Resource Access Management (RAM) allows you to manage the permissions of your Alibaba Cloud account and its RAM users separately. You can grant different permissions to different RAM users to avoid security risks caused by disclosure of the AccessKey pair of your Alibaba Cloud account.
Background information
Enterprise A has activated ApsaraMQ for Kafka and wants to grant different permissions to its employees with different duties to perform operations on ApsaraMQ for Kafka resources, such as instances, topics, and consumer groups. Employees with different duties require different permissions. Enterprise A has the following requirements:
For security purposes, the enterprise does not want to disclose the AccessKey pair of its Alibaba Cloud account to employees. Instead, it prefers to create different RAM users for employees and grant different permissions to these RAM users.
Only RAM users who are granted permissions can manage resources. Resource usage and costs are not calculated separately for each RAM user. All expenses are billed to the Alibaba Cloud account of Enterprise A.
Enterprise A can revoke the permissions granted to RAM users and delete RAM users at any time.
Step 1: Create RAM users
Enterprise A uses its Alibaba Cloud account to log on to the RAM console and create RAM users.
Procedure
Log on to the RAM console by using an Alibaba Cloud account or a RAM user who has administrative rights.
In the left-side navigation pane, choose .
On the Users page, click Create User.
In the User Account Information section of the Create User page, configure the following parameters:
Logon Name: The logon name can be up to 64 characters in length, and can contain letters, digits, periods (.), hyphens (-), and underscores (_).
Display Name: The display name can be up to 128 characters in length.
Tag: Click the
 icon and enter a tag key and a tag value. You can add one or more tags to the RAM user. This way, you can manage the RAM user based on the tags.
icon and enter a tag key and a tag value. You can add one or more tags to the RAM user. This way, you can manage the RAM user based on the tags.
NoteYou can click Add User to create multiple RAM users at a time.
In the Access Mode section, select an access mode and configure the required parameters.
To ensure the security of your Alibaba Cloud account, we recommend that you select only one access mode for the RAM user. This way, the RAM user for an individual is separated from the RAM user for a program.
Console Access
If the RAM user represents an individual, we recommend that you select Console Access for the RAM user. This way, the RAM user can use a username and password to access Alibaba Cloud. If you select Console Access, you must configure the following parameters:
Set Console Password: You can select Automatically Regenerate Default Password or Reset Custom Password. If you select Reset Custom Password, you must specify a password. The password must meet the complexity requirements. For more information, see Configure a password policy for RAM users.
Password Reset: specifies whether the RAM user is required to reset the password upon the next logon.
Enable MAF: specifies whether to enable multi-factor authentication (MFA) for the RAM user. After you enable MFA, you must bind an MFA device to the RAM user or allow the RAM user to bind an MFA device. For more information, see Bind an MFA device to a RAM user.
OpenAPI Access
If the RAM user represents a program, we recommend that you select OpenAPI Access for the RAM user. This way, the RAM user can use an AccessKey pair to access Alibaba Cloud. If you select OpenAPI Access, the system automatically generates an AccessKey ID and AccessKey secret for the RAM user. For more information, see Obtain an AccessKey pair.
ImportantAn AccessKey secret for a RAM user is displayed only after you click Create AccessKey. You cannot query the AccessKey secret in subsequent operations. Therefore, you must back up your AccessKey secret.
Click OK.
Complete security verification as prompted.
Step 2: Grant permissions to RAM users
Method 1: Grant permissions to a RAM user on the Users page
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Users page, find the required RAM user, and click Add Permissions in the Actions column.

You can also select multiple RAM users and click Add Permissions in the lower part of the page to grant permissions to the RAM users at a time.
In the Grant Permission panel, grant permissions to the RAM user.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to grant a RAM user the permissions to manage a specific ECS instance.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. The current RAM user is automatically selected.
Configure the Policy parameter.
A policy contains a set of permissions. Policies can be classified into system policies and custom policies. You can select multiple policies at a time.
System policies: policies that are created by Alibaba Cloud. You can use but cannot modify these policies. Version updates of the policies are maintained by Alibaba Cloud. For more information, see Services that work with RAM.
NoteThe system automatically identifies high-risk system policies, such as AdministratorAccess and AliyunRAMFullAccess. We recommend that you do not grant unnecessary permissions by attaching high-risk policies.
Custom policies: You can manage and update custom policies based on your business requirements. You can create, update, and delete custom policies. For more information, see Create a custom policy.
Click Grant permissions.
Click Close.
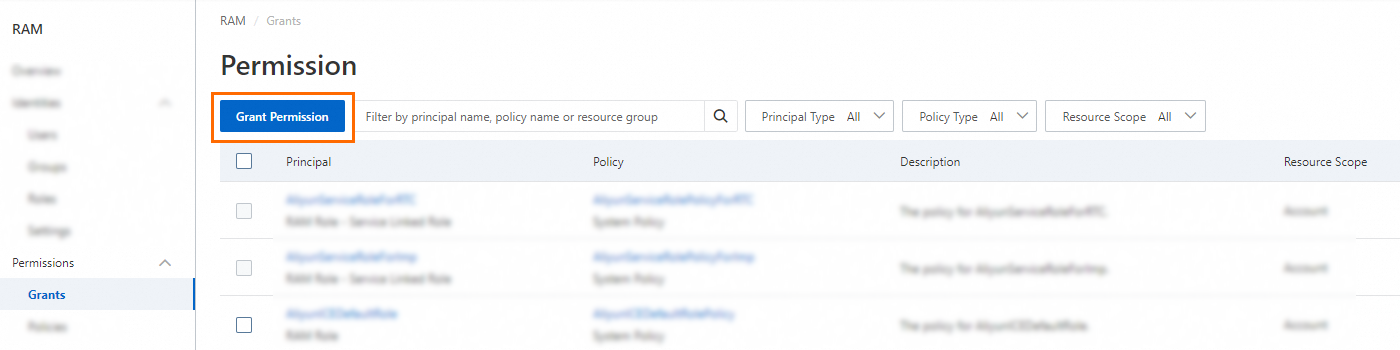
Method 2: Grant permissions to a RAM user on the Grants page
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Permission page, click Grant Permission.
In the Grant Permission panel, grant permissions to the RAM user.
Configure the Resource Scope parameter.
Account: The authorization takes effect on the current Alibaba Cloud account.
Resource Group: The authorization takes effect on a specific resource group.
ImportantIf you select Resource Group for the Resource Scope parameter, make sure that the required cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to grant a RAM user the permissions to manage a specific ECS instance.
Configure the Principal parameter.
The principal is the RAM user to which you want to grant permissions. You can select multiple RAM users at a time.
Configure the Policy parameter.
A policy contains a set of permissions. Policies can be classified into system policies and custom policies. You can select multiple policies at a time.
System policies: policies that are created by Alibaba Cloud. You can use but cannot modify these policies. Version updates of the policies are maintained by Alibaba Cloud. For more information, see Services that work with RAM.
NoteThe system automatically identifies high-risk system policies, such as AdministratorAccess and AliyunRAMFullAccess. We recommend that you do not grant unnecessary permissions by attaching high-risk policies.
Custom policies: You can manage and update custom policies based on your business requirements. You can create, update, and delete custom policies. For more information, see Create a custom policy.
Click Grant permissions.
Click Close.
What to do next
Employees of Enterprise A can use RAM users to access ApsaraMQ for Kafka by using the following methods:
Console
Open the RAM User Logon page in a browser.
On the RAM User Logon page, enter the logon name of the RAM user, click Next, enter the password, and then click Log On.
NoteThe logon name of the RAM user is in the format of <$username>@<$AccountAlias> or <$username>@<$AccountAlias>.onaliyun.com. <$AccountAlias> is the alias of the RAM user. If no alias is set, use the ID of the Alibaba Cloud account.
API
Use the AccessKey ID and AccessKey secret of the RAM user in code to make an API request to access ApsaraMQ for Kafka.