建立ACK託管叢集時,您只需配置Worker節點,Master節點由阿里雲Container Service建立並託管,降低營運成本,讓您更聚焦於業務應用。本文介紹如何通過控制台、API、Terraform、SDK以及CLI等方式建立ACK託管叢集。
在開始建立ACK叢集之前,建議您已瞭解Kubernetes基礎知識、Container ServiceACK、ACK託管叢集等基礎資訊。
如果您是首次使用ACK託管叢集,可參見通過ACK快速搭建魔方遊戲應用開始新手入門體驗。體驗結束後請及時釋放資源,避免產生預期外費用。
規劃與設計
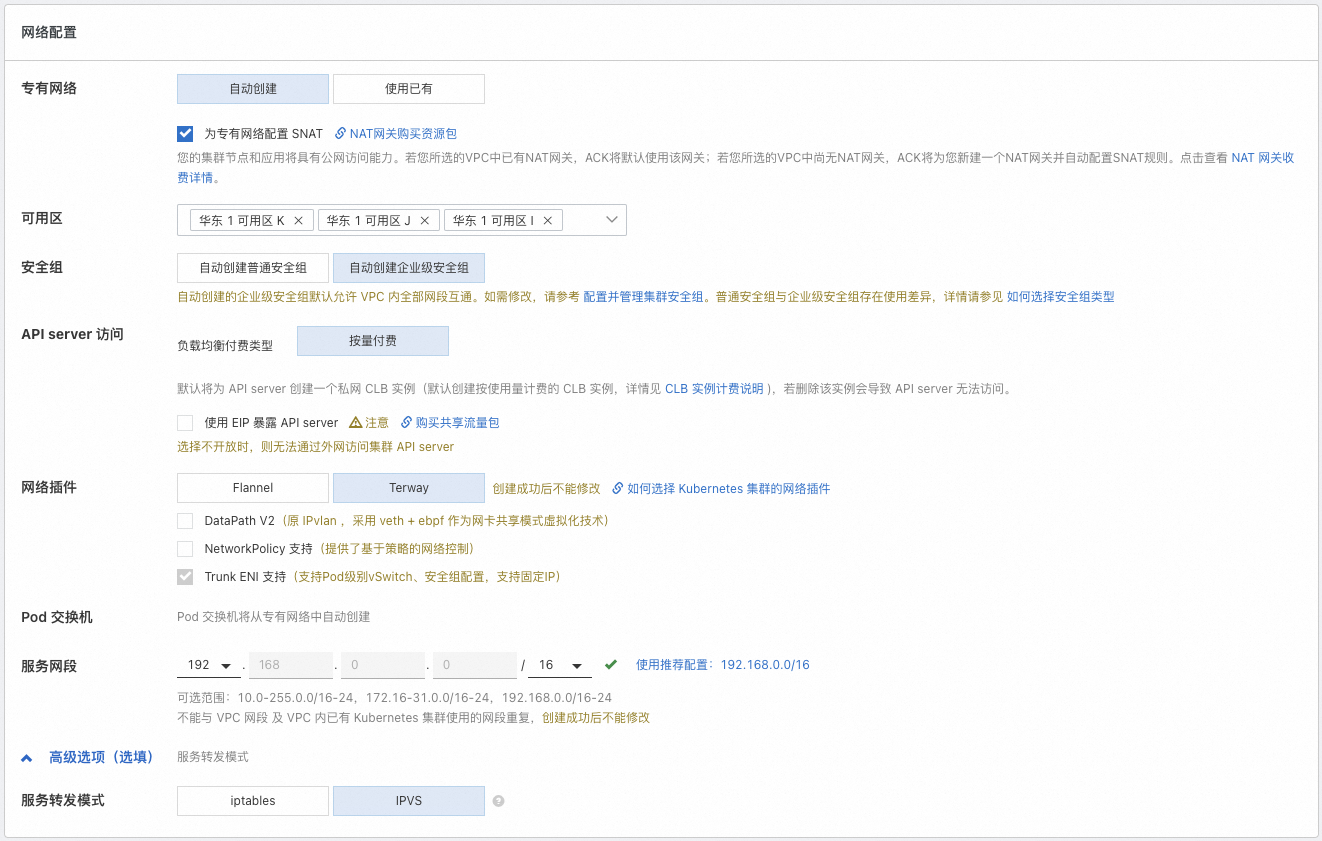
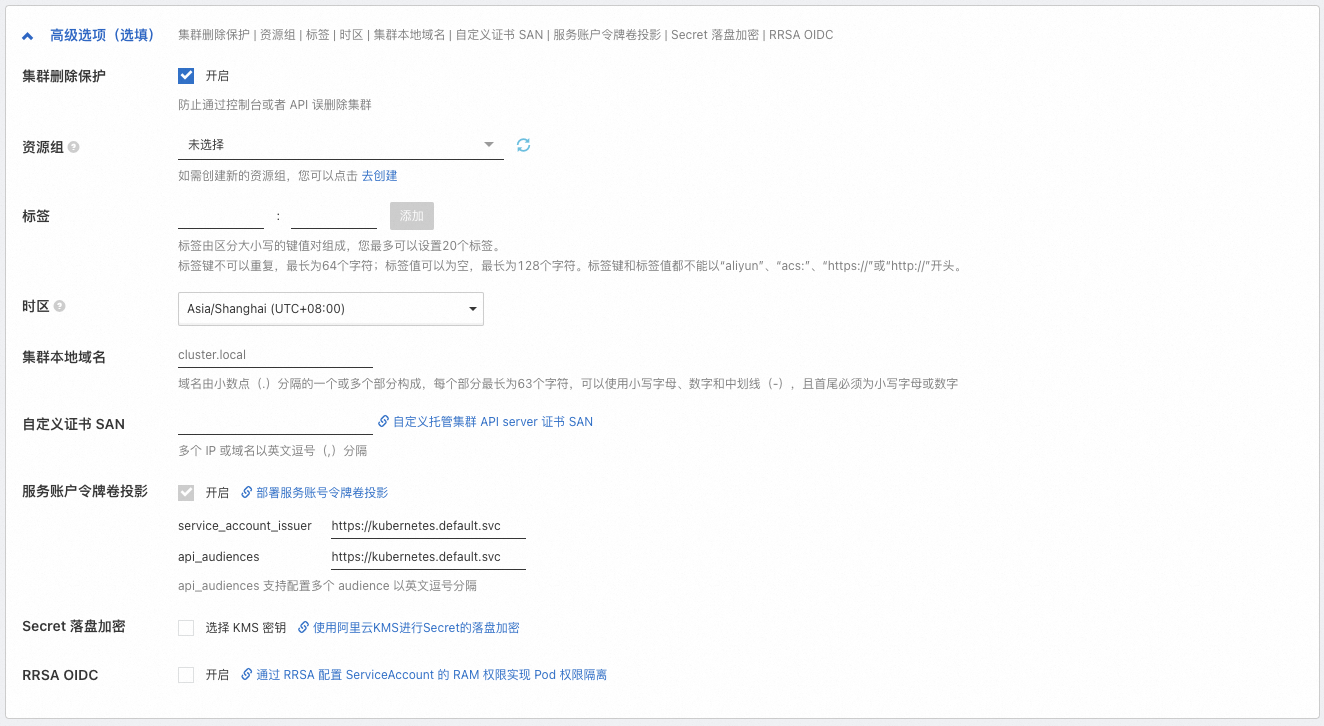
建立叢集前,請根據業務需求規劃並設計叢集,以確保叢集能夠穩定、高效且安全地運行。大多數配置項在叢集建立後仍可調整,但部分配置項建立後不支援更改,尤其是叢集可用性、叢集網路相關的配置。規劃時,請確保已考慮以下因素。
分類 | 說明 |
部署位置 |
|
版本和規格 |
|
網路規劃 |
|
準備工作
建立叢集前,請確保您已經開通Container ServiceACK、為您的阿里雲帳號或RAM帳號授予了ACK系統服務角色(ACK需要這些許可權來調用相關服務或執行叢集操作),並且開通了相關雲產品(例如VPC、負載平衡、NAT Gateway等)。具體操作,請參見快速建立ACK託管叢集。
建立叢集過程中涉及負載平衡CLB等按量資源的購買,請確保您的賬戶餘額充足,避免因為欠費導致停機。
建立叢集
ACK支援通過控制台、API、SDK、Terraform以及CLI方式建立叢集。
控制台
API
Terraform
SDK
CLI
後續操作
應用部署:建立並管理工作負載,包括Deployment、StatefulSet、Job等,請參見建立工作負載。
服務發現與網路管理
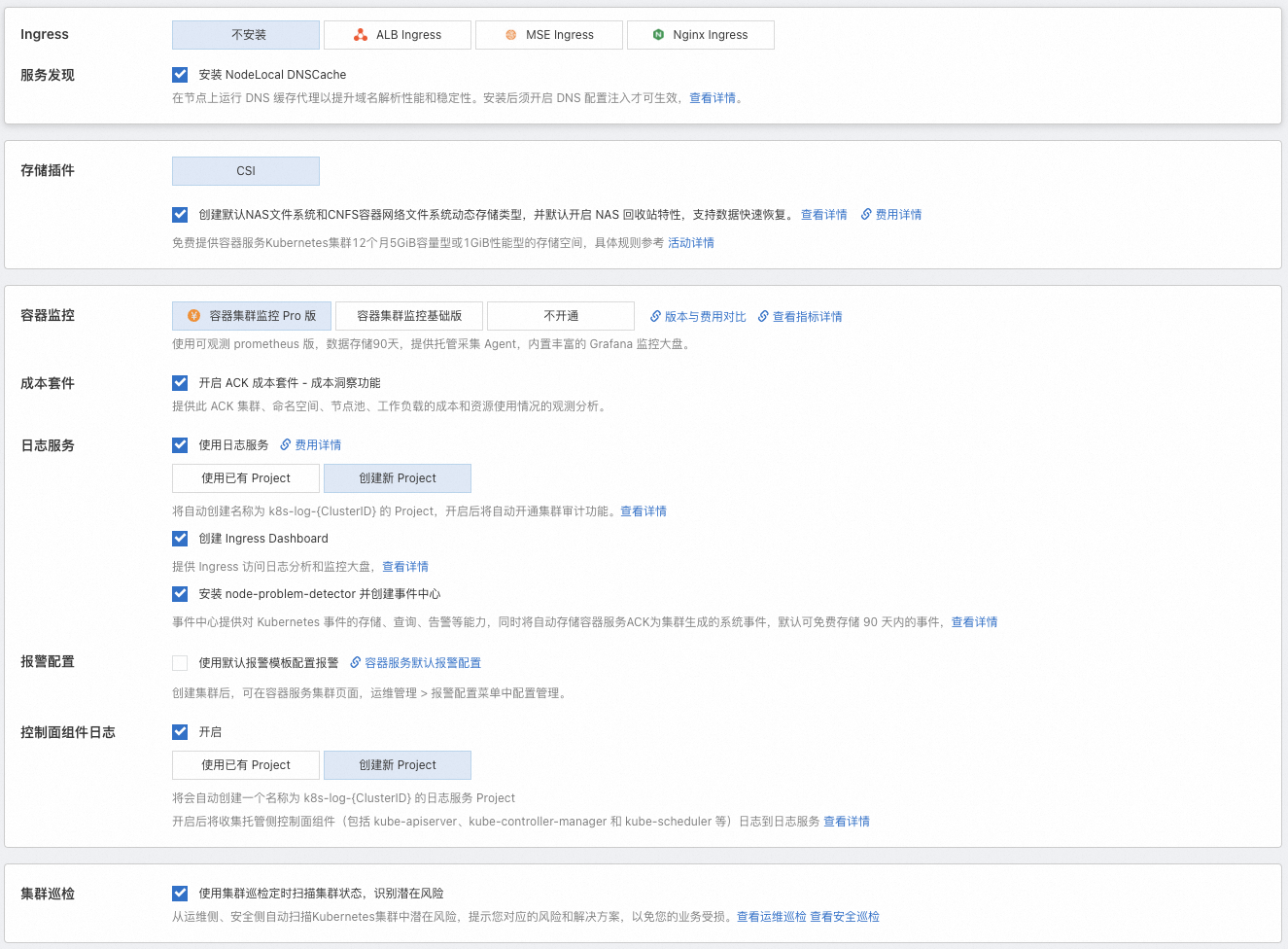
可觀測配置:實現叢集日誌收集和監控警示,便於叢集診斷和狀態觀測。請參見可觀測性瞭解ACK在基礎設施、容器、工作負載等維度提供的可觀測方案。
儲存:基於CSI外掛程式實現應用資料持久化儲存、敏感和配置資料存放區、儲存資源動態供應等儲存需求。
Auto Scaling配置:如業務資源需求不易預測或有周期性變化(例如Web應用、遊戲服務、線上教育等),推薦啟用Auto Scaling,包括工作負載伸縮(HPA、CronHPA、VPA等)和計算資源伸縮(節點自動調整、節點即時彈性等)。
精細化授權
如需對基礎資源層(ACK依賴的雲產品)和叢集內部資源(Kubernetes資來源物件)進行更細粒度的許可權控制,ACK提供基於阿里雲RAM和Kubernetes原生RBAC機制的多種許可權管理方案,請參見授權。
配額與限制
如叢集規模較大或帳號資源較多,請遵循使用ACK叢集時涉及的配額與限制。詳細資料,請參見配額與限制。
使用限制:包括ACK配置限制(例如帳號餘額等)和單叢集容量限制(單叢集內不同Kubernetes資源的最大容量)。
配額限制與提升方式:ACK叢集配額限制和ACK依賴雲產品(例如ECS、VPC等)的配額限制。如需提升配額,請參見文檔擷取提升方式。
常見問題
如在使用ACK叢集的過程中遇到問題,可參見故障排除、常見問題進行自排查。
可以建立一個0節點的叢集嗎?
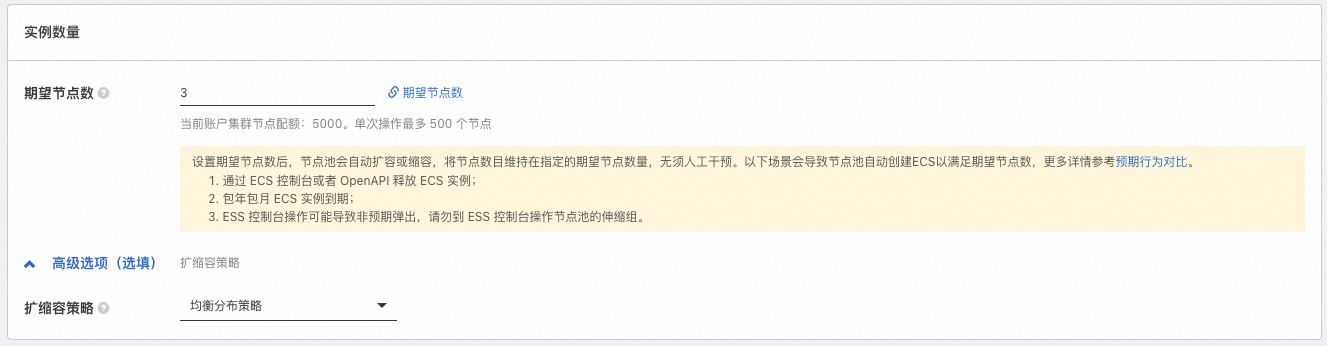
可以。如需跳過節點建立,或在叢集建立後再將已購買的ECS執行個體添加到叢集中,可在配置過程中將期望節點數配置為0,即配置叢集中的執行個體數量為0,並完成其他必選項的配置,後續再參見建立和管理節點池完成節點池的配置更新或建立更多節點池。如需將已購買的ECS執行個體添加到叢集,請參見添加已有節點。
已購買的ECS執行個體如何添加到叢集中?
ACK支援將已有ECS執行個體手動或自動添加到節點池中。自動添加的方式會根據節點池當前的作業系統替換該ECS執行個體原有的作業系統,原系統硬碟會被釋放。如需保留ECS執行個體作業系統,請選擇手動添加的方式。相關注意事項及操作步驟,請參見添加已有節點。
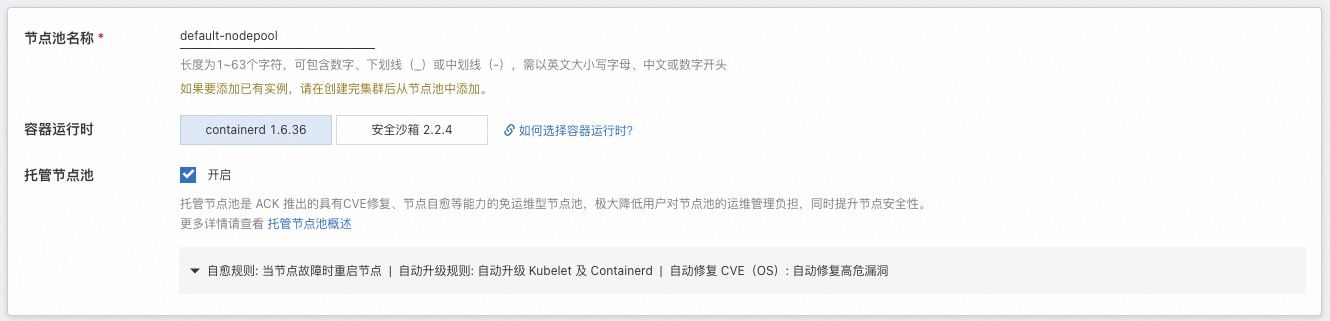
建議待添加ECS執行個體與待加入的節點池具有相同或類似配置(例如付費類型、磁碟配置、執行個體規格等),便於後續節點的統一管理。
已購買的隨用隨付的ECS執行個體可以添加到訂用帳戶的節點池中嗎?
可以,您可以參見添加已有節點完成操作。但當節點池付費類型為訂用帳戶時,後續節點池擴容出的節點均為訂用帳戶類型。建議您建立不同的節點池,納管不同類型(例如付費類型、磁碟配置、執行個體規格等)的節點。具體操作,請參見建立和管理節點池。
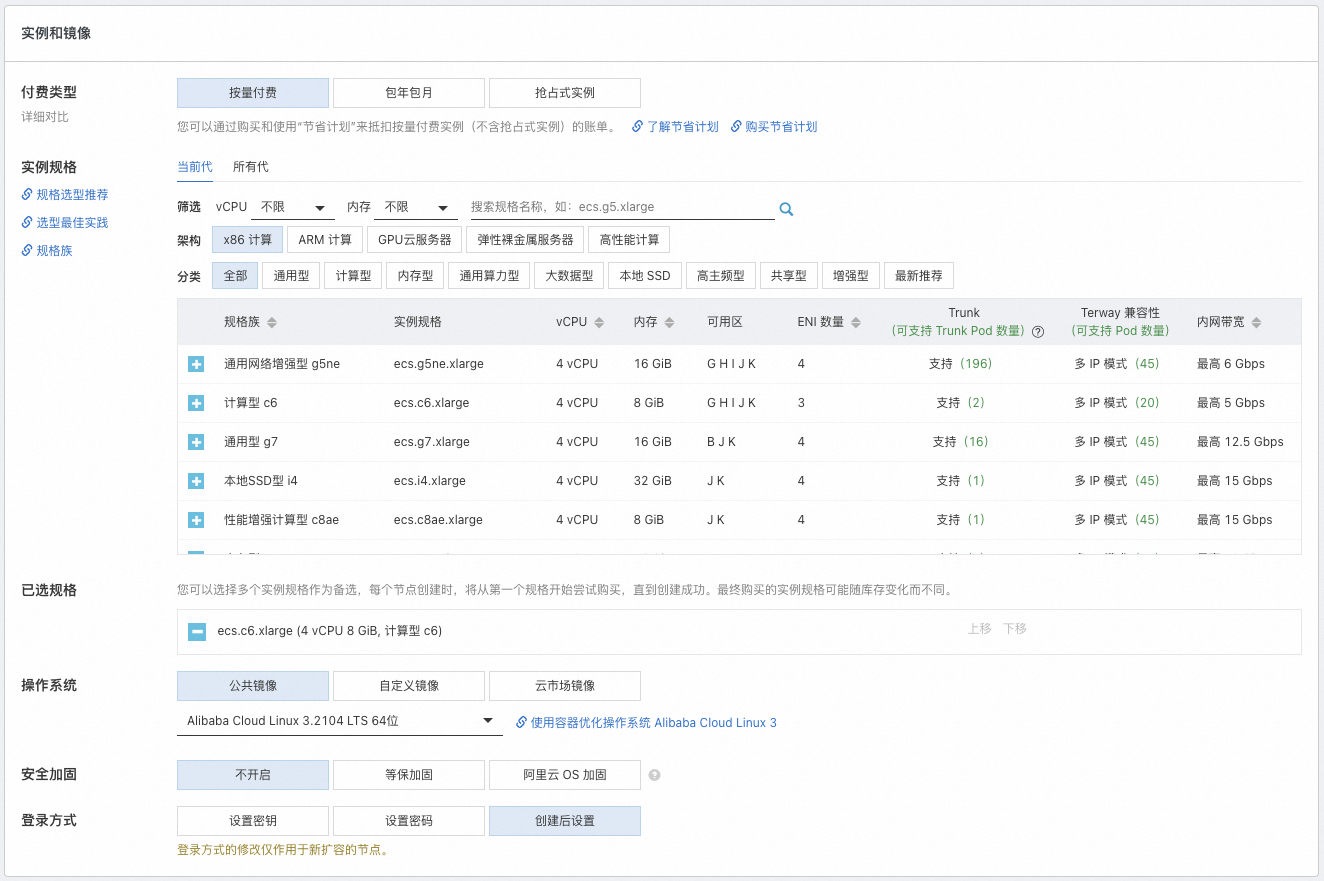
為什麼剛建立好的叢集就提示Pod數量不足?
可能是以下原因。
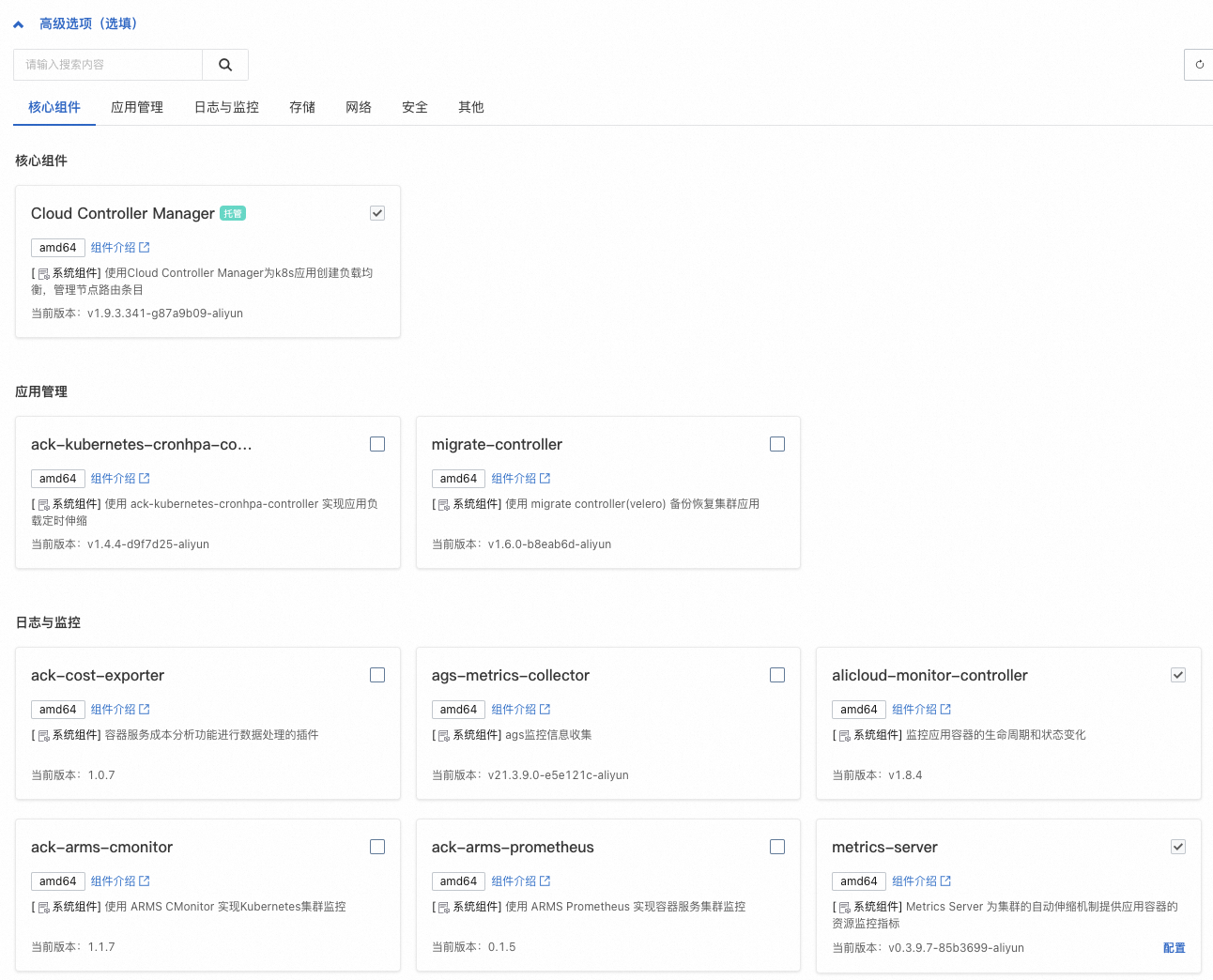
組件佔用:叢集組件會以Pod的形式存在,佔用節點資源。部分組件可能會採用多副本形式。如果您建立叢集配置組件時啟用的功能較多,可能會佔用節點較多的Pod數量。
執行個體規格較小:Terway模式下,單節點支援的最大Pod數依賴於ECS執行個體規格類型系列所提供的彈性網卡(ENI)數量。雖然節點支援的最大Pod數跟CPU和記憶體並不是直接的線性關係,但通常較小規格的ECS執行個體支援的ENI數量較少,單節點的Pod限額也較小。
當節點Pod數量達到上限時,新Pod將調度失敗,影響服務效能。您可以通過擴容節點池以增加更多可用的節點、升配節點以提升單節點最大Pod數等方式增加可使用的Pod數,請參見調整可使用的節點Pod數量。
購買後查看節點可用的CPU和記憶體資源,為什麼比購買時的執行個體規格定義的少?
ACK需要佔用一定的節點資源來為kube組件和system進程預留資源,從而保證OS核心和系統服務、Kubernetes守護進程的正常運行。這會導致節點的資源總數(Capacity)與可分配的資源數(Allocatable)之間存在差異。詳細資料,請參見節點資源預留策略。
相關文檔
使用ACK叢集過程中,操作不當可能會導致業務故障,請參見使用須知及高危風險操作說明。
關於如何串連叢集,請參見擷取叢集KubeConfig並通過kubectl工具串連叢集。
如需在ACK叢集中跨域拉取海外源容器鏡像,請參見使用GA實現ACK跨域加速拉取容器鏡像。
如有任何產品建議或疑問,請聯絡我們。