This topic describes how to configure single sign-on (SSO) from Shibboleth to CloudSSO.
Preparations
Install Shibboleth, Apache Tomcat, and a Lightweight Directory Access Protocol (LDAP)-authenticated server.
The configurations of Shibboleth that are described in this topic are suggestions and used only to help you understand the end-to-end SSO process from Shibboleth to Alibaba Cloud. Alibaba Cloud does not provide consulting services for the configurations of Shibboleth.
Step 1: Download the SAML SP metadata file of Alibaba Cloud
Log on to the CloudSSO console.
In the left-side navigation pane, click Settings.
In the SSO Logon section, download the Security Assertion Markup Language (SAML) service provider (SP) metadata file and save it as
/opt/shibboleth-idp/metadata/aliyun-cloudsso-metadata.xml.Save the
Entity IDof the SP for subsequent use.
Step 2: Register Alibaba Cloud with Shibboleth
Configure the metadata file that you obtained in Step 1: Download the SAML SP metadata file of Alibaba Cloud in the /opt/shibboleth-idp/conf/metadata-providers.xml file to register Alibaba Cloud with Shibboleth.
<!--
<MetadataProvider id="LocalMetadata" xsi:type="FilesystemMetadataProvider" metadataFile="PATH_TO_YOUR_METADATA"/>
-->
<!-- Find the code that is displayed in the preceding line in the file and replace the code with the code that is displayed in the following line. -->
<MetadataProvider id="AliyunMetadata" xsi:type="FilesystemMetadataProvider" metadataFile="%{idp.home}/metadata/aliyun-cloudsso-metadata.xml"/>Step 3: Configure the user attributes that are returned by Shibboleth
Modify the
/opt/shibboleth/conf/services.xmlfile.The original configuration file contains the
attribute-resolver.xmlfield and does not provide complete configuration information. You must replace the field with theattribute-resolver-full.xmlfield to provide complete configuration information.<value>%{idp.home}/conf/attribute-resolver.xml</value> <!-- Find the code that is displayed in the preceding line in the file and replace the code with the code that is displayed in the following line. --> <value>%{idp.home}/conf/attribute-resolver-full.xml</value>Modify the
/opt/shibboleth/conf/attribute-resolver-full.xmlfile.Configure the user attributes that are returned by Shibboleth in the /opt/shibboleth/conf/attribute-resolver-full.xml file. In this example, the
mailfield is used as a user attribute.<!-- ========================================== --> <!-- Attribute Definitions --> <!-- ========================================== --> <!-- Schema: Core schema attributes--> <!-- Find the code that is displayed in the preceding line in the file and append the code that is displayed in the following line. --> <AttributeDefinition xsi:type="Simple" id="mail"> <InputDataConnector ref="myLDAP" attributeNames="mail" /> <AttributeEncoder xsi:type="SAML1String" name="urn:mace:dir:attribute-def:mail" encodeType="false" /> <AttributeEncoder xsi:type="SAML2String" name="urn:oid:0.9.2342.19200300.100.1.3" friendlyName="mail" encodeType="false" /> </AttributeDefinition>Read the configuration information that is contained in
/opt/shibboleth/conf/ldap.propertiesin the /opt/shibboleth/conf/attribute-resolver-full.xml file to establish a connection to the LDAP server.<!-- Example LDAP Connector --> <!-- <DataConnector id="myLDAP" xsi:type="LDAPDirectory" ldapURL="%{idp.attribute.resolver.LDAP.ldapURL}" baseDN="%{idp.attribute.resolver.LDAP.baseDN}" principal="%{idp.attribute.resolver.LDAP.bindDN}" principalCredential="%{idp.attribute.resolver.LDAP.bindDNCredential}" useStartTLS="%{idp.attribute.resolver.LDAP.useStartTLS:true}" ... </DataConnector> --> <!-- Find the code that is displayed in the preceding line in the file and replace the code with the code that is displayed in the following line. --> <DataConnector id="myLDAP" xsi:type="LDAPDirectory" ldapURL="%{idp.attribute.resolver.LDAP.ldapURL}" baseDN="%{idp.attribute.resolver.LDAP.baseDN}" principal="%{idp.attribute.resolver.LDAP.bindDN}" principalCredential="%{idp.attribute.resolver.LDAP.bindDNCredential}" useStartTLS="%{idp.attribute.resolver.LDAP.useStartTLS}" connectTimeout="%{idp.attribute.resolver.LDAP.connectTimeout}" responseTimeout="%{idp.attribute.resolver.LDAP.responseTimeout}"> <FilterTemplate> <![CDATA[ %{idp.attribute.resolver.LDAP.searchFilter} ]]> </FilterTemplate> </DataConnector>
Add an attribute filter to the
/opt/shibboleth/conf/attribute-filter.xmlfile.Replace the
valueattribute in thePolicyRequirementRuletag with theEntity IDthat you obtained in Step 1: Download the SAML SP metadata file of Alibaba Cloud.<AttributeFilterPolicyGroup id="ShibbolethFilterPolicy" xmlns="urn:mace:shibboleth:2.0:afp" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="urn:mace:shibboleth:2.0:afp http://shibboleth.net/schema/idp/shibboleth-afp.xsd"> <!-- Find the code that is displayed in the preceding line in the file and append the code that is displayed in the following line. --> <AttributeFilterPolicy id="aliyun"> <PolicyRequirementRule xsi:type="Requester" value="[entityID]" /> <AttributeRule attributeID="mail"> <PermitValueRule xsi:type="ANY" /> </AttributeRule> </AttributeFilterPolicy>
Step 4: Configure the NameID attribute in the SAML response
Configure the NameID attribute in the
/opt/shibboleth/conf/relying-party.xmlfile.Replace the
relyingPartyIdsattribute in thebeantag with theEntity IDthat you obtained in Step 1: Download the SAML SP metadata file of Alibaba Cloud.<!-- Override example that identifies a single RP by name and configures it for SAML 2 SSO without encryption. This is a common "vendor" scenario. --> <!-- <bean parent="RelyingPartyByName" c:relyingPartyIds="https://sp.example.org"> <property name="profileConfigurations"> <list> <bean parent="SAML2.SSO" p:encryptAssertions="false" /> </list> </property> </bean> --> <!-- Find the code that is displayed in the preceding line in the file and replace the code with the code that is displayed in the following line. --> <bean parent="RelyingPartyByName" c:relyingPartyIds="[entityID]"> <property name="profileConfigurations"> <list> <bean parent="SAML2.SSO" p:encryptAssertions="false" p:nameIDFormatPrecedence="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress" /> </list> </property> </bean>Configure the generation method of the NameID attribute in the
/opt/shibboleth/conf/saml-nameid.xmlfile.<!-- Find the following code. Comment out the code to make the configuration into effect.--> <bean parent="shibboleth.SAML2AttributeSourcedGenerator" p:omitQualifiers="true" p:format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress" p:attributeSourceIds="#{ {'mail'} }" /> <bean parent="shibboleth.SAML1AttributeSourcedGenerator" p:omitQualifiers="true" p:format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress" p:attributeSourceIds="#{ {'mail'} }" />Configure information about the NameID attribute in
/opt/shibboleth/conf/saml-nameid.properties.idp.nameid.saml2.default = urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress idp.persistentId.useUnfilteredAttributes = true idp.persistentId.encoding = BASE32
Step 5: Obtain the metadata file of the SAML IdP in Shibboleth
Restart Apache Tomcat to allow the preceding configurations to take effect.
Access
https://<The IP address of the LDAP server>/idp/shibbolethand save the metadata file to your computer.
Step 6: Enable SSO in the CloudSSO console
In the left-side navigation pane of the CloudSSO console, click Settings.
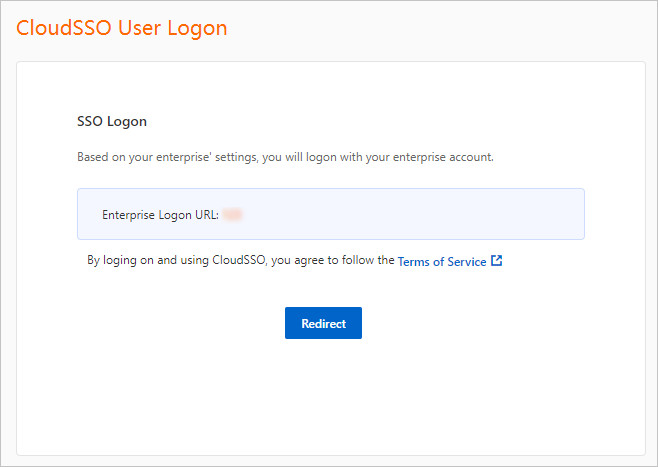
In the SSO Logon section of the Settings page, click Configure IdP.
In the Configure IdP dialog box, select Upload Metadata File.
Click Upload File to upload the metadata file that you obtained in Step 5: Obtain the metadata file of the SAML IdP in Shibboleth.
Turn on the SSO switch to enable SSO.
NoteAfter SSO is enabled, username-password logon is automatically disabled. SSO takes effect on all users. After you enable SSO, all users must use the SSO logon method.
Step 7: Create a CloudSSO user in the CloudSSO console
In the CloudSSO console, create a CloudSSO user who has the same name as the user in Shibboleth.
In the left-side navigation pane of the CloudSSO console, choose .
On the User page, click Create User.
In the Create User panel, configure Username.
In this example, the username
testUser@testdomain.alicloud.comis used.Turn on Status.
Click Close.
(Optional) Step 8: Grant permissions to the CloudSSO user
If you want a CloudSSO user to access specific resources within the specified members in a resource directory after the user logs on to the user portal by using the SSO method, you must create access configurations that define access permissions. Then, you must assign the access permissions on the members to the user.
Create access configurations and specify policies in the CloudSSO console.
For more information, see Create an access configuration.
Assign access permissions on the accounts in your resource directory to the CloudSSO user.
For more information, see Assign access permissions on the accounts in a resource directory.
Verify the configuration results
After you complete the preceding configurations, you can initiate SSO from Alibaba Cloud or Shibboleth.
Initiate SSO from Alibaba Cloud
Log on to the CloudSSO console. Go to the Overview page and copy the URL that is used to log on to the user portal.
Open a browser, paste the copied URL, and then press Enter.
Click Redirect. You are redirected to the logon page of Shibboleth.
On the logon page of Shibboleth , enter the username testUser and its password and click Log On.
After the logon succeeds, you are redirected to the user portal.
Access the Alibaba Cloud resources on which you have permissions.
Initiate SSO from Shibboleth
Access
https://<The IP address of the LDAP server>/idp/profile/SAML2/Unsolicited/SSO?providerId=<entityID>.Replace
<entityID>with theEntity IDthat you obtained in Step 1: Download the SAML SP metadata file of Alibaba Cloud.On the logon page of Shibboleth, enter the username testUser and its password and click Log On.
After the logon succeeds, you are redirected to the user portal.
Access the Alibaba Cloud resources on which you have permissions.
FAQ
If issues occur when you verify the configuration results, you can identify the issues by using the /opt/shibboleth-idp/logs/idp-process.log file. The following section provides answers to some frequently asked questions:
What do I do if an exception occurs when I use a valid username and password to log on to Shibboleth?
View the error message in the /opt/shibboleth-idp/logs/idp-process.log file. If the ValidateUsernamePassword error message is displayed, view the connection configurations and deployment of your LDAP server. Make sure the code that must be commented out is commented out and that no extra spaces exist.
What do I do if the system does not respond when I log on to Shibboleth and the unable to connect to the ldap error message is displayed?
Check whether the connection configurations of your LDAP server in the ldap.properties and attribute-resolver-full.xml files are correct.
What do I do if the The NameID is missing error message is displayed when I am redirected to Alibaba Cloud?
Check whether the mail field is correctly mapped as an attribute in Step 3: Configure the user attributes that are returned by Shibboleth. Check whether the NameID attribute is correctly configured in Step 4: Configure the NameID attribute in the SAML response.
What do I do if the Unsupported Request error message is displayed when I access https://<The IP address of your LDAP server>/idp/profile/SAML2/Unsolicited/SSO?providerId=<entityID>?
Check whether the entityId field is correctly specified. Make sure that the values of the entityId fields in the metadata file, attribute-filter.xml file, and relying-party.xml file are the same.
What do I do if the The response signature is invalid error message is displayed when I am redirected to Alibaba Cloud?
Re-upload the metadata file of Shibboleth to Alibaba Cloud.