the ACL Engine Management - NAT Firewall panel, find the NAT gateway whose engine mode you want to change and click Modify in the Engine Mode column.
In the Change Engine Mode dialog box, configure the Engine Mode parameter and click OK.
Strict Mode: After you enable the strict mode, the traffic whose application type or domain name is identified as Unknown is matched against all policies that you configured. If you configured a Deny policy, this type of traffic is denied.
Loose Mode: After you enable the loose mode, traffic whose application type or domain name is identified as Unknown is allowed. This ensures normal access.
View the hit details about an access control policy
After your service runs for a period of time, you can view the hit details about an access control policy in the Hits/Last Hit At column in the list of access control policies.
You can click the number of hits to go to the Log Audit page to view traffic logs. For more information, see Log audit.
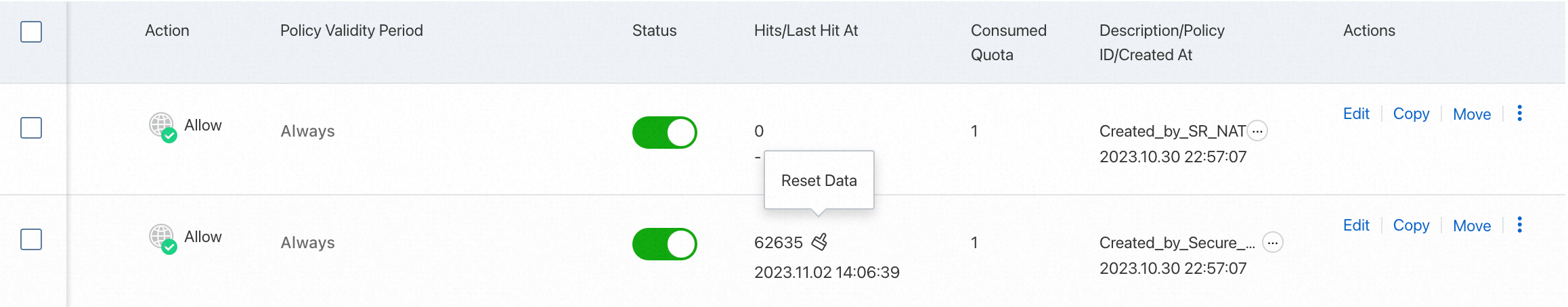
Related operations
After you create an access control policy, you can click Modify, Delete, or Copy in the Actions column of the policy. You can also click Move to change the priority of the policy. After you change the priority of the policy, the priorities of access control policies that have lower priorities decrease.
After you delete a policy, Cloud Firewall no longer manages traffic on which the policy is originally in effect. Proceed with caution.
References
For more information about how to manage traffic from internal-facing assets to a specific domain name, see Configure a policy to allow only internal-facing servers to access a specific domain name.
For more information about how access control policies work, see Overview of access control policies.
For more information about how to configure an access control policy, see Configure access control policies.
For more information about how to view and manage IP address books, port address books, and domain address books in access control policies, see Manage address books.
For more information about how to configure and use an access control policy, see FAQ about access control policies.