Forward Open-Falcon alerts to ARMS Alert Management for centralized alert handling, deduplication, and notification routing.
Prerequisites
Before you begin, make sure that you have:
An Alibaba Cloud account with access to the ARMS console
A running Open-Falcon deployment
Step 1: Create an Open-Falcon integration
Log on to the ARMS console. In the left-side navigation pane, choose Alert Management > Integrations.
On the Alert Integration tab, click OpenFalcon.
In the Create OpenFalcon Integration dialog box, enter a name and description, specify the automatic recovery time, and click Save.
NoteIf an alert event is not triggered again within the specified recovery period, it is automatically cleared.
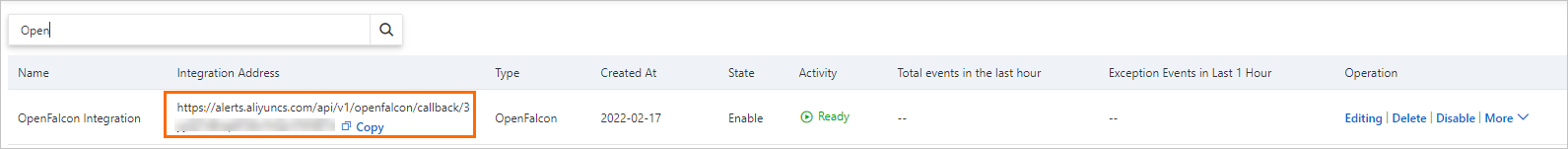
On the Alert Integration tab, find the integration you created and copy the URL in the Integration Address column.
Step 2: Configure the callback in Open-Falcon
Log on to the Open-Falcon homepage.
In the top navigation bar, click Templates.
In the upper-right corner of the Templates page, enter a name for the new alert template and click the + icon.
On the Configure Template page, create an alert rule in the Policies in the Template section. For details, see the Open-Falcon documentation.
Set Callback Address to the integration address you copied in Step 1 and click Save.
(Optional) Step 3: Customize field mappings
ARMS provides field mappings between Open-Falcon alert sources and ARMS alert events. To add or modify mappings, edit the integration.
Sample alert source:
{
"name": "cpu alert",
"endpoint": "test-host",
"metric": "cpu.user",
"status": "PROBLEM",
"step": "1",
"priority": 2,
"time": "2021-09-08 09:25:00",
"tpl_id": 1,
"exp_id": 2,
"stra_id": 1,
"tags": ""
}Send test data
On the Alert Integration tab, find the integration and click Edit in the Actions column.
In the Event Mapping section, click Send Test Data.
In the Send Test Data dialog box, paste a JSON alert payload and click Send.
NoteIf the message Uploaded. No events are generated. Configure mappings based on the original data. appears, the source fields have not been mapped yet. The raw data appears in the left pane for field selection during mapping configuration.
If the message Uploaded. appears, the event was reported successfully. For details, see View historical alert events.
In the Send Test Data dialog box, click Disable.
Configure field mappings
In the left pane of the Event Mapping section, click a data record to view its details.
In the right pane, map source fields to ARMS alert fields. Click the Map icon next to a field to choose a mapping method:
Method Description Direct Map one source field directly to one ARMS alert field Series Concatenate multiple source fields with a delimiter, then map the result to one ARMS alert field. Only special characters are supported as delimiters Condition Map source fields only when their values meet specified conditions Mapping table Map source severity levels to ARMS severity levels. Use this method only for the severityfield
ARMS alert fields
| Field | Description |
|---|---|
alertname | Custom alert name |
severity | Alert level. You must configure mappings for this field. The mapping method must be set to Direct |
message | Alert description used as the notification message body. Maximum 15,000 characters |
value | Sample metric value |
imageUrl | URL of a Grafana metrics line chart, displayed in the alert details |
check | Check item, such as CPU, JVM, Application Crash, or Deployment |
source | Alert source identifier |
class | Object type that triggered the event, such as host |
service | Source service, such as Login Service |
startat | Timestamp for the event start time |
endat | Timestamp for the event end time |
generatorUrl | URL of the event details page |
(Optional) Set a root node for batch processing
If the alert data contains an array node, you can designate it as the root node to process each element as a separate event.
In the Select Root Node section, select Use Batch Processing.
Select the array node to process as the root node.
Only one array node can be selected for batch processing at a time.
Configure event deduplication
Deduplication merges events that share the same value for a specified field into a single alert notification, reducing noise from repeated alerts.
Deduplication applies only to events that have not been cleared.
In the Event Deduplication section on the Integration Details page, select the fields to use for deduplication.
Click Deduplication Test to preview how historical events would be grouped.
NoteThe deduplication test uses only the 10 most recently uploaded data records from the Event Mapping section.
Click Save.
View alert event details
In the left-side navigation pane of the ARMS console, choose Alert Management > Alert Event History.
Click an alert event name to view its details. For more information, see View historical alert events.
Manage the integration
On the Alert Integration tab (Alert Management > Integrations), the following operations are available:
| Operation | Steps |
|---|---|
| View details | Click the integration row to open the Integration Details page |
| Update the key | Choose More > Update Key in the Actions column and click OK. After the key is updated, update the callback address in your Open-Falcon alert template as described in Step 2 |
| Edit | Click Edit in the Actions column, modify the settings, and click Save |
| Enable or disable | Click Enable or Disable in the Actions column |
| Delete | Click Delete in the Actions column and click OK |
| Add an event processing flow | Click Add Event Processing Flow in the Actions column. For details, see Work with event processing flows |
| Create a notification policy | Choose More > Create Notification Policy in the Actions column. For details, see Create and manage a notification policy |
What to do next
Create a notification policy so that the system generates alerts and sends alert notifications for reported alert events based on the policy. For details, see Create and manage a notification policy.
After notifications are configured, verify delivery on the Alert Sending History page. For details, see View historical alerts.