如果您想使用RAM使用者訪問其他雲資源,可以參考本文檔,根據使用情境(同帳號或跨帳號)為RAM使用者授予對應許可權。本文介紹同帳號授權和跨帳號授權的詳細步驟。
前提條件
叢集的產品系列為企業版、基礎版或湖倉版。
Spark作業許可權說明
提交Spark作業,需要具備以下三種許可權:
許可權 | 說明 |
以下任一許可權:
|
具體操作請參見為RAM使用者授權。 |
AnalyticDB for MySQL庫表的讀寫權限 | AnalyticDB for MySQL預設通過資料庫帳號進行庫表許可權管理。通過RAM使用者提交Spark作業時,如果Spark作業需要讀寫資料,需要將資料庫普通帳號與RAM使用者綁定。具體操作請參見綁定或解除綁定RAM使用者與資料庫帳號。 |
| 用於授權AnalyticDB for MySQL Spark訪問其他雲資源,如訪問OSS目錄,OTS資料等。具體操作請參見同帳號授權。 |
同帳號授權
前提條件
已建立RAM使用者。
操作步驟
通過RAM控制台授權(推薦)
步驟一:建立RAM角色並授權
建立RAM角色。
說明如果您已建立RAM角色,且RAM角色的信任主體類型為雲端服務、信任主體名稱為雲原生資料倉儲AnalyticDB MySQL 版,可跳過該步驟,執行後續步驟。
使用Resource Access Management員登入RAM控制台。
在左側導覽列,選擇。
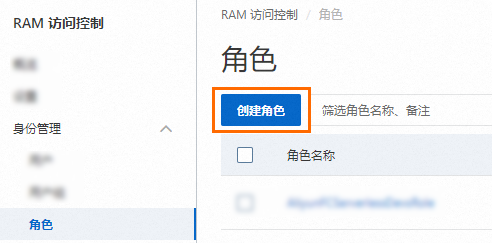
在角色頁面,單擊建立角色。
在建立角色頁面,選擇信任主體類型為雲端服務,然後選擇信任主體名稱為雲原生資料倉儲AnalyticDB MySQL 版,最後單擊確定。
在建立角色對話方塊,輸入角色名稱,然後單擊確定。
為RAM角色授權。
單擊精確授權。
在精確授權面板,選擇權限原則類型為系統策略或自訂策略,然後輸入權限原則名稱(大小寫不敏感)。
若您僅想訪問指定的雲資源時,需自訂權限原則。自訂策略的方法請參見建立自訂權限原則。
單擊確認。
步驟二:提交Spark作業
通過RAM控制台建立RAM角色並授權後,在提交Spark作業時,需要在Spark作業配置中配置spark.adb.roleArn參數,以確保Spark作業可正常執行。樣本如下:
{
"comments": [
"-- Here is just an example of using LakeCache. Modify the content and run your spark program."
],
"args": ["oss://testBucketName/data/readme.txt"],
"name": "spark-oss-test",
"file": "oss://testBucketName/data/example.py",
"conf": {
"spark.adb.lakecache.enabled": "true";
"spark.adb.roleArn": "acs:ram::testAccountID:role/adbtest";
}
}快速授權
在同帳號授權後,AliyunADBSparkProcessingDataRole角色將預設被授予AliyunADBSparkProcessingDataRolePolicy許可權。該許可權具備對OSS、TableStore、DMS等雲資源的存取權限,因此可能會導致過度授權的問題。建議您在授權後,解除AliyunADBSparkProcessingDataRolePolicy許可權,僅為AliyunADBSparkProcessingDataRole角色授予業務所需雲資源的許可權。
單擊快速授權連結。
說明僅具備RAM使用者系統管理權限(至少擁有建立RAM角色、建立RAM策略、查詢RAM角色和查詢RAM策略的許可權)的使用者,可以進行快速授權。
單擊左下角同意授權。
授權後將自動建立可供AnalyticDB for MySQL使用的服務角色AliyunADBSparkProcessingDataRole,AnalyticDB for MySQL使用此角色來訪問其他雲資源。
跨帳號授權
AnalyticDB for MySQL Spark支援訪問其他阿里雲帳號的所有雲資源。本文以阿里雲帳號A(主帳號,帳號ID為testAccountIDA)跨帳號訪問阿里雲帳號B(主帳號,帳號ID為testAccountIDB)中的資料為例,介紹跨帳號授權的具體操作。
步驟一:為B帳號建立RAM角色並授權
建立RAM角色,並允許A帳號扮演該RAM角色。
說明如果您已建立RAM角色,並允許A帳號扮演該RAM角色,可跳過該步驟,執行後續步驟。
使用阿里雲帳號B(主帳號)或Resource Access Management員登入RAM控制台。
在左側導覽列,選擇。
在角色頁面,單擊建立角色。
在建立角色頁面,選擇信任主體類型為雲帳號,然後設定具體的阿里雲帳號,最後單擊確定。
設定角色資訊。
輸入角色名稱。本樣本角色名稱設定為
admin-oss。可選:輸入備忘。
信任的雲帳號選擇其他云账号,然後輸入A帳號的阿里雲帳號UID(
testAccountIDA)。
單擊完成。
為RAM角色精確授權。
單擊精確授權。
在精確授權面板,選擇權限原則類型為系統策略或自訂策略,然後輸入權限原則名稱(大小寫不敏感)。
訪問OSS
AliyunOSSReadOnlyAccess:唯讀訪問Object Storage Service服務(OSS)的許可權。
AliyunOSSFullAccess:管理Object Storage Service服務(OSS)許可權。如果需要對OSS外表執行INSERT等資料更新操作,需為該RAM角色授予此許可權。
訪問指定VPC下的資源
若您想訪問指定VPC下的資源時,需自訂權限原則,並在Resource參數中指定資源所屬的安全性群組和交換器。自訂策略的方法請參見建立自訂權限原則。
本文樣本僅授權訪問指定VPC下的RDS MySQL執行個體,自訂權限原則的名稱為
eni_policy,權限原則內容如下:說明您需要為RDS MySQL執行個體添加安全性群組,且安全性群組規則的入方向與出方向允許存取RDS MySQL連接埠的訪問請求。
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": "ecs:*", "Resource": "acs:ecs:*:*:securitygroup/<RDS所屬安全性群組ID>" }, { "Effect": "Allow", "Action": "vpc:*", "Resource": "acs:vpc:*:*:vswitch/<RDS所屬交換器ID>" } ] }單擊確認。
修改信任策略,允許A帳號下任意的RAM使用者扮演該RAM角色。
在左側導覽列,選擇。
在角色頁面,單擊目標RAM角色名稱。
在信任策略頁簽,單擊編輯信任策略。
在編輯器中修改信任策略內容,然後單擊確定。
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::testAccountIDA:root" ] } }, { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "Service": [ "testAccountIDA@ads.aliyuncs.com" ] } } ], "Version": "1" }
步驟二:為A帳號建立RAM使用者並授予扮演RAM角色的許可權
建立RAM使用者。
使用阿里雲帳號A(主帳號)或Resource Access Management員登入RAM控制台。
在左側導覽列,選擇。
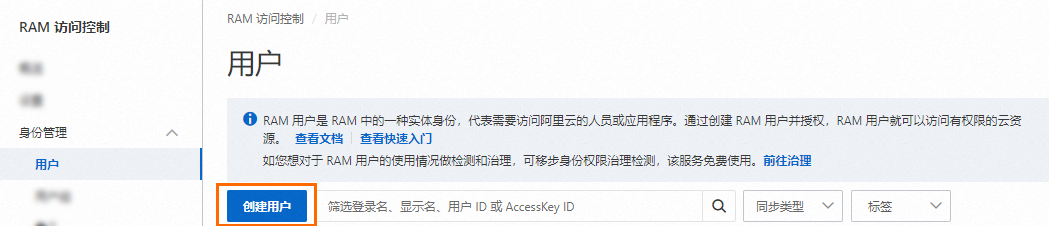
在使用者頁面,單擊建立使用者。
在建立使用者頁面的使用者帳號資訊地區,設定使用者基本資料。
登入名稱稱:可包含英文字母、數字、半形句號(.)、短劃線(-)和底線(_),最多64個字元。
顯示名稱:最多包含128個字元或漢字。
標籤:單擊
 ,然後輸入標籤鍵和標籤值。為RAM使用者綁定標籤,便於後續基於標籤的使用者管理。
,然後輸入標籤鍵和標籤值。為RAM使用者綁定標籤,便於後續基於標籤的使用者管理。
說明單擊添加使用者,可以大量建立多個RAM使用者。
在訪問方式地區,選擇控制台访问,並根據需要設定控制台登入密碼、重設密碼原則和多因素認證策略。詳情請參見控制台訪問。
單擊確定。
建立權限原則,允許RAM使用者扮演任何角色。
在左側導覽列,選擇。
在權限原則頁面,單擊建立權限原則。
在建立權限原則頁面,單擊指令碼編輯頁簽。
輸入權限原則內容,然後單擊確定。
{ "Version": "1", "Statement": [ { "Action": "ram:PassRole", "Resource": "*", "Effect": "Allow" } ] }在建立權限原則對話方塊,輸入策略名稱稱和備忘,然後單擊確定。
為RAM使用者授權。
在添加許可權面板,為RAM使用者添加步驟2所建立的許可權。
單擊確認新增授權。