This guide walks you through deploying a gRPC application in a Container Service for Kubernetes (ACK) cluster and configuring an MSE cloud-native gateway to route traffic to it. gRPC runs on HTTP/2 and supports bidirectional streaming, header compression, and multiplexing.
How gRPC routing works
Every gRPC call maps to an HTTP/2 request with a path in the following format:
/{PackageName}.{ServiceName}/{MethodName}For example, calling the Index method of the GRPCBin service in the grpcbin package produces the path:
/grpcbin.GRPCBin/IndexMSE cloud-native gateways match and route gRPC requests based on this path. When you create a route, set the path prefix to the package and service you want to expose.
Prerequisites
Before you begin, make sure that you have:
An MSE cloud-native gateway. For details, see Create an MSE cloud-native gateway
An ACK managed cluster in the same VPC as the gateway. For details, see Create an ACK managed cluster
Step 1: Deploy a gRPC application in the ACK cluster
This example uses grpcbin, an open-source gRPC test server that exposes multiple RPC methods including unary, server streaming, client streaming, and bidirectional streaming. The ACK cluster handles service discovery through CoreDNS with annotation-based service APIs.
For general deployment instructions, see Create a stateless application by using a Deployment.
Kubernetes resource definitions
Apply the following Deployment, ServiceAccount, and Service to your ACK cluster:
The name field in the Kubernetes Service port definition must contain grpc. This tells the gateway to use HTTP/2 for the backend connection.
apiVersion: apps/v1
kind: Deployment
metadata:
name: grpcbin
spec:
replicas: 1
selector:
matchLabels:
app: grpcbin
template:
metadata:
labels:
app: grpcbin
spec:
serviceAccountName: grpcbin
containers:
- image: docker.io/moul/grpcbin
imagePullPolicy: IfNotPresent
name: grpcbin
ports:
- containerPort: 9000
- containerPort: 9001
resources:
requests:
cpu: '1'
memory: 2Gi
limit:
cpu: '1'
memory: 2Gi
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: grpcbin
---
apiVersion: v1
kind: Service
metadata:
name: grpcbin-grpc
labels:
app: grpcbin
spec:
ports:
- name: grpc
port: 9000
targetPort: 9000
selector:
app: grpcbinNotable configuration details:
| Item | Value | Description |
|---|---|---|
Service port name | grpc | Signals the gateway to use HTTP/2 for the backend connection |
| Container ports | 9000, 9001 | Port 9000 serves gRPC traffic |
| Resource requests and limits | 1 CPU, 2 GiB memory | Both requests and limits are set to the same values |
Proto definition
The grpcbin service defines the following RPC methods:
syntax = "proto3";
package grpcbin;
service GRPCBin {
rpc Index(EmptyMessage) returns (IndexReply) {}
// Called without parameters. Returns an empty response.
rpc Empty(EmptyMessage) returns (EmptyMessage) {}
// Echoes the request parameters back.
rpc DummyUnary(DummyMessage) returns (DummyMessage) {}
// Server streaming: returns 10 response messages.
rpc DummyServerStream(DummyMessage) returns (stream DummyMessage) {}
// Client streaming: receives 10 requests, returns the last request body.
rpc DummyClientStream(stream DummyMessage) returns (DummyMessage) {}
// Bidirectional streaming.
rpc DummyBidirectionalStreamStream(stream DummyMessage) returns (stream DummyMessage) {}
// Returns a specified gRPC error.
rpc SpecificError(SpecificErrorRequest) returns (EmptyMessage) {}
// Returns a random error.
rpc RandomError(EmptyMessage) returns (EmptyMessage) {}
// Returns request headers.
rpc HeadersUnary(EmptyMessage) returns (HeadersMessage) {}
// Returns no response.
rpc NoResponseUnary(EmptyMessage) returns (EmptyMessage) {}
}
message HeadersMessage {
message Values {
repeated string values = 1;
}
map<string, Values> Metadata = 1;
}
message SpecificErrorRequest {
uint32 code = 1;
string reason = 2;
}
message EmptyMessage {}
message DummyMessage {
message Sub {
string f_string = 1;
}
enum Enum {
ENUM_0 = 0;
ENUM_1 = 1;
ENUM_2 = 2;
}
string f_string = 1;
repeated string f_strings = 2;
int32 f_int32 = 3;
repeated int32 f_int32s = 4;
Enum f_enum = 5;
repeated Enum f_enums = 6;
Sub f_sub = 7;
repeated Sub f_subs = 8;
bool f_bool = 9;
repeated bool f_bools = 10;
int64 f_int64 = 11;
repeated int64 f_int64s= 12;
bytes f_bytes = 13;
repeated bytes f_bytess = 14;
float f_float = 15;
repeated float f_floats = 16;
}
message IndexReply {
message Endpoint {
string path = 1;
string description = 2;
}
string description = 1;
repeated Endpoint endpoints = 2;
}Step 2: Configure the gateway to route gRPC requests
Connect the gateway to the grpcbin backend by completing three tasks: adding the ACK cluster as a service source, importing the service, and creating a route.
Add a service source
Log on to the MSE console. In the top navigation bar, select a region.
In the left-side navigation pane, choose Cloud-native Gateway > Gateways. Click the name of the gateway.
In the left-side navigation pane, click Routes. Click the Sources tab.
Click Add Source. In the Add Source panel, set Source Type to Container Service, configure the following parameters, and then click OK.
| Parameter | Description |
|---|---|
| ACK/ACK Serverless Cluster | Select the cluster that hosts the backend services. Important The gateway must be in the same VPC as the cluster. When you create a gateway and select a VPC, clusters in that VPC are automatically discovered. |
| Listen to Kubernetes Ingress | Turn on to have the gateway automatically detect Ingress resource changes and apply the corresponding domain and route configurations. Turn off to stop listening. Exercise caution when you turn off this switch. Important Domain names and routes configured manually in the MSE console take priority over those from Ingress resources. |
| Ingress Class | Restrict which Ingress resources the gateway monitors. Leave blank to monitor all Ingress resources. If set to a value such as nginx, the gateway monitors Ingress resources whose class annotation or Spec.IngressClassName matches, plus any Ingress resources not associated with a class. |
| Namespace | Restrict monitoring to Ingress resources in a specific namespace. Leave blank to monitor all namespaces. |
| Update Ingress Status | Set to Open to update the Ingress IP address to the Server Load Balancer (SLB) instance IP associated with the gateway. Note Requires gateway version 1.2.9 or later. |
| Security Group Rules | Security groups are configured in the ACK cluster node pool. External access to in-cluster services typically requires opening the relevant ports. For details, see Configure security group rules. |
Add a service
Log on to the MSE console. In the top navigation bar, select a region.
In the left-side navigation pane, choose Cloud-native Gateway > Gateways. Click the name of the gateway.
In the left-side navigation pane, click Routes. Click the Services tab.
Click Add Service. In the Add Service panel, configure the following parameters and click OK.
| Parameter | Description |
|---|---|
| Source Type | Select Container Service. |
| Namespace | Select the namespace of the cluster. |
| Services | Select one or more services from the list. Choose the grpcbin-grpc service. |
Create a route to the grpcbin service
Log on to the MSE console. In the top navigation bar, select a region.
In the left-side navigation pane, choose Cloud-native Gateway > Gateways. Click the name of the gateway.
In the left-side navigation pane, click Routes. Click the Routes tab.
Click Add Route. Configure the following parameters and click Save and Advertise. For the full parameter reference, see Create a route.
| Parameter | Description |
|---|---|
| Routing Rule Name | Enter grpc. |
| Domain name | Select the default wildcard domain *. |
| Path | Select Prefix and enter /grpcbin.GRPCBin. This matches all methods under the GRPCBin service. Note The gRPC path format is |
| Scenario | Select Single Service. |
| Backend Service | Select the grpcbin-grpc service and set the service port to 9000. |
Verify the result
After the route is published, test the gRPC service to confirm traffic flows through the gateway.
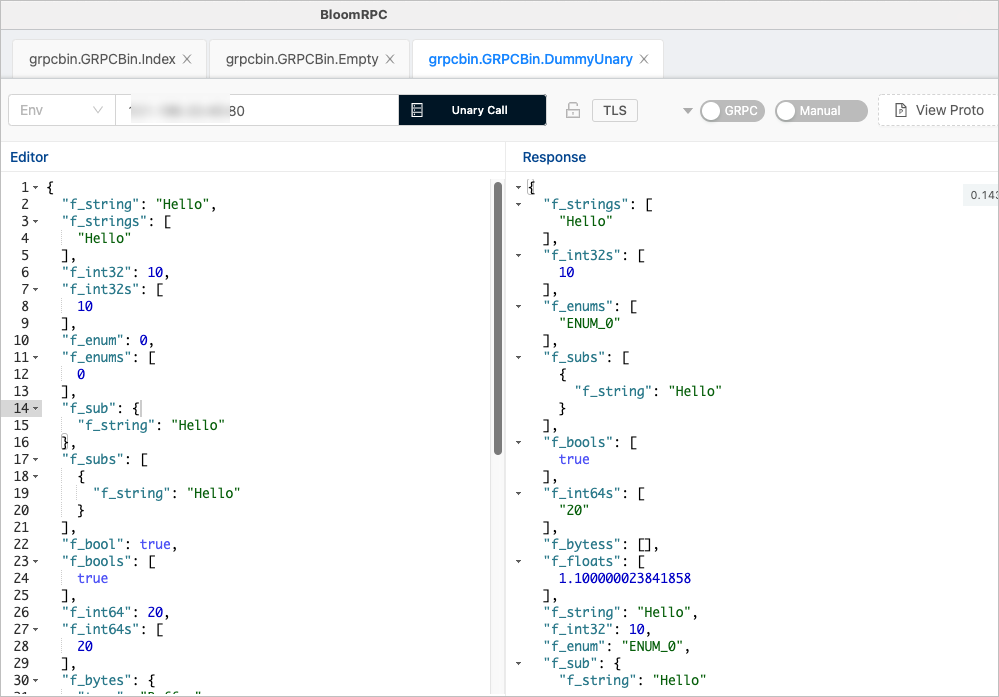
Use bloomrpc to test gRPC service availability. If a response is returned, the gRPC service is available. You can also use other gRPC clients for testing.
What's next
Create a route -- explore advanced routing options such as header-based matching and traffic splitting
Configure security group rules -- open ports required for gRPC traffic