You can use the network acceleration feature to create custom rules to allow an Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan to work together with an Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Chinese Mainland Acceleration (CMA) mitigation plan. If no attacks occur after you enable the network acceleration feature, service access is accelerated by using the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan. If attacks occur, traffic is switched to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan for scrubbing. This way, only service traffic is forwarded to the origin server.
Prerequisites
An Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan is purchased.
For more information, see References.
An Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan is purchased.
ImportantThe clean bandwidth and clean queries per second (QPS) of the instance must meet the protection requirements of your service.
For more information, see Purchase an Anti-DDoS Proxy instance.
Your website service is added to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan and the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan.
For more information, see Add one or more websites.
Both the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan and the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan forward traffic as expected.
For more information, see Verify the forwarding configurations on your on-premises computer.
Background information
The network acceleration feature is suitable for the scenario in which services are deployed outside the Chinese mainland but most users of the services are located in the Chinese mainland. In this scenario, if you use only the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan to protect your service, the access latency of users in the Chinese mainland increases.
You can purchase an Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan and an Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan. This way, if no attacks occur, service access is accelerated by using the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan. If attacks occur, traffic is switched to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan for scrubbing.
The following figure shows how the network acceleration feature works. For more information, see Configure an Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan. 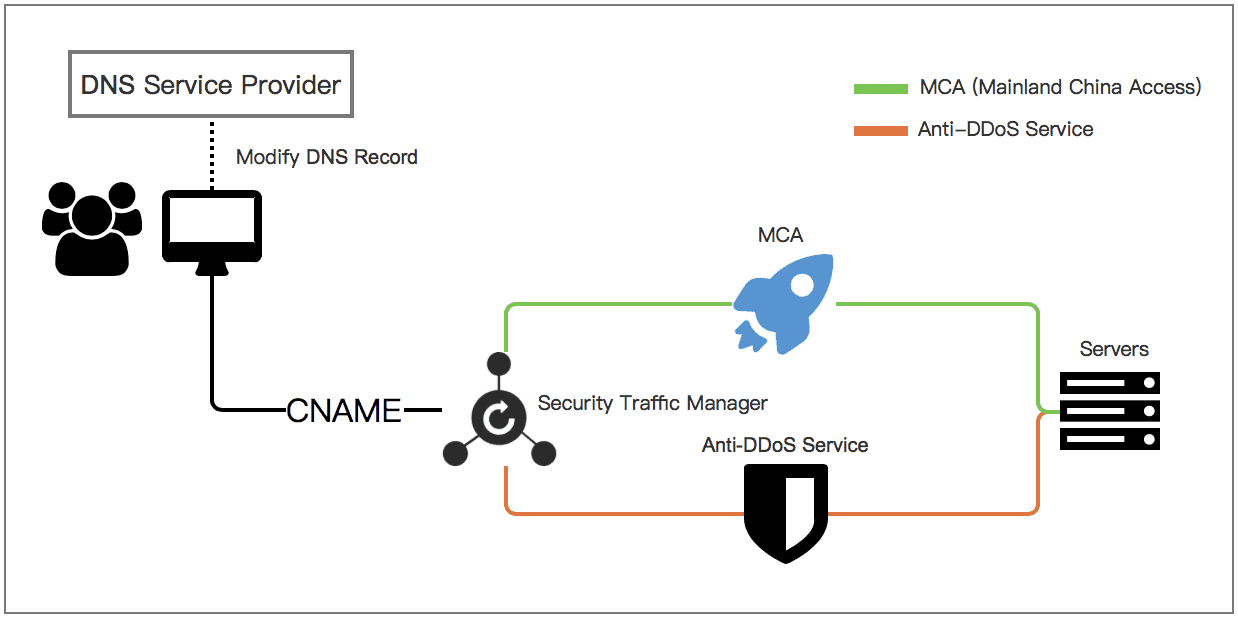
Create a network acceleration rule
Log on to the Anti-DDoS Proxy console.
In the top navigation bar, select Outside Chinese Mainland.
If you select this region, you are redirected to the Anti-DDoS Proxy (Outside Chinese Mainland) console.
In the left-side navigation pane, choose .
- On the General tab, click Create Rule.
In the Add Rule panel, configure a network acceleration rule and click Next.
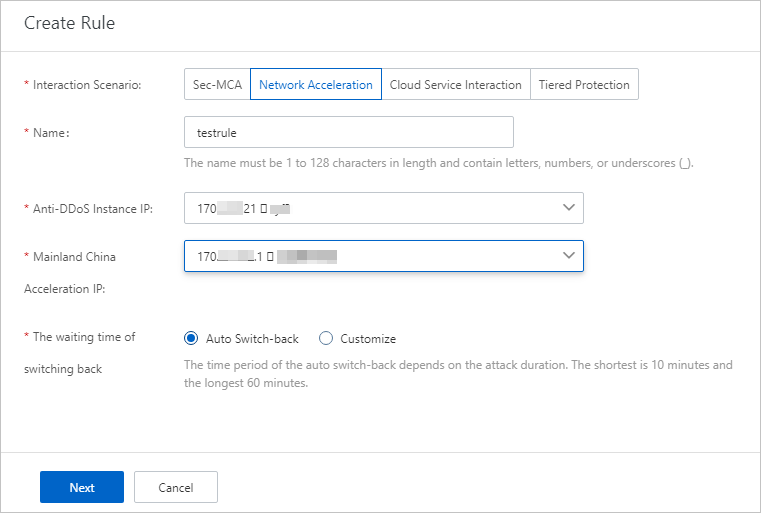
Parameter
Description
Interaction Scenario
Select Network Acceleration.
Rule Name
Enter a name for the rule.The name can be up to 128 characters in length and can contain letters, digits, and underscores (_).
Anti-DDoS Pro
Select an Anti-DDoS Pro or Anti-DDoS Premium instance.CMA IP Address
Select the IP address of the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan.
Waiting Time of Switchback
Specify the waiting time before traffic is switched back. Valid values:
Automatic Switchback: the waiting time before traffic is automatically switched back based on the duration of attacks. Valid values: 10 to 60. Unit: minutes.
Custom: the custom waiting time before traffic is switched back. Valid values: 30 to 120. Unit: minutes. To prevent frequent switchover operations, we recommend that you specify a waiting time of 60 minutes.
- Change the DNS records of the domain name as prompted and click Complete. For the cloud service interaction rule to take effect, you must change the DNS records of your domain name on the website of the DNS service provider to map the domain name to the CNAME provided by Sec-Traffic Manager. If your DNS service is provided by Alibaba Cloud DNS, you need only to change the DNS records in the Alibaba Cloud DNS console.Important After you change the DNS records of your domain name, the cloud service interaction rule takes effect. Before you change the DNS records, we recommend that you modify the hosts file on your computer to verify the cloud service interaction rule. This helps avoid incompatibility issues caused by inconsistent back-to-origin policies. Alibaba Cloud CDN (CDN) allows you to change the origin host for back-to-origin requests. However, you cannot use Anti-DDoS Pro or Anti-DDoS Premium to change the origin host for back-to-origin requests. If you use CDN together with Anti-DDoS Pro or Anti-DDoS Premium to retrieve data from an Object Storage Service (OSS) object, the normal traffic that is forwarded by Anti-DDoS Pro or Anti-DDoS Premium cannot be identified by OSS. As a result, your services are interrupted. For more information about origin hosts, see Origin hosts.
For more information about how to verify traffic forwarding rules, see Verify the forwarding configurations on your local computer.
For more information about how to change the DNS records of a domain name, see Change the CNAME record to redirect traffic to Sec-Traffic Manager.
If no attacks occur after a network acceleration rule is created, the service access of users in the Chinese mainland is accelerated by using the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan. If attacks occur, traffic is switched to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan for scrubbing. This way, only service traffic is forwarded to the origin server. If traffic is automatically switched to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan, the instance switches traffic back to the Anti-DDoS Proxy (Outside Chinese Mainland) of the CMA mitigation plan when the attacks stop and the waiting time that you specify elapses.
In addition to automatic switchover, you can also manually switch traffic to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the Insurance or Unlimited mitigation plan and then manually switch traffic back to the Anti-DDoS Proxy (Outside Chinese Mainland) instance of the CMA mitigation plan based on the protection requirements of your service. For more information, see What to do next.
What to do next
After a cloud service interaction rule is created, you can perform the following operations on the rule.
Operation | Description |
Switch to Anti-DDoS | If traffic scrubbing by your Anti-DDoS Pro or Anti-DDoS Premium instance is not automatically triggered, the  icon is displayed in the Cloud Service column. In this case, you can manually switch service traffic to the instance for scrubbing. You can manually switch service traffic before blackhole filtering is triggered. This reduces adverse impacts on your services. icon is displayed in the Cloud Service column. In this case, you can manually switch service traffic to the instance for scrubbing. You can manually switch service traffic before blackhole filtering is triggered. This reduces adverse impacts on your services.  Service traffic can be switched to your Anti-DDoS Pro or Anti-DDoS Premium instance only if blackhole filtering is not triggered for the IP address of the instance. Important After you manually switch service traffic to your Anti-DDoS Pro or Anti-DDoS Premium instance, the service traffic cannot be automatically switched back to the associated cloud resources. To switch the service traffic back to the associated cloud resources, you must click Switch back to manually switch the service traffic. |
Switchback | If service traffic is scrubbed by your Anti-DDoS Pro or Anti-DDoS Premium instance, the  icon is displayed in the Anti-DDoS Instance IP column. In this case, you can manually switch the service traffic back to the associated cloud resources. icon is displayed in the Anti-DDoS Instance IP column. In this case, you can manually switch the service traffic back to the associated cloud resources. 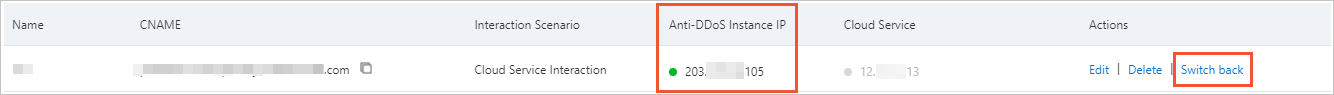 Important
If blackhole filtering is triggered for the IP addresses of all associated cloud resources, the switchback fails. If blackhole filtering is deactivated for some cloud resources, service traffic is first switched back to these cloud resources. After blackhole filtering is deactivated for the remaining cloud resources, service traffic is also switched back to these cloud resources. |
Edit | You can modify the cloud service interaction rule. However, you cannot change the values of Interaction Scenario and Name for the rule. |
Delete | You can delete the cloud service interaction rule. Warning Before you delete a rule, make sure that the domain name of your website is not mapped to the CNAME provided by Sec-Traffic Manager. Otherwise, access to the website may fail after you delete the rule. |