Application performance issues -- such as JVM garbage collection spikes, slow response times, or rising error rates -- require timely detection. Alert rules in Enterprise Distributed Application Service (EDAS) monitor these metrics and notify your team through specified contacts or DingTalk groups when thresholds are crossed, so you can respond before users are affected.
Prerequisites
Before you begin, make sure that you have:
Application Monitoring connected to EDAS. For more information, see Application Monitoring overview
Create an alert rule
An alert rule defines which metric to watch, what threshold triggers an alert, and who gets notified.
Log on to the EDAS console.
In the left-side navigation pane, click Application Management > Applications. In the top navigation bar, select a region. In the upper part of the page, select a microservices namespace. Select Kubernetes Cluster from the Cluster Type drop-down list. Then, find the application and click the application name.
In the left-side navigation pane, choose Alert Management > Alert Rules.
On the Application Monitoring Alert Rules page, click Create Application Monitoring Alert Rule.
Configure the parameters described in the following sections and click Save.
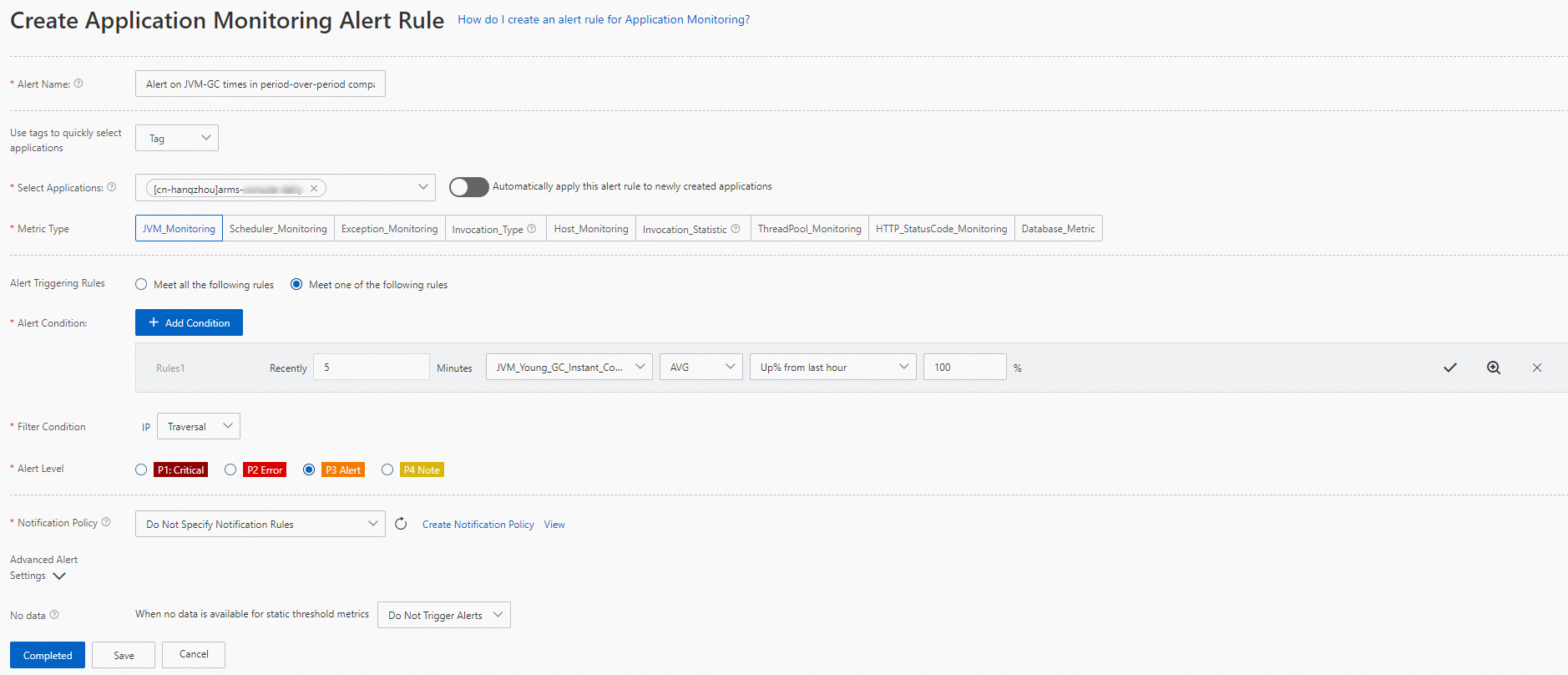
Alert name and scope
| Parameter | Description |
|---|---|
| Alert Name | A descriptive name for this rule. Example: Alert on JVM-GC occurrences in period-over-period comparison. |
| Select Applications | The application this alert rule applies to. |
| Metric Type | The type of metric to monitor, such as JVM metrics, host metrics, or exception metrics. The available options for Alert Condition and Filter Condition change based on the metric type you select. For the full list of supported metrics, see Alert rule metrics. |
Alert triggering conditions
Define when an alert fires and how metric dimensions are filtered.
| Parameter | Description |
|---|---|
| Alert Triggering Rules | How multiple conditions combine: Meet all the following rules (AND logic -- all conditions must be met) or Meet One of the Following Rules (OR logic -- any single condition triggers the alert). |
| Alert Condition | The threshold expression that triggers the alert. Click +Add Condition to define each condition. For example, trigger an alert when the average number of JVM full garbage collection (GC) events in the last 5 minutes increases by 100% compared to the previous hour. After you configure a condition, click the confirm icon to save it. To preview the metric trend, click the magnify icon. To delete a condition, click the delete icon. To add more conditions, click +Add Condition again. |
Preview the metric trend before saving to verify that your condition matches expected behavior.
Filter conditions
The Filter Condition parameter controls which dimension values are included when evaluating the alert condition.
| Filter | Behavior |
|---|---|
| Traversal | Evaluates each value of the selected metric type individually. |
| No | Aggregates (sums) all values of the selected metric type. |
| = | Includes only the specified dimension values. |
| != | Excludes dimension values that match the specified value. |
| Contain | Includes only dimension values that contain the specified string. |
| Do Not Contain | Excludes dimension values that contain the specified string. |
| Match Regular Expression | Includes only dimension values that match the specified regular expression. |
Severity and notifications
| Parameter | Description |
|---|---|
| Alert Level | The severity level: P4 (lowest), P3, P2, or P1 (highest). |
| Notification Policy | Controls how alert notifications are delivered. Without a notification rule, Application Real-Time Monitoring Service (ARMS) sends notifications only when the dispatch rule in the notification policy matches. With a notification rule, ARMS sends notifications through the method specified in the policy. Select an existing notification policy or create one. For more information, see Create and manage a notification policy. To review existing policies, click View all notification policies. |
Advanced alert settings
| Parameter | Description |
|---|---|
| No Data | Handles data anomalies such as missing data, abnormal composite metrics, and abnormal period-over-period comparison results. If the metric data does not meet the specified conditions, the system automatically sets the value to 0 or 1, or suppresses the alert. For more information, see Terminologies. |
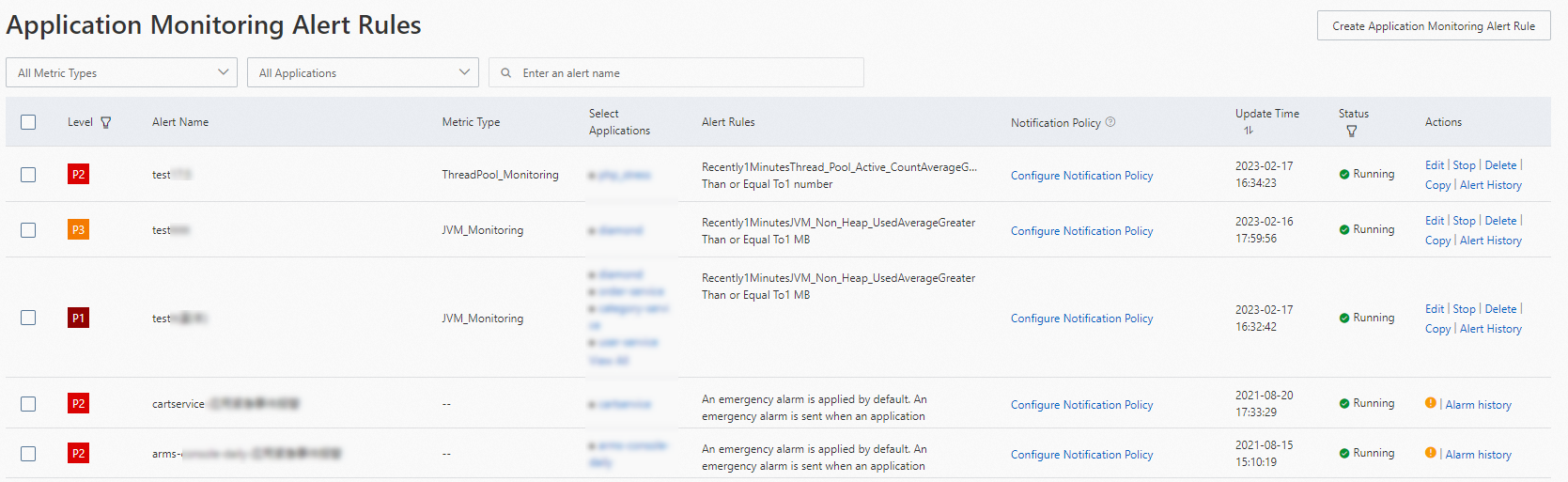
Manage alert rules
After you create alert rules, they appear on the Application Monitoring Alert Rules page. You can search for specific rules and perform management actions.
Find an alert rule
Log on to the EDAS console.
In the left-side navigation pane, click Application Management > Applications. In the top navigation bar, select a region. In the upper part of the page, select a microservices namespace. Select Kubernetes Cluster from the Cluster Type drop-down list. Then, find the application and click the application name.
In the left-side navigation pane, choose Alert Management > Alert Rules.
(Optional) On the Application Monitoring Alert Rules page, select Rule name from the drop-down list, enter the rule name in the search box, and then click the search icon.
NoteThe search supports fuzzy matching, so entering a keyword from the rule name is sufficient.
Available actions
In the alert rule list, find the rule and use the following actions in the Actions column:
| Action | Description |
|---|---|
| Edit | Modify the rule configuration. |
| Start | Enable a disabled rule. |
| Stop | Disable an active rule. |
| Delete | Permanently remove the rule. |
| Copy | Duplicate the rule to create a similar one. |
| Alert History | View past alert events triggered by this rule. |