This topic describes how to connect a corporate OpenLDAP as an inbound identity provider. This lets you synchronize OpenLDAP organizations and accounts to IDaaS. You can also use OpenLDAP identities to log on to IDaaS or applications.
About OpenLDAP
OpenLDAP is an open source implementation of the Lightweight Directory Access Protocol (LDAP). It is often used to manage resources in an enterprise, such as users, computers, and networks. Because OpenLDAP is widely used, it is often referred to simply as LDAP.
You can use the network endpoint feature to synchronize data from LDAP and delegate authentication to LDAP without opening public ports.
Connect to OpenLDAP
Step 1: Connect to OpenLDAP
Log on to the IDaaS console. Find the IDaaS instance that you want to manage and click Manage in the Actions column.
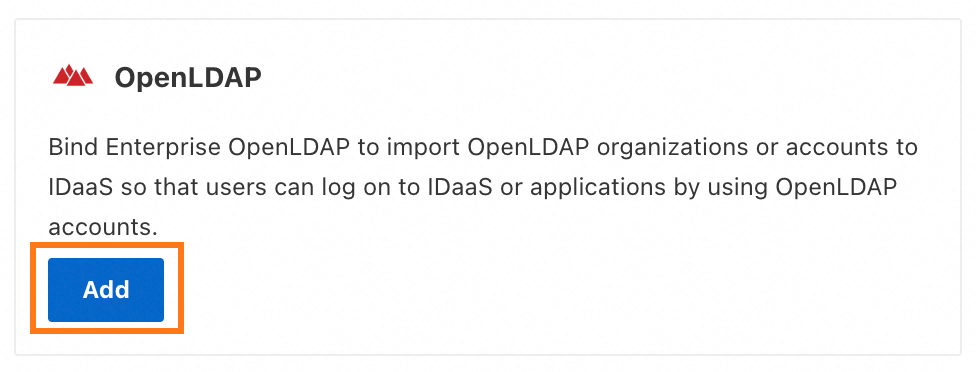
In the navigation pane on the left, choose . Click Add Outbound. In the provider list, find OpenLDAP and click Add.
On the Connect to OpenLDAP panel, configure the following parameters.
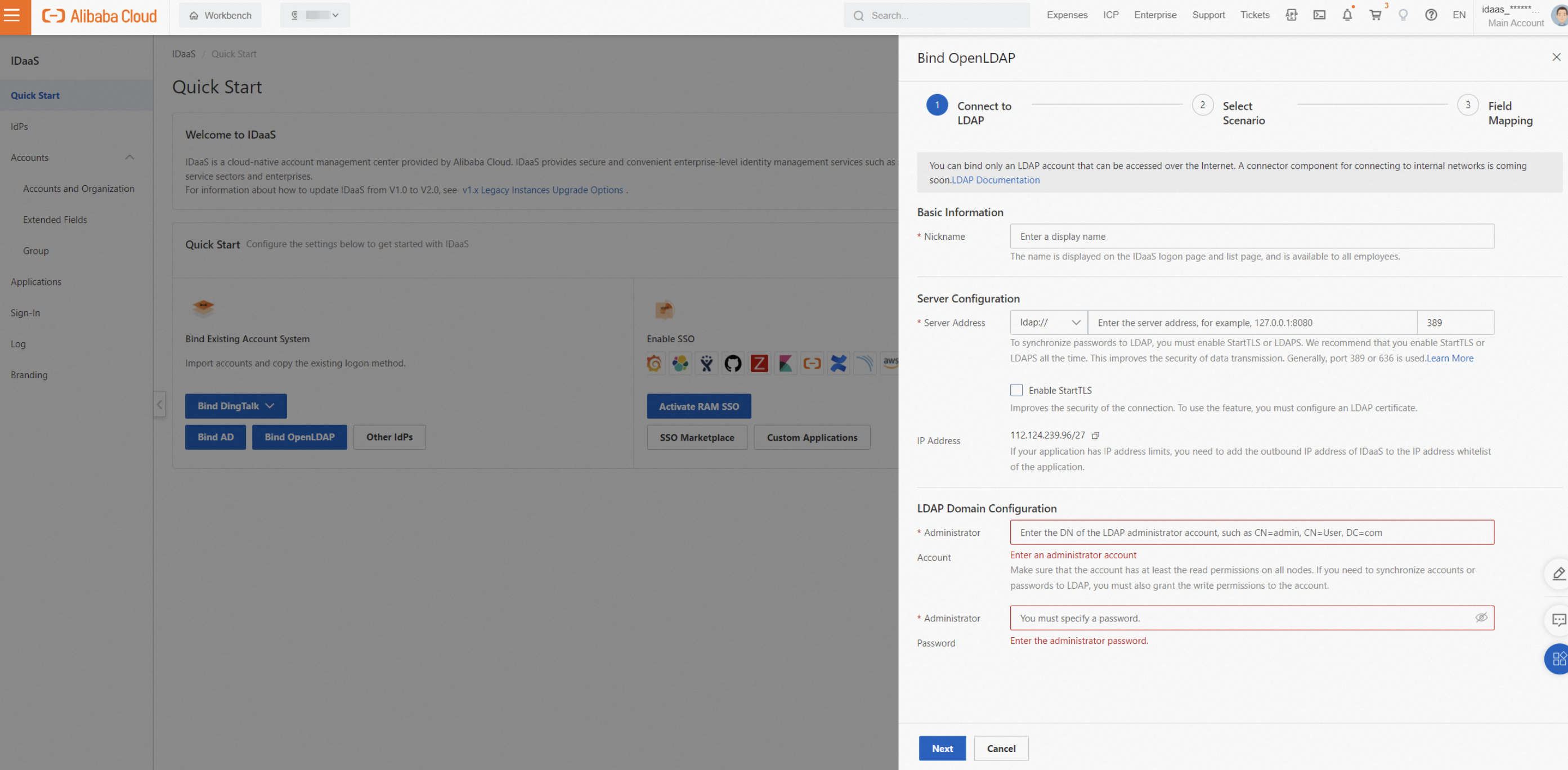
Display Name: The name displayed to users when they log on to and use IDaaS.
Network Access Endpoint: To allow requests only from IDaaS, configure an IP whitelist on your LDAP server. A shared endpoint uses a shared, fixed public outbound IP address. A dedicated endpoint uses a dedicated private outbound IP address and a custom public outbound IP address. A dedicated endpoint allows IDaaS to access your Alibaba Cloud VPC over a private network. This lets you access your LDAP server without opening a public port. For more information, see Network endpoints.
Server address: The address of the LDAP server. The default port for LDAP is 389, for example, 127.0.0.1:389. Port 636 is typically used if LDAPS or StartTLS is enabled.
Enable StartTLS: Enabling this feature significantly improves connection security. We recommend that you enable this option. For more information about how to enable this feature, see LDAP security configuration.
Administrator Account: IDaaS uses this LDAP administrator account to read LDAP information for data synchronization and delegated authentication. The account requires at least read permissions. The account must be in the Distinguished Name (DN) format, such as cn=admin,ou=Technical Department,dc=example,dc=com.
Administrator Password: The logon password for this account.
Step 2: Select a scenario
In this step, you can select the features that you want to implement with LDAP.

Basic configuration
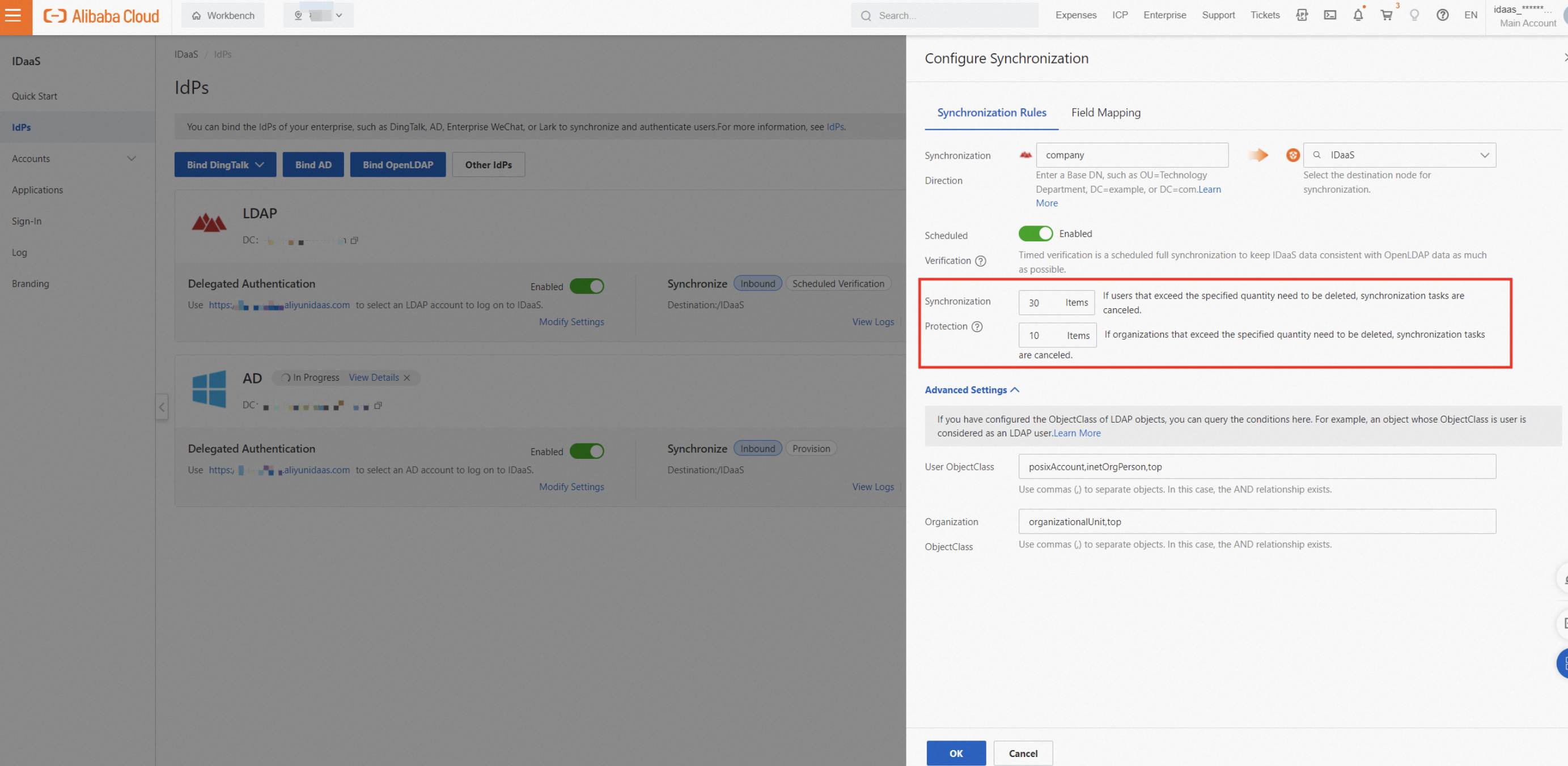
Synchronization Direction: User and organization data is imported from the selected LDAP source node to the specified IDaaS node. For Source Node, you must enter the DN of the LDAP node. The DN of the LDAP root node is typically dc=example,dc=com, which is your domain.
Scheduled Verification: LDAP does not support queries for incremental data. IDaaS automatically performs a full synchronization of all data under the LDAP source node every morning.
You can set mapping identifiers in the field mapping settings. This process matches a field in an IDaaS account, such as a mobile phone number, with a field in an LDAP user account. If a match is found, the accounts are linked, and the IDaaS account is updated. Otherwise, a new IDaaS account is created.
To synchronize data immediately, you can manually trigger a full synchronization.
IDaaS has a built-in synchronization protection feature. If more than 30 accounts or 10 organizations are scheduled for deletion, the synchronization task is automatically canceled. This feature prevents accidental data loss. We recommend that you adjust the synchronization protection settings based on the size of your enterprise.
If a single account record fails to import, it does not affect the import of other records.
You can view failure information in the Synchronization Logs.
Delegated Authentication: Users can log on to IDaaS using their LDAP username and password.
Automatic Password Update: When a user logs on to IDaaS through LDAP delegated authentication, if the IDaaS account does not have a password, the password is set to the password of the LDAP account. The LDAP password must meet the IDaaS password policy requirements. Otherwise, the password cannot be updated automatically.
Advanced settings
User/Organization
ObjectClass: You can useObjectClassto define which object types are users or organizations. For example, an object in the query results whereObjectClass=useris treated as a user.ImportantLDAP has flexible customization capabilities. If you customize the
ObjectClassfor users or organizations, you must ensure that theObjectClassis consistent. This ensures that the data synchronized toIDaaSmeets your expectations.User logon identity: When a user logs on to IDaaS using LDAP delegated authentication, IDaaS uses these attributes to find the user in LDAP and verify the password. If the password is correct, the user is allowed to log on to IDaaS. You can enter multiple attributes separated by commas (,). This creates an OR condition, which means the user can log on with any of the specified attributes. You must ensure that all attributes correspond to the same LDAP user. Otherwise, the logon fails.
User
filter: To synchronize only specific users from different organizations to IDaaS, you can define a customfilterstatement. Only users who meet the conditions are synchronized. By default, thefilterstatement includes an AND condition forObjectClass. Click View Details to see the complete statement. For more information about the syntax and common use cases, see Filter.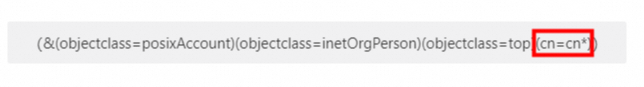
Step 3: Configure field mappings
If you have historical data in IDaaS, you can link LDAP users and organizations to existing IDaaS accounts and organizations. You can also use data from specific LDAP fields for IDaaS accounts. For example, you can use the mobile phone number from an LDAP user as the username for an IDaaS account. To achieve this, you can configure field mappings in this step. To use the mapping identifier feature, you must manually enable it, as shown in the following figure for the mobile phone field.
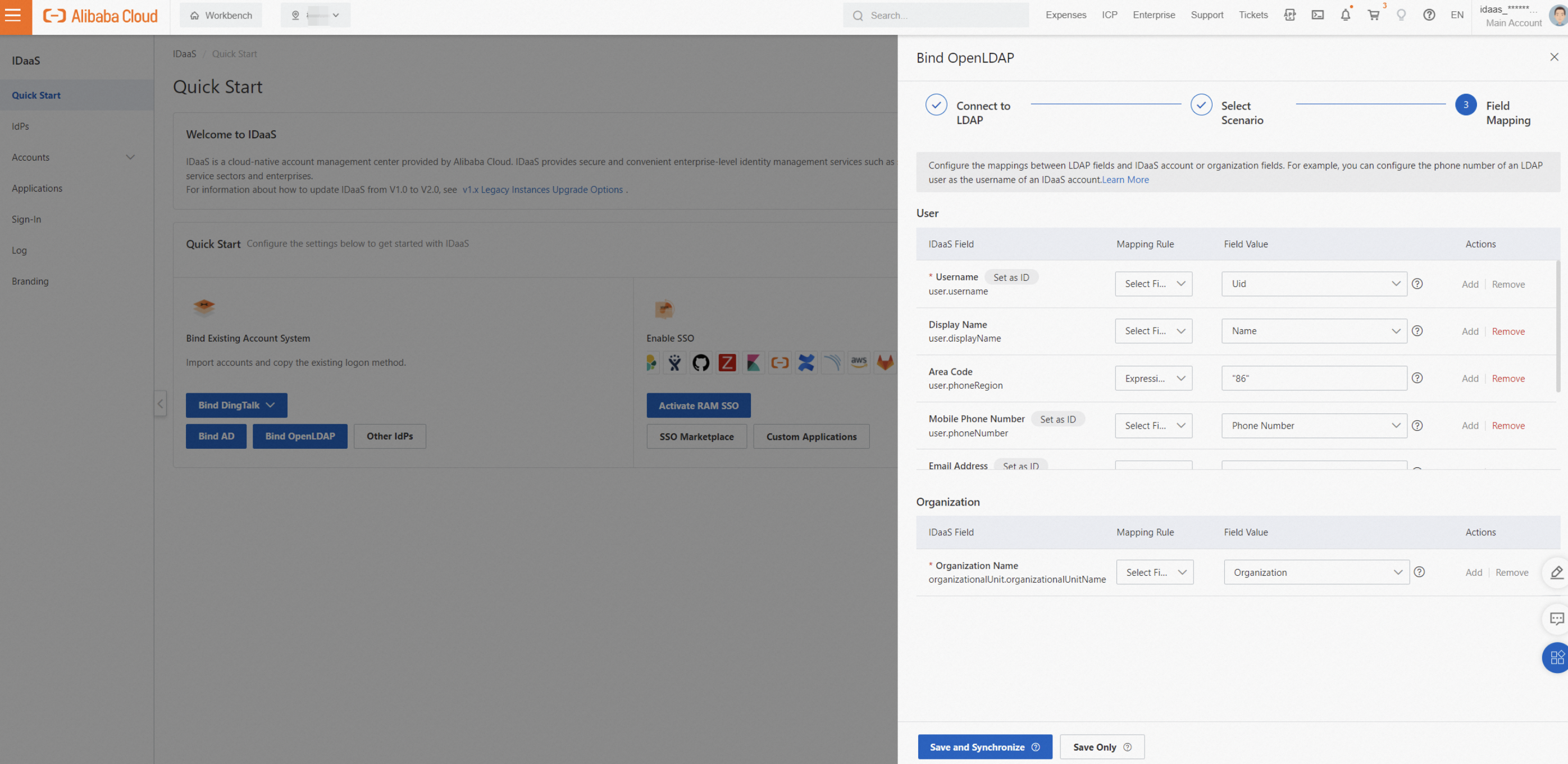
For more information about field mappings, see Field mappings.
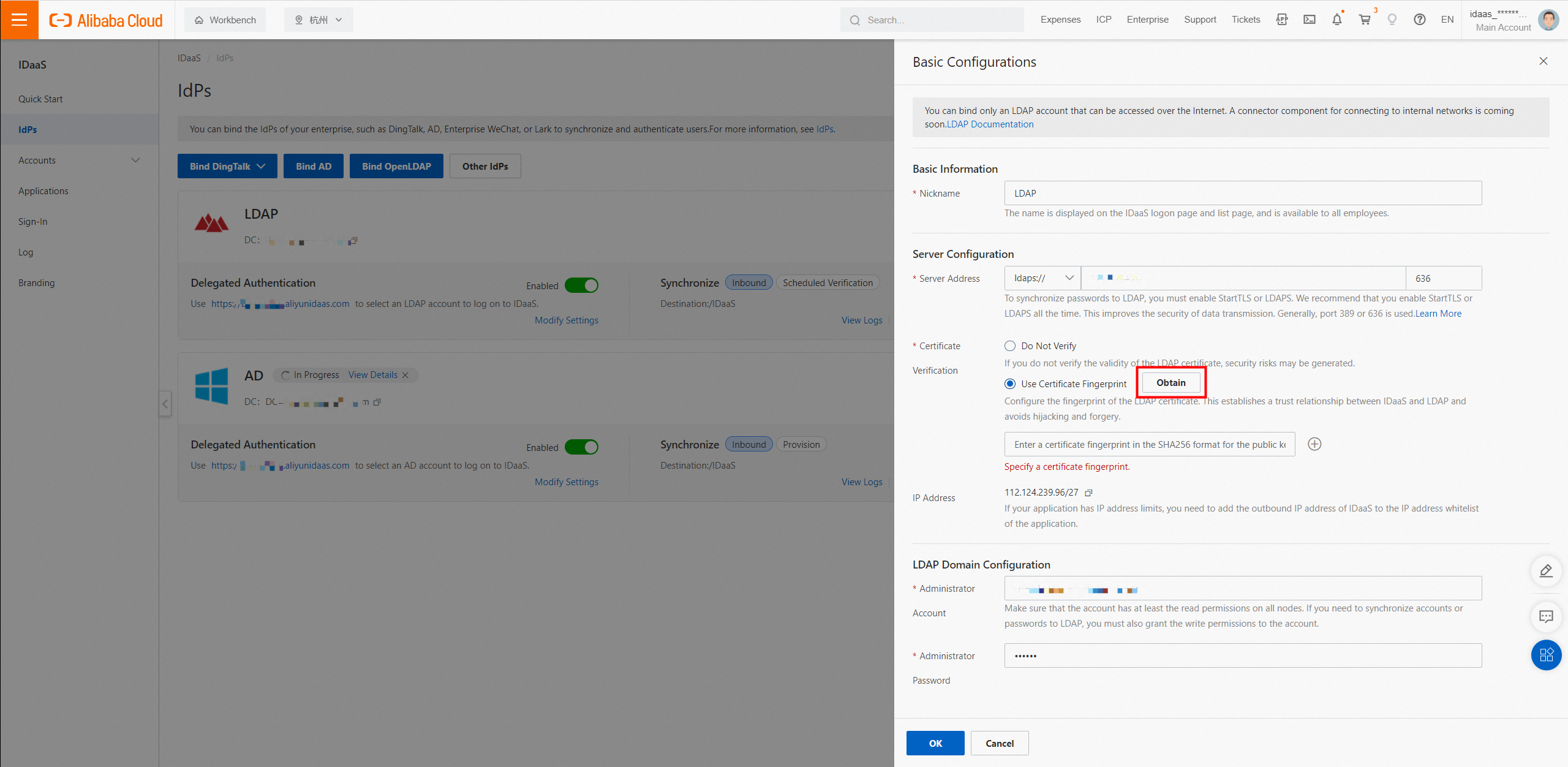
LDAP security configuration
By default, LDAP transmits data in plaintext. This data is not encrypted or protected, which creates a risk of data theft. Using LDAPS or StartTLS can significantly improve the security of data transmission. After you configure a certificate in LDAP, you can use LDAPS or StartTLS in IDaaS. We strongly recommend that you enable one of these options.
After you configure the certificate, you can click a button in IDaaS to obtain the certificate fingerprint. This establishes a trust relationship between IDaaS and the LDAP certificate and reduces the risk of certificate forgery.
LDAP custom configuration
ObjectClass
In LDAP, an ObjectClass is a collection of attributes. Every object must have an ObjectClass. You can use ObjectClass to define an object as a user, organization, or computer. For example, for the object in the following figure, if you set the User ObjectClass to "inetOrgPerson,posixAccount,top" in IDaaS, IDaaS treats the object as a user. You can view the ObjectClass when you edit an object in LDAP.
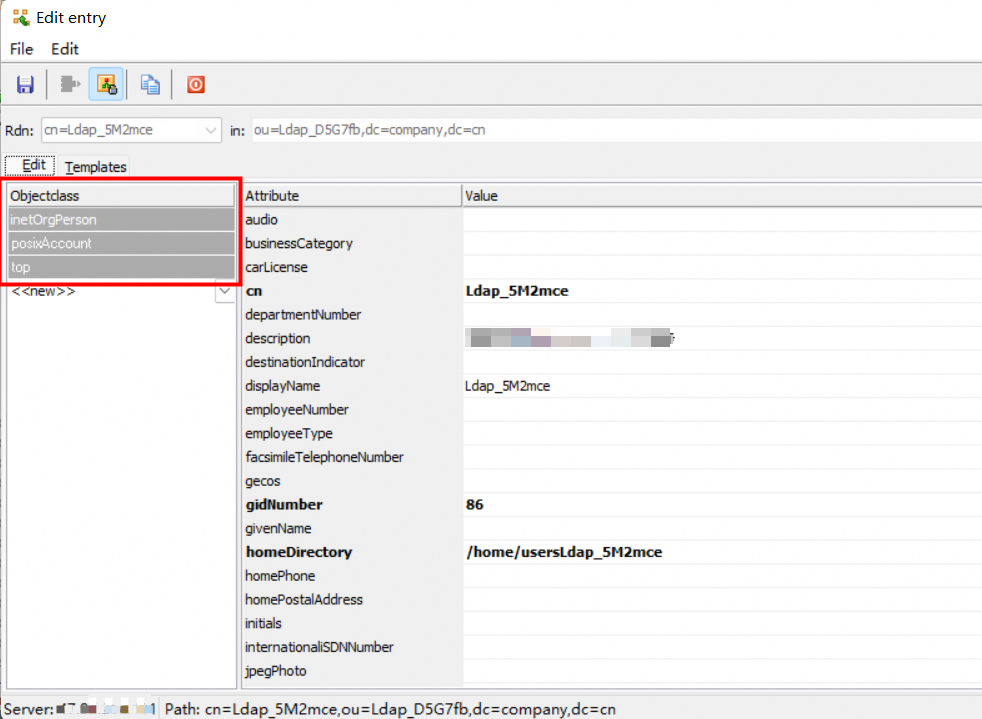
LDAP has flexible customization capabilities. If you customize the ObjectClass for users or organizations, you must ensure that the ObjectClass is consistent. This ensures that the data synchronized to IDaaS meets your expectations.
Logon identity
When a user logs on to IDaaS using LDAP delegated authentication, IDaaS uses these attributes to find the user in LDAP and verify the password. If the password is correct, the user is allowed to log on to IDaaS.
You can typically use attributes such as uid, mobile phone number, mailbox, or employee ID for logon. You can define these attributes during creation or in the Delegated Authentication settings. If you use multiple attributes, you must ensure that each attribute is unique and corresponds to the same LDAP user. Otherwise, the user cannot use delegated authentication.
Filter
Modifying the ObjectClass and filter affects the LDAP filter conditions. During a full synchronization, IDaaS accounts and organizations that do not meet the filter conditions are deleted. Before you make changes, you must adjust the synchronization protection limit. Also, you must fully test the filter results to ensure that they meet your expectations. For example, you can use another IDaaS instance for testing.
Overview
To synchronize only specific users from different organizations to IDaaS, you can define a custom filter statement. Only users who meet the conditions are synchronized. By default, the filter statement includes an AND condition for ObjectClass. Click View Details to see the complete statement.
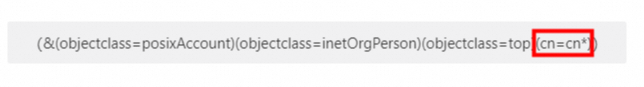
You can enter the filter statement in an LDAP Admin tool to check the filtered results.
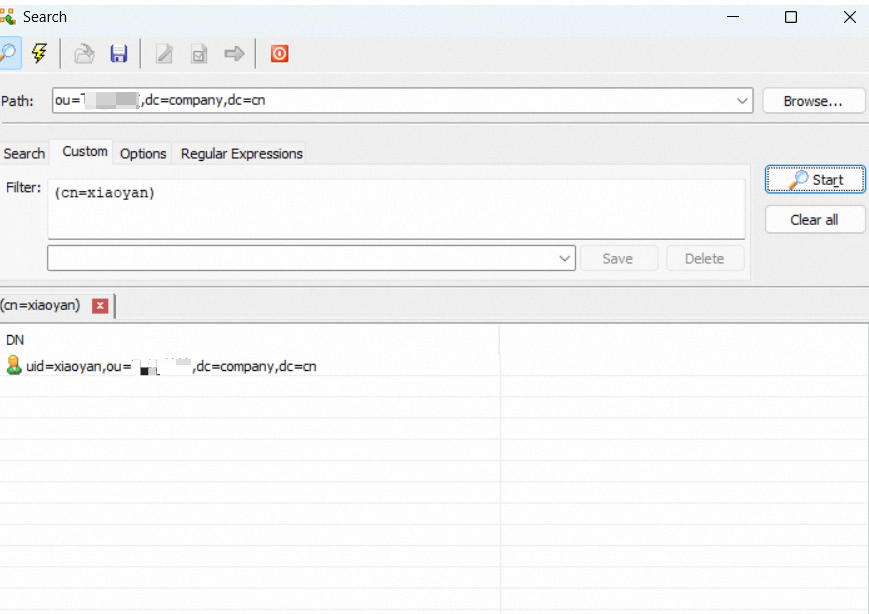
The following sections describe the common syntax and statements for LDAP filters.
Common syntax
Operator | Meaning | Example |
= | Equal to | (cn=Alice) |
>= | Greater than or equal to | (pwdLastSet>=1319563845000000000) |
<= | Less than or equal to | (employeeNumber<=1000) |
& | AND relationship. All conditions must be met. | (&(cn=CN*)(title=RD)) |
| | OR relationship. At least one condition must be met. | (|(cn=Test*)(cn=Admin*)) |
! | NOT relationship. All conditions must not be met. | (!(cn=Test*)(cn=Admin*)) |
Common statements
Scenario | Example |
Username starts with "CN" | (cn=CN*) |
User with a specific mailbox | (mail=alice@example.com) |
LDAP synchronization configuration
Obtain the Base DN
A Base Distinguished Name (Base DN) is the path identifier for a node in LDAP. IDaaS performs operations, such as queries and data synchronization, only under this node. You can set the Base DN of the source node in the Synchronization Direction settings.
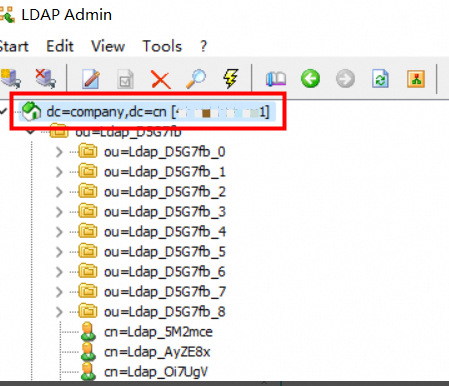
The DN format is ou=some-organization,dc=example,dc=com. The DN of the root node is typically dc=example,dc=com, which is your domain. You can also view the DN of a node directly in LDAP, as shown in the following figure.
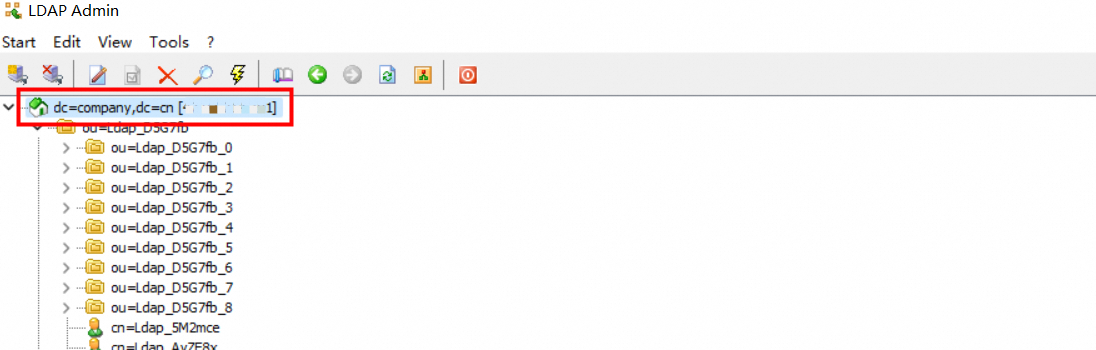
In addition, if a node's path changes, its Base DN also changes. To prevent data synchronization errors that are caused by path changes, IDaaS also uses the node's ObjectGuid as a node fingerprint when you configure the Base DN of the source node. If the Base DN changes and no longer matches the node fingerprint, data synchronization is blocked. After you reconfigure the source node, synchronization can proceed normally.
Scheduled verification
LDAP does not support queries for incremental data. IDaaS automatically performs a full synchronization of all data under the LDAP source node every morning. To synchronize data immediately, you can manually trigger a full synchronization.
IDaaS has a built-in synchronization protection feature. If more than 30 accounts or 10 organizations are scheduled for deletion, the synchronization task is automatically canceled. This feature prevents accidental data loss. We recommend that you adjust the synchronization protection settings based on the size of your enterprise.