本文為您介紹如何配置Cloud Firewall和營運資訊安全中心(Bastionhost)聯合部署時的存取原則,避免營運資訊安全中心(Bastionhost)訪問被Cloud Firewall誤攔截,影響業務運行。
應用情境
Cloud Firewall可以聯合營運資訊安全中心(Bastionhost)共同部署,防護互連網的訪問流量,為您的業務提供安全保障。但在聯合部署情境中,營運資訊安全中心(Bastionhost)的訪問流量可能會被Cloud Firewall誤攔截,導致營運資訊安全中心(Bastionhost)無法正常訪問互連網。因此,我們需要為Cloud Firewall配置互連網邊界防火牆的存取控制策略,保證在不影響營運資訊安全中心(Bastionhost)業務的情況下,Cloud Firewall可以防護營運資訊安全中心(Bastionhost)與互連網之間的流量。
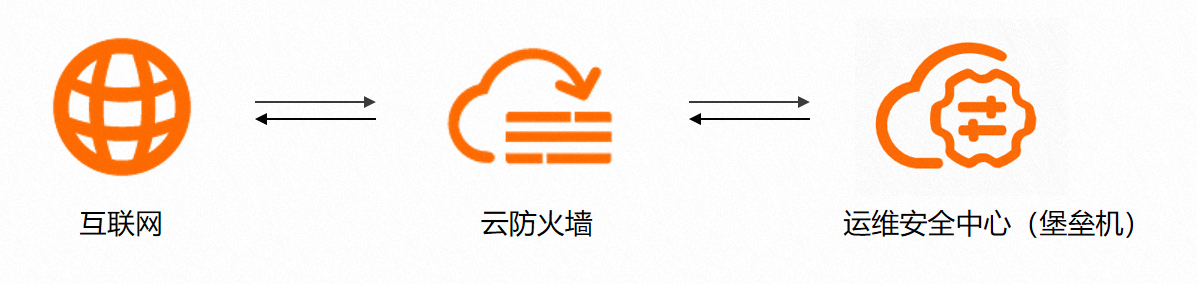
Cloud Firewall為營運資訊安全中心(Bastionhost)提供安全防護的原理圖如下圖所示。
如果您未按照以下操作配置,可能會導致無法正常訪問營運資訊安全中心(Bastionhost)的業務連接埠、無法匯入資產和使用者,以及無法使用網頁營運和播放錄影。
前提條件
已購買Cloud Firewall。具體步驟,請參見購買Cloud Firewall服務。
已購買並啟用營運資訊安全中心(Bastionhost)。具體步驟,請參見購買營運資訊安全中心執行個體、啟用Bastionhost。
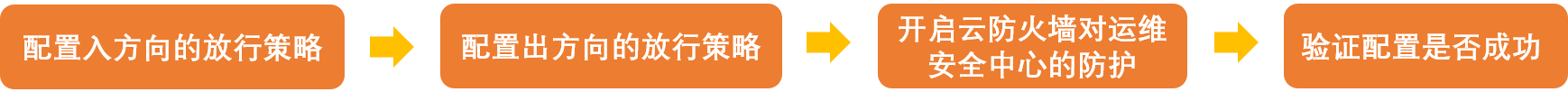
配置流程
步驟一:配置入方向的允許存取策略
配置互連網邊界防火牆入方向策略,允許互連網訪問營運資訊安全中心(Bastionhost)的開放連接埠。
在左側導覽列,選擇。
在入向頁簽,單擊建立策略。
在建立入向策略面板的自訂建立頁簽,參考入向策略配置項說明表建立一條對互連網訪問源允許存取的策略。然後單擊確定。
配置項
說明
源類型
選擇IP類型。
訪問源
填寫允許訪問營運資訊安全中心(Bastionhost)的互連網IP位址區段。
目的類型
選擇IP類型。
目的
填寫營運資訊安全中心(Bastionhost)營運網域名稱位址解析的IP地址。
說明您可以訪問互連網邊界防火牆頁面,通過篩選資產類型查看您的營運資訊安全中心(Bastionhost)IP地址,而無需切換到營運資訊安全中心(Bastionhost)控制台去查看IP資訊。
協議類型
選擇TCP。
連接埠類型
選擇連接埠或者地址簿。
當您需要開放多個營運資訊安全中心(Bastionhost)連接埠時,可以將這些連接埠先配置在地址簿中。在此選擇對應地址簿即可。
說明地址簿用於添加多個IP地址或連接埠進行大量設定,可簡化您的配置流程。如果您只需要開放一個連接埠,無需建立地址簿。
連接埠
當連接埠類型選擇連接埠時,您需要設定營運資訊安全中心(Bastionhost)連接埠。常用的營運資訊安全中心(Bastionhost)業務及連接埠如下,您可以根據實際情況配置。
SSH營運:60022
RDP營運:63389
錄影播放連接埠:9443
主機營運連接埠及營運門戶:443
單點登入器連接埠:20045
應用
選擇ANY。
動作
選擇允許存取,表示允許互連網地址訪問營運資訊安全中心(Bastionhost)對外開放的連接埠。
描述
對存取控制策略進行描述或備忘。輸入該策略的備忘內容,便於您後續查看時能快速區分每條策略的目的。
優先順序
設定存取控制策略的優先順序為最前。
啟用狀態
設定策略為啟用狀態。
建立一條對所有互連網地址拒絕訪問營運資訊安全中心(Bastionhost)的策略。
參考入向策略配置項說明表,設定訪問源為0.0.0.0/0、優先順序設定為最後。
步驟二:配置出方向的允許存取策略
營運資訊安全中心(Bastionhost)需要通過互連網訪問雲端服務,因此需要配置互連網邊界防火牆出方向策略,允許營運資訊安全中心(Bastionhost)對互連網訪問。
在出向頁簽,單擊建立策略。
在建立出向策略面板的自訂建立頁簽,參考出方向策略配置項說明表建立一條對營運資訊安全中心(Bastionhost)訪問員允許存取的策略。然後單擊確定。
配置項
說明
源類型
選擇IP類型。
訪問源
填寫營運資訊安全中心(Bastionhost)出口IP地址。
目的類型
選擇地址簿,並在選擇地址簿面板,選擇雲地址簿,搜尋阿里雲可信網域名稱Alibaba credible domains。
協議類型
選擇TCP協議類型。
連接埠類型
選擇連接埠或者地址簿。
當您需要開放多個雲端服務的連接埠時,可以將這些連接埠先配置在地址簿中。在此選擇對應地址簿即可。
說明地址簿用於添加多個IP地址或連接埠進行大量設定,可簡化您的配置流程。如果您只需要開放一個連接埠,無需建立地址簿。
連接埠
當連接埠類型選擇連接埠時,您需要設定營運資訊安全中心(Bastionhost)的連接埠:443、80。
應用
選擇HTTP 、HTTPS。
動作
選擇允許存取,表示允許營運資訊安全中心(Bastionhost)對外開放的連接埠訪問互連網地址。
描述
輸入該策略的備忘內容,便於您後續查看時能快速區分每條策略的目的。
優先順序
設定存取控制策略的優先順序為最前。
啟用狀態
設定策略為啟用狀態。
建立一條對營運資訊安全中心(Bastionhost)所有地址拒絕訪問互連網的策略。
參考出方向策略配置項說明表,設定訪問源為0.0.0.0/0、優先順序設定為最後。
步驟三:開啟Cloud Firewall對營運資訊安全中心的防護
策略配置完成後,您需要開啟互連網邊界防火牆開關,開啟對營運資訊安全中心(Bastionhost)的防護。
在左側導覽列,單擊防火牆開關。
在互連網邊界頁簽,定位到營運資訊安全中心(Bastionhost)的IP,單擊右側操作列的開啟保護。
說明新購買的營運資訊安全中心(Bastionhost)大概需要15~30分鐘同步到Cloud Firewall。
完成以上配置後,即可實現Cloud Firewall保護營運資訊安全中心(Bastionhost)的同時不影響營運資訊安全中心(Bastionhost)業務的正常使用。您可以登入營運資訊安全中心(Bastionhost)匯入資產和使用者,進行營運及審計。
步驟四:驗證配置是否成功
如果您能正常訪問營運資訊安全中心(Bastionhost)的業務連接埠、並匯入資產和使用者,能使用網頁營運和播放錄影,表示配置成功。您可以訪問互連網邊界防火牆流量日誌頁簽,查看營運資訊安全中心(Bastionhost)與互連網之間的流量日誌。具體操作,請參見日誌審計。