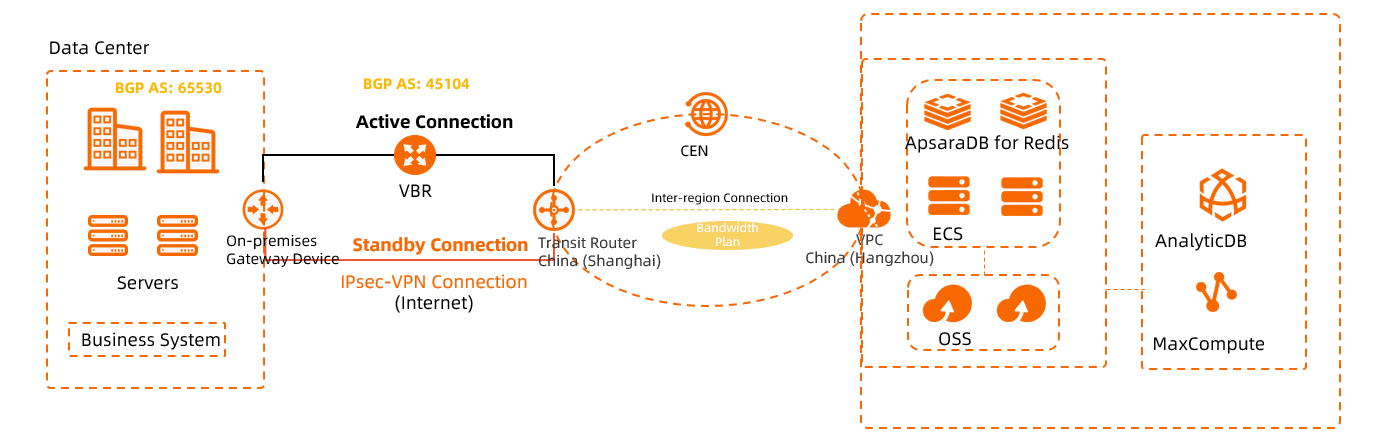
This topic describes how to use an IPsec-VPN connection and an Express Connect circuit to set up active/standby links between a data center and a virtual private cloud (VPC). The IPsec-VPN connection is associated with a transit router.
Scenario
This topic uses the following scenario as an example. A company has a data center in Shanghai and has deployed a VPC in the China (Hangzhou) region. Applications and services are deployed on Elastic Compute Service (ECS) instances in the VPC. The company wants to deploy active/standby links to the cloud to establish a highly reliable connection between the data center and the VPC.
Network planning
Network feature planning
The following network features are used in this scenario:
The data center connects to Alibaba Cloud through an Express Connect circuit and an IPsec-VPN connection.
When both the Express Connect circuit and the IPsec-VPN connection are active, all traffic between the data center and the VPC is routed primarily through the Express Connect circuit. If the Express Connect circuit fails, all traffic between the data center and the VPC automatically switches to the IPsec-VPN connection.
To create an IPsec-VPN connection, set the Gateway Type to Public and the attached resource type to Cloud Enterprise Network.
The data center, the virtual border router (VBR) instance, and the IPsec-VPN connection all use the Border Gateway Protocol (BGP) for dynamic routing. This simplifies route configuration by enabling automatic route distribution and learning.
BGP is supported only by IPsec-VPN connections in specific regions. For more information about the supported regions, see Configure routes.
ImportantThe following information describes data transmission in this scenario:
When the Express Connect circuit, IPsec-VPN connection, and BGP dynamic routing are all active, Cloud Enterprise Network (CEN) learns the CIDR block of the data center through both the Express Connect circuit and the IPsec-VPN connection. Similarly, the data center learns the route to the VPC from CEN through both connections. By default, the route learned through the Express Connect circuit has a higher priority. Therefore, traffic between the VPC and the data center is routed primarily through the Express Connect circuit.
If the BGP peer between the data center and the VBR is interrupted, CEN automatically revokes the route learned through the Express Connect circuit. The route learned through the IPsec-VPN connection then takes effect, and traffic is automatically routed through the IPsec-VPN connection. When the BGP peer between the data center and the VBR recovers, traffic switches back to the Express Connect circuit, and the IPsec-VPN connection resumes its role as the standby link.
CIDR block planning
When you plan CIDR blocks, make sure that the CIDR blocks of the data center and the VPC do not overlap.
Resource | CIDR block and IP address |
VPC | Primary CIDR block: 172.16.0.0/16
|
IPsec-VPN connections | BGP configuration: The tunnel CIDR block is 169.254.10.0/30, with a local BGP IP address of 169.254.10.1 and a local autonomous system number (ASN) of 45104 (default). |
VBR | VBR configuration:
|
On-premises gateway devices | Public IP address of the on-premises gateway device: 211.XX.XX.68 |
BGP configuration for the on-premises gateway device: Tunnel CIDR block: 169.254.10.0/30. Local BGP IP address: 169.254.10.2. Local ASN: 65530. | |
Data center | CIDR blocks to be connected to the VPC:
|
Preparations
Before you start, complete the following operations:
Create a VPC in the China (Hangzhou) region and deploy applications on an ECS instance within the VPC. For more information, see Create a VPC with an IPv4 CIDR block.
Create a CEN instance. Then, create an Enterprise Edition transit router in the China (Hangzhou) and China (Shanghai) regions. For more information, see Create a CEN instance and Create a transit router.
ImportantWhen you create a transit router, you must configure a CIDR block for the transit router. Otherwise, IPsec connections cannot be associated with the transit router.
If you have created a transit router, you can configure a CIDR block for the transit router. For more information, see Transit router CIDR blocks.
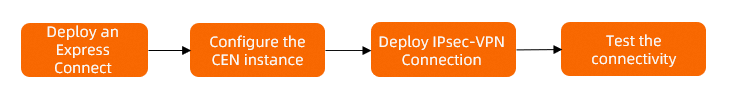
Configuration flow
Step 1: Deploy an Express Connect circuit
Deploy an Express Connect circuit to connect the data center to Alibaba Cloud.
Create a dedicated Express Connect circuit.
In this example, a connection over a dedicated Express Connect circuit is created in the China (Shanghai) region. The connection is named Circuit1. For more information, see Create and manage a dedicated connection over an Express Connect circuit.
Create a VBR instance.
Log on to the Express Connect console.
In the left-side navigation pane, click Virtual Border Routers (VBRs).
In the top navigation bar, select the region where you want to create the VBR instance.
In this example, the China (Shanghai) region is selected.
On the Virtual Border Routers (VBRs) page, click Create VBR.
In the Create VBR panel, configure the parameters and click OK.
The following table describes only the key parameters. Use the default values for the other parameters. For more information, see Create and manage VBRs.
Parameter
Description
VBR
Account Type
Select the type of account that owns the VBR instance.
In this example, select Current Account.
Name
Enter a name for the VBR.
Enter VBR.
Express Connect Circuit
Select the Express Connect circuit to which the VBR will be attached.
Select Dedicated Physical Connection as the type, and then select the Express Connect circuit that you created in Step 1.
VLAN ID
Enter a VLAN ID for the VBR.
In this example, enter 0.
Set VBR Bandwidth Value
Specify the peak bandwidth for the VBR.
Select a maximum bandwidth value as needed.
Alibaba Cloud Side IPv4 Address
Enter the gateway IPv4 address on the Alibaba Cloud side.
In this example, enter 10.0.0.2.
Data Center Side IPv4 Address
Enter the gateway IPv4 address on the data center side.
This example uses 10.0.0.1.
IPv4 Subnet Mask
Enter the subnet mask for the Alibaba Cloud and customer-side IPv4 addresses.
Enter 255.255.255.252.
Configure a BGP group for the VBR instance.
On the Virtual Border Routers (VBRs) page, click the ID of the VBR.
On the details page, click the BGP Groups tab.
On the BGP Groups tab, click Create BGP Group, set the following parameters, and click OK.
The following table describes only the key parameters. Use the default values for the other parameters. For more information, see Create a BGP group.
Configuration item
Description
VBR
Name
Enter the name of the BGP group.
Enter VBR-BGP.
Peer ASN
Enter the ASN of the on-premises gateway device.
This topic uses 65530 as the autonomous system number for the on-premises gateway device.
Local ASN
Enter the Autonomous System Number (ASN) of the VBR instance.
In this topic, enter 45104 as the autonomous system number for the VBR.
Configure a BGP peer for the VBR instance.
On the VBR details page, click the BGP Peers tab.
On the BGP Peers tab, click Create BGP Peer.
In the Create BGP Peer dialog box, set the following parameters and click OK.
The following table describes only the key parameters. Use the default values for the other parameters. For more information, see Create a BGP peer.
Configuration item
Description
VBR
BGP Group
Select the BGP group to join.
In this example, select VBR-BGP.
BGP Peer IP
Enter the IP address of the BGP peer.
This topic uses the IP address 10.0.0.1. This is the IP address of the on-premises gateway device's interface for the Express Connect circuit.
Configure BGP routing on the on-premises gateway device.
After you configure BGP on the on-premises gateway device, a BGP peer relationship is established between the on-premises gateway device and the VBR instance. This enables automatic route learning and propagation.
NoteIn this example, the software Adaptive Security Appliance (ASA) 9.19.1 is used to describe how to configure a Cisco firewall. The commands may vary with software versions. Consult the documentation or your vendor based on your actual environment during operations. For more information, see Configure local gateways.
The following content contains third-party product information, which is only for reference. Alibaba Cloud does not make guarantees or other forms of commitments for the performance and reliability of third-party products, or the potential impacts of operations performed by using these products.
interface GigabitEthernet0/3 nameif VBR1 # Configure the name of the interface that connects to VBR1. security-level 0 ip address 10.0.0.1 255.255.255.0 # Configure a private IP address for the GigabitEthernet 0/3 interface. no shutdown # Enable the interface. ! router bgp 65530 # Enable BGP and configure the ASN of the data center. 65530 is used in this example. bgp router-id 10.0.0.1 # Enter the ID of the BGP router. In this example, 10.0.0.1 is used. bgp log-neighbor-changes address-family ipv4 unicast neighbor 10.0.0.2 remote-as 45104 # Create a BGP peer for the VBR. network 192.168.0.0 mask 255.255.255.0 # Advertise the CIDR block of the data center. network 192.168.1.0 mask 255.255.255.0 network 192.168.2.0 mask 255.255.255.0 neighbor 10.0.0.2 activate # Activate the BGP peer. neighbor 10.0.0.2 weight 1000 # Set the weights of the routes learned through the Express Connect circuit to 1000. exit-address-family !
Step 2: Configure Cloud Enterprise Network
After you deploy the Express Connect circuit, the data center can access Alibaba Cloud. However, the data center and the VPC cannot communicate with each other. To enable communication, you must connect the VBR instance and the VPC to CEN.
Create a VPC connection.
-
Log on to the CEN console.
-
On the Instances page, find the CEN instance that you created and click its ID.
-
On the tab, find the transit router that you want to manage in the China (Hangzhou) region and click Create Connection in the Actions column.
On the Connection with Peer Network Instance page, configure the following parameters and click OK.
The following table describes only the key parameters. The default values are used for other parameters. For more information, see Create a VPC connection.
Parameter
Description
VPC connection
Instance Type
Select the type of network instance.
In this example, Virtual Private Cloud (VPC) is selected.
Region
Select the region of the network instance.
In this example, China (Hangzhou) is selected.
Transit Router
The system automatically displays the transit router in the current region.
Resource Owner ID
Specify whether the network instance belongs to the current Alibaba Cloud account.
In this example, Current Account is selected.
Billing Method
Select a billing method for the VPC connection. Default value: Pay-As-You-Go. For more information about the billing rules for transit routers, see Billing.
Attachment Name
Enter a name for the VPC connection.
In this example, VPC-Attachment is used.
Network Instance
Select a network instance.
In this example, the VPC created in the Preparations section is selected.
VSwitch
Select the vSwitches that are deployed in the zones of the transit router.
If the transit router supports only one zone in the current region, you must select a vSwitch in that zone.
If the transit router supports multiple zones in the current region, you must select vSwitches in at least two different zones. This provides disaster recovery across zones for traffic between the VPC and the transit router.
Select a vSwitch in each zone to reduce traffic detours and transmission delays, and to improve performance.
Make sure that each selected vSwitch has an idle IP address. If the VPC does not have a vSwitch in the zones supported by the transit router, or if the vSwitches do not have idle IP addresses, you must create a vSwitch. For more information, see Create and manage vSwitches.
In this example, vSwitch 1 is selected in Zone H and vSwitch 2 is selected in Zone I.
Advanced Settings
Specify whether to enable the advanced features. By default, all advanced features are enabled.
In this example, the default settings are used.
-
You can create a VBR connection.
On the tab, find the Transit Router instance in the China (Shanghai) region, and in the Actions column, click Create Connection.
On the Connection to Peer Network Instance page, configure the parameters and click OK.
The following table describes only the key parameters. Use the default values for the other parameters. For more information, see Attach a VBR to a CEN instance.
Parameter
Description
VBR
Instance Type
Specify the network instance type.
Select Virtual Border Router (VBR).
Region
Select the region of the network instance.
This example uses the China (Shanghai) region.
Transit Router
The system automatically displays the transit router instances in the current region.
Resource Owner ID
Specify whether the network instance belongs to your Alibaba Cloud account.
In this example, Current Account is selected.
Attachment Name
Enter a name for the network instance connection.
For this example, enter VBR-Attachment.
Network Instance
Select a network instance.
In this example, VBR is selected.
Advanced Settings
Select whether to enable all advanced features. By default, all advanced features are enabled.
Keep the default configurations. All advanced features are enabled by default.
Create an inter-region connection.
The transit routers associated with the VBR and the VPC are in different regions. By default, they cannot communicate with each other. You must create an inter-region connection between the transit routers in the China (Hangzhou) and China (Shanghai) regions to enable communication.
On the Instances page, find the destination CEN instance and click its ID.
On the tab, click Allocate Bandwidth for Inter-region Communication.
On the Connection with Peer Network Instance page, configure the inter-region connection and click OK.
Create an inter-region connection using the following configurations. Keep the default values for other parameters. For more information, see Create an inter-region connection.
Parameter
Description
Instance Type
Select Inter-region Connection.
Region
Select a region to connect.
Select China (Hangzhou).
Transit Router
The system automatically displays the ID of the transit router in the current region.
Attachment Name
Enter a name for the inter-region connection.
Enter Cross-Region-test.
Peer Region
Select the peer region to connect.
Select China (Shanghai).
Transit Router
The system automatically displays the ID of the transit router in the current region.
Bandwidth Allocation Mode
An inter-region connection supports the following bandwidth allocation modes:
Allocate from Bandwidth Plan: Bandwidth is allocated from a purchased bandwidth plan.
Pay-By-Data-Transfer: You are charged for the actual data transfer over the inter-region connection.
Select Pay-By-Data-Transfer.
Default Line Type
Use the default link type.
Bandwidth
Enter a bandwidth value for the inter-region connection. Unit: Mbit/s.
Advanced Settings
Keep the default configuration. All advanced configuration options are selected.
Step 3: Deploy an IPsec-VPN connection
After you complete the preceding steps, the data center and the VPC can communicate through the Express Connect circuit. Now, you can deploy the IPsec-VPN connection as a standby link.
Log on to the VPN Gateway console.
Create a customer gateway.
Before you can establish an IPsec-VPN connection, you must create a customer gateway to register information about the on-premises gateway device with Alibaba Cloud.
In the navigation pane on the left, choose .
In the top navigation bar, select the region where you want to create the customer gateway.
When you select the region for your customer gateway, select the Alibaba Cloud region that is closest to your on-premises data center. In this topic, China (Shanghai) is used as an example.
On the Customer Gateway page, click Create Customer Gateway.
In the Create Customer Gateway panel, set the following parameters and click OK.
The following table describes only the key parameters. Use the default values for the other parameters. For more information, see Create a customer gateway.
Configuration item
Description
Customer Gateway
Name
Enter a name for the customer gateway.
Enter Customer-Gateway.
IP Address
Enter the public IP address of the on-premises gateway device that you want to connect to Alibaba Cloud.
In this example, the public IP address of the on-premises gateway device is 211.XX.XX.68.
ASN
Enter the BGP ASN of the on-premises gateway device.
In this example, enter 65530.
Create an IPsec-VPN connection.
After you create the customer gateway, create an IPsec-VPN connection in the Alibaba Cloud console. This connection is used to establish an encrypted tunnel to the data center.
In the navigation pane on the left, go to .
On the IPsec Connections page, click Bind CEN.
On the Create IPsec-VPN Connection page, set the parameters for the IPsec-VPN connection and click OK.
IPsec-VPN connections are a billable service. For more information, see Billing overview.
Parameter
Description
IPsec-VPN connection
Name
Enter a name for the IPsec-VPN connection.
In this example, enter IPsec-VPN-connection.
Region
Select the region of the transit router to attach.
The IPsec-VPN connection is created in the same region as the transit router.
Select China (Shanghai).
Gateway Type
Select the network type for the IPsec-VPN connection.
In this topic, the selection is Internet.
Bind CEN
Select the account that owns the transit router.
Select Same Account.
CEN Instance ID
Select the CEN instance.
Select the CEN instance created in the Preparations section.
The system displays the instance ID and CIDR block of the transit router that is created by the CEN instance in the current region. The IPsec-VPN connection will be attached to the transit router.
Zone
Select a zone that supports transit routers in which to deploy the IPsec-VPN connection.
This example uses Shanghai Zone F.
Routing Mode
Select the routing mode.
This example uses Destination Routing Mode.
Effective Immediately
Specify whether to immediately establish the connection. Valid values:
Yes. Start negotiations after the configuration is completed.
No. Start negotiations when inbound traffic is detected.
In this example, Yes is selected.
Customer Gateway
Select the customer gateway to associate with the connection.
This topic uses Customer-Gateway.
Pre-shared key
Enter the pre-shared key for authentication between the on-premises gateway device and the IPsec-VPN connection.
The key must be 1 to 100 characters in length. The key supports digits, uppercase and lowercase letters, and the following special characters:
~`!@#$%^&*()_-+={}[]\|;:',.<>/?. The key cannot contain spaces.If you do not specify a pre-shared key, the system generates a random 16-character string as the pre-shared key. After the IPsec-VPN connection is created, you can click the Edit button to view the system-generated pre-shared key. For more information, see Manage IPsec-VPN connections.
ImportantThe pre-shared key of the IPsec-VPN connection must be the same as the pre-shared key of the peer gateway device. Otherwise, the IPsec-VPN connection cannot be established.
This example uses fddsFF123****.
Enable BGP
Specify whether to enable BGP. BGP is disabled by default.
This topic describes how to enable the Border Gateway Protocol (BGP) feature.
Local ASN
Enter the autonomous system number (ASN) for the IPsec-VPN connection.
In this example, enter 45104.
Encryption Configuration
Configure the IKE and IPsec encryption settings.
Use the default settings except for the following parameters. For more information, see Manage a single-tunnel IPsec-VPN connection.
In the IKE Configurations section, set the DH Group (Perfect Forward Secrecy) parameter to group14.
In the IPsec Configurations section, set the DH Group (Perfect Forward Secrecy) parameter to group14.
NoteYou need to select encryption parameters based on the on-premises gateway device to ensure that the encryption configurations for the IPsec connection are the same as those for the on-premises gateway device.
BGP Configuration
Tunnel CIDR Block
Enter the CIDR block for the tunnel interface.
The tunnel CIDR block must be a /30 subnet within 169.254.0.0/16. It cannot be 169.254.0.0/30, 169.254.1.0/30, 169.254.2.0/30, 169.254.3.0/30, 169.254.4.0/30, 169.254.5.0/30, 169.254.6.0/30, or 169.254.169.252/30.
For this example, enter 169.254.10.0/30.
Local BGP IP address
Enter the BGP IP address for the Alibaba Cloud side of the connection.
The IP address must be within the tunnel CIDR block.
In this topic, use 169.254.10.1.
Advanced Configuration (including route table association and route forwarding)
Specify whether to enable advanced settings. These settings allow the IPsec-VPN connection to automatically advertise and learn routes. Advanced settings are enabled by default.
In this topic, all advanced configurations are enabled by default.
After the IPsec-VPN connection is created, the system automatically assigns it a public IP address. This address is used to establish the tunnel to the data center. You can view this gateway IP address on the IPsec-VPN connection details page.
 Note
NoteThe system assigns a gateway IP address to an IPsec-VPN connection only after the connection is attached to a transit router.
Download the peer configuration.
Return to the IPsec Connections page, find the IPsec-VPN connection that you created, and in the Actions column, click Generate Peer Configuration.
Add the VPN and BGP configurations to the on-premises gateway device.
After you create the IPsec-VPN connection, add the VPN and BGP configurations to your on-premises gateway device. Use the downloaded peer configuration file as a reference. This allows the data center and Alibaba Cloud to establish an IPsec-VPN connection.
NoteIn this example, the software Adaptive Security Appliance (ASA) 9.19.1 is used to describe how to configure a Cisco firewall. The commands may vary with software versions. Consult the documentation or your vendor based on your actual environment during operations. For more information, see Configure local gateways.
The following content contains third-party product information, which is only for reference. Alibaba Cloud does not make guarantees or other forms of commitments for the performance and reliability of third-party products, or the potential impacts of operations performed by using these products.
Log on to the CLI of the Cisco firewall and enter the configuration mode.
ciscoasa> enable Password: ******** # Enter the password for entering the enable mode. ciscoasa# configure terminal # Enter the configuration mode. ciscoasa(config)#View the interface and route configurations.
The Cisco firewall interface configuration is already complete and the interfaces are enabled. The following code shows an example of the interface configuration for this topic.
ciscoasa(config)# show running-config interface ! interface GigabitEthernet0/0 nameif outside1 # The name of the GigabitEthernet 0/0 interface. security-level 0 ip address 211.XX.XX.68 255.255.255.255 # The public IP address of the GigabitEthernet 0/0 interface. ! interface GigabitEthernet0/2 # The interface that connects to the data center. nameif private # The name of the GigabitEthernet 0/2 interface. security-level 100 # The security level of the interface that connects to the data center, which is lower than that of a public interface. ip address 192.168.2.215 255.255.255.0 # The private IP address of the GigabitEthernet 0/2 interface. ! route outside1 47.XX.XX.213 255.255.255.255 192.XX.XX.172 # The route for accessing the public IP address of IPsec-VPN connection on the Alibaba Cloud side. The next hop is a public IP address. route private 192.168.0.0 255.255.0.0 192.168.2.216 # The route that points to the data center.Enable the IKEv2 feature for the interface that connects to the Internet.
crypto ikev2 enable outside1 crypto ikev2 enable outside2Create an IKEv2 policy. Specify the authentication algorithm, encryption algorithm, DH group, and SA lifetime for the IKE phase. These parameters must match the settings on the Alibaba Cloud side.
ImportantWhen you configure an IPsec-VPN connection in the Alibaba Cloud console, you can specify only one value for the Encryption Algorithm, Authentication Algorithm, and DH Group in the IKE Configurations section. We recommend that you also specify only one value for each of these parameters on the Cisco firewall. The values must match the settings on the Alibaba Cloud side.
crypto ikev2 policy 10 encryption aes # Specify the encryption algorithm. integrity sha # Specify the authentication algorithm. group 14 # Specify the DH group. prf sha # The value of the prf parameter must be the same as that of the integrity parameter. By default, these values are the same on the Alibaba Cloud side. lifetime seconds 86400 # Specify the SA lifetime.Create an IPsec proposal and profile. Specify the encryption algorithm, authentication algorithm, DH group, and SA lifetime for the IPsec phase on the Cisco firewall. These parameters must match the settings on the Alibaba Cloud side.
ImportantWhen you configure an IPsec-VPN connection in the Alibaba Cloud console, you can specify only one value for the Encryption Algorithm, Authentication Algorithm, and DH Group in the IPsec Configurations section. We recommend that you also specify only one value for each of these parameters on the Cisco firewall. The values must match the settings on the Alibaba Cloud side.
crypto ipsec ikev2 ipsec-proposal ALIYUN-PROPOSAL # Create an IPsec proposal. protocol esp encryption aes # Specify the encryption algorithm. The ESP protocol is used on the Alibaba Cloud side. Therefore, use the ESP protocol. protocol esp integrity sha-1 # Specify the authentication algorithm. The ESP protocol is used on the Alibaba Cloud side. Therefore, use the ESP protocol. crypto ipsec profile ALIYUN-PROFILE set ikev2 ipsec-proposal ALIYUN-PROPOSAL # Create an IPsec profile and apply the proposal that is created. set ikev2 local-identity address # Set the format of the local ID to IP address, which is the same as the format of the remote ID on the Alibaba Cloud side. set pfs group14 # Specify the Perfect Forward Secrecy (PFS) and DH group. set security-association lifetime seconds 86400 # Specify the time-based SA lifetime. set security-association lifetime kilobytes unlimited # Disable the traffic-based SA lifetime.Create a tunnel group. Specify the pre-shared key for the tunnel. This key must match the key configured on the Alibaba Cloud side.
tunnel-group 47.XX.XX.213 type ipsec-l2l # Set the encapsulation mode of the tunnel to l2l. tunnel-group 47.XX.XX.213 ipsec-attributes ikev2 remote-authentication pre-shared-key fddsFF123**** # Specify the peer pre-shared key for the tunnel, which is the pre-shared key on the Alibaba Cloud side. ikev2 local-authentication pre-shared-key fddsFF123**** # Specify the local pre-shared key for the tunnel, which must be the same as that on the Alibaba Cloud side. !Create a tunnel interface.
interface Tunnel1 #Create a tunnel interface. nameif ALIYUN1 ip address 169.254.10.2 255.255.255.252 #Specify the IP address of the interface. tunnel source interface outside1 #Specify the source address of the tunnel as the GigabitEthernet 0/0 public interface. tunnel destination 47.XX.XX.213 #Specify the destination address of the tunnel as the public IP address of the IPsec-VPN connection on the Alibaba Cloud side. tunnel mode ipsec ipv4 tunnel protection ipsec profile ALIYUN-PROFILE #Apply the IPsec profile ALIYUN-PROFILE on the tunnel. no shutdown #Enable the interface for the tunnel. !Add a BGP configuration to establish a BGP peer relationship between the on-premises gateway device and the IPsec-VPN connection.
router bgp 65530 address-family ipv4 unicast neighbor 169.254.10.1 remote-as 45104 # Specify the BGP peer, which is the IP address of the tunnel on the Alibaba Cloud side. neighbor 169.254.10.1 ebgp-multihop 255 neighbor 169.254.10.1 activate # Activate the BGP peer. neighbor 169.254.10.1 weight 500 # Set the weights of the routes learned through the IPsec-VPN connection to 500, which is lower than the weights of the routes learned through the Express Connect circuit. This ensures that traffic from the data center to the VPC is preferably forwarded through the Express Connect circuit. exit-address-family
Step 4: Test and verify
After you complete the preceding steps, the data center can communicate with the VPC through either the Express Connect circuit or the IPsec-VPN connection. When both links are active, traffic is routed through the Express Connect circuit by default. If the Express Connect circuit fails, traffic automatically switches to the IPsec-VPN connection. The following sections describe how to test network connectivity and verify the active/standby link redundancy.
Before the test, make sure that you understand the security group rules applied to the ECS instance in the VPC and the access control list (ACL) rules applied to the data center. Make sure that the rules allow mutual access between the VPC and the data center. For more information about ECS security group rules, see View security group rules and Add a security group rule.
Test the network connectivity.
Log on to the ECS instance in the VPC. For more information, see Connect to an ECS instance.
On the ECS instance, run the ping command to access a client in the data center.
ping <IP address of the client in the data center>If you receive a response message, a network connection is established between the data center and the VPC, and they can access each other's resources.
Verify the active/standby link redundancy.
From multiple clients in the data center, continuously send access requests to the ECS instance.
ping <IP address of ECS instance> -c 10000Log on to the CEN console and check the traffic monitoring data for the VBR connection. For more information, see View monitoring information about a CEN instance.
Under normal conditions, traffic is transmitted through the Express Connect circuit. You can view the traffic data on the monitoring tab for the VBR connection.
Interrupt the Express Connect circuit connection.
For example, you can disable the interface on the on-premises gateway device that connects to the Express Connect circuit.
Log on to the VPN Gateway console and check the traffic data on the IPsec-VPN connection details page. For more information, see View monitoring information about a CEN instance.
After the Express Connect circuit is interrupted, traffic automatically fails over to the IPsec-VPN connection. You can view the traffic data on the monitoring tab for the IPsec-VPN connection.
Route description
In this topic, the default route configurations are used when the IPsec-VPN, VPC, VBR, and inter-region connections are created. With these default settings, CEN automatically handles route distribution and learning to enable communication between the data center and the VPC. The default route configurations are described in the following sections.