Terraform是一種開源工具,用於安全高效地預覽、配置和管理雲資源。本文介紹如何使用Terraform建立RAM角色並綁定權限原則。
本教程所含範例程式碼支援一鍵運行,您可以直接運行代碼。一鍵運行
前提條件
為了降低資訊安全風險,建議使用最小許可權的RAM使用者完成此教程的操作。請參見建立RAM使用者與為RAM使用者授權,完成此教程要求的權限的權限原則如下:
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "ram:GetRole", "ram:ListPoliciesForRole", "ram:ListRoles", "ram:CreateRole", "ram:DeleteRole", "ram:DetachPolicyFromRole", "ram:UpdateRole", "ram:GetPolicy", "ram:GetPolicyVersion", "ram:AttachPolicyToRole", "ram:CreatePolicy", "ram:CreatePolicyVersion", "ram:ListEntitiesForPolicy", "ram:ListPolicyVersions", "ram:DeletePolicy", "ram:DeletePolicyVersion", "ram:ListPoliciesForGroup", "ram:ListPolicies", "ram:ListPolicyAttachments" ], "Resource": "*" } ] }準備Terraform運行環境,您可以選擇以下任一方式來使用Terraform。
在Terraform Explorer中使用Terraform:阿里雲提供了Terraform的線上運行環境,您無需安裝Terraform,登入後即可線上使用和體驗Terraform。適用於零成本、快速、便捷地體驗和調試Terraform的情境。
Cloud Shell:阿里雲Cloud Shell中預裝了Terraform的組件,並已配置好身份憑證,您可直接在Cloud Shell中運行Terraform的命令。適用於低成本、快速、便捷地訪問和使用Terraform的情境。
在本地安裝和配置Terraform:適用於網路連接較差或需要自訂開發環境的情境。
使用的資源
alicloud_ram_policy:權限原則。
alicloud_ram_role:RAM角色。
alicloud_ram_role_policy_attachment:為RAM角色授予許可權。
步驟一:建立權限原則
建立一個工作目錄,並在該工作目錄中建立名為main.tf的設定檔。以下代碼將建立一個自訂權限原則,權限原則的更多資訊請參見權限原則語言,將代碼複製到main.tf中。
resource "random_integer" "default" { min = 10000 max = 99999 } # 權限原則 resource "alicloud_ram_policy" "policy" { policy_name = "policy-name-${random_integer.default.result}" policy_document = <<EOF { "Statement": [ { "Action": [ "oss:ListObjects", "oss:GetObject" ], "Effect": "Deny", "Resource": [ "acs:oss:*:*:mybucket", "acs:oss:*:*:mybucket/*" ] } ], "Version": "1" } EOF description = "this is a policy test" force = true }執行如下命令,初始化Terraform運行環境。
terraform init返回資訊如下,則Terraform初始化成功。
Terraform has been successfully initialized! You may now begin working with Terraform. Try running "terraform plan" to see any changes that are required for your infrastructure. All Terraform commands should now work. If you ever set or change modules or backend configuration for Terraform, rerun this command to reinitialize your working directory. If you forget, other commands will detect it and remind you to do so if necessary.執行如下命令,開始執行代碼。
terraform apply在執行過程中,根據提示輸入
yes並按下Enter鍵,等待命令執行完成,若出現以下資訊,則表示代碼執行成功。You can apply this plan to save these new output values to the Terraform state, without changing any real infrastructure. Do you want to perform these actions? Terraform will perform the actions described above. Only 'yes' will be accepted to approve. Enter a value: yes Apply complete! Resources: 2 added, 0 changed, 0 destroyed.驗證結果。
執行terraform show命令
您可以在工作目錄中,使用以下命令查詢Terraform已建立資源的詳細資料:
terraform show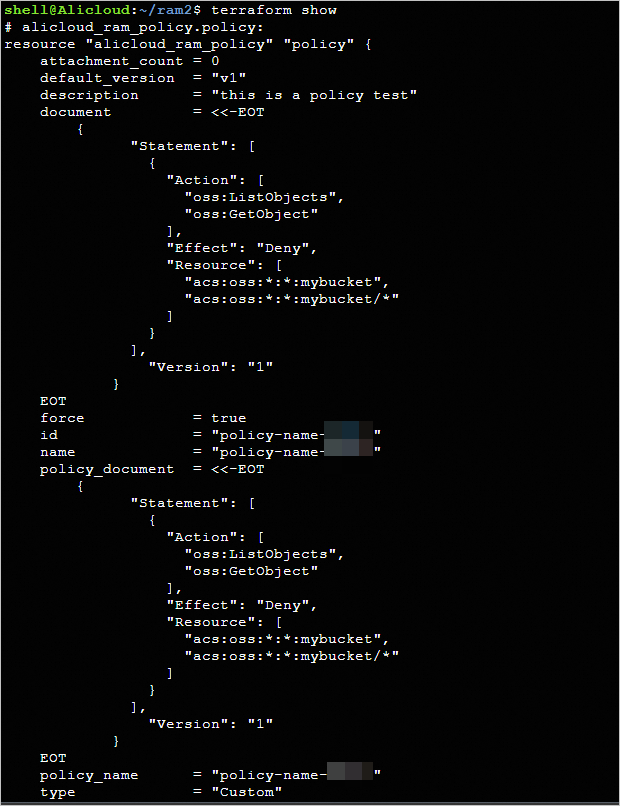
登入控制台查看
登入RAM控制台,進入頁面,查看已建立的權限原則。

步驟二:建立RAM角色並授權
在
main.tf檔案中增加如下代碼。# RAM角色 resource "alicloud_ram_role" "role" { name = "role-name-${random_integer.default.result}" document = <<EOF { "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "Service": [ "apigateway.aliyuncs.com", "ecs.aliyuncs.com" ] } } ], "Version": "1" } EOF description = "this is a role test." force = true } # 為RAM角色授予許可權 resource "alicloud_ram_role_policy_attachment" "attach" { policy_name = alicloud_ram_policy.policy.policy_name role_name = alicloud_ram_role.role.name policy_type = alicloud_ram_policy.policy.type }建立執行計畫,並預覽變更。
terraform plan執行如下命令,開始執行代碼。
terraform apply在執行過程中,根據提示輸入
yes並按下Enter鍵,等待命令執行完成,若出現以下資訊,則表示代碼執行成功。Apply complete! Resources: 2 added, 0 changed, 0 destroyed.驗證結果。
執行terraform show命令
您可以在工作目錄中,使用以下命令查詢Terraform已建立資源的詳細資料:
terraform show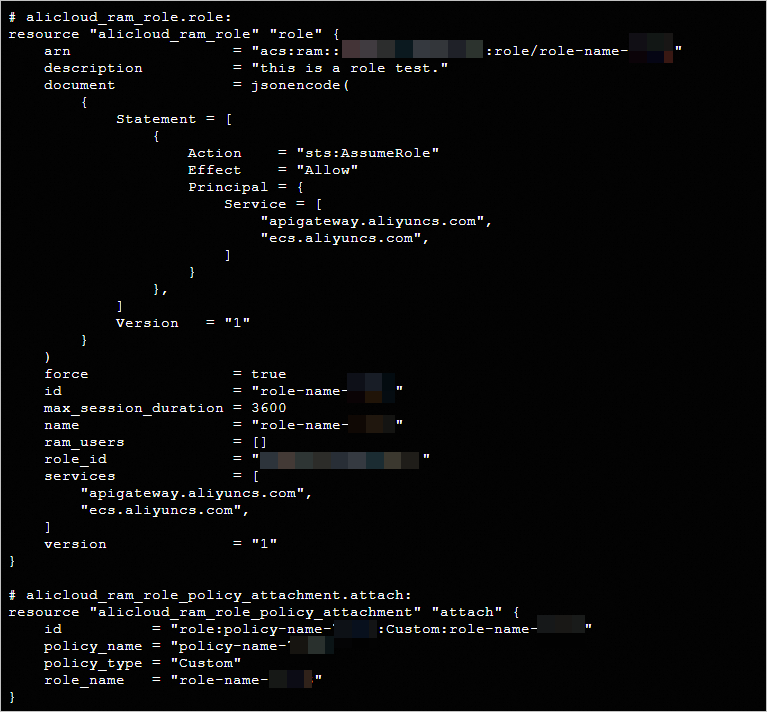
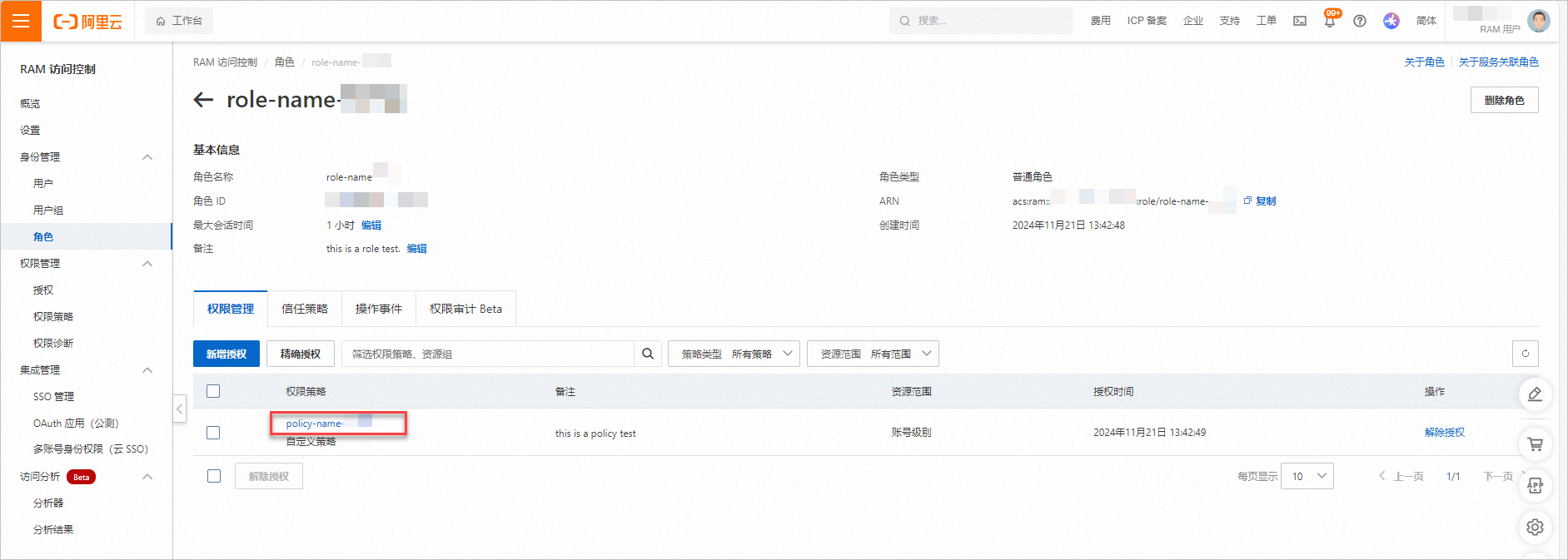
登入控制台查看
登入RAM控制台,進入頁面,查看已建立的RAM角色。

單擊使用者組的,查看RAM角色已擁有的許可權。
清理資源
當您不再需要上述通過Terraform建立或管理的資源時,請運行以下命令釋放資源。關於terraform destroy的更多資訊,請參見常用命令。
terraform destroy完整樣本
本教程所含範例程式碼支援一鍵運行,您可以直接運行代碼。一鍵運行
範例程式碼
如果您想體驗更多完整樣本,請前往更多完整樣本中對應產品的檔案夾查看。