Production deployments accumulate credentials quickly. AccessKey pairs end up embedded in deployment scripts. Database passwords get stored in environment variable files. API tokens are committed to version control during early development and never revisited. Each of these habits creates a real attack surface, a single misconfigured storage bucket or an overly permissive policy is enough to expose credentials that may have gone unchanged for years.
In IoT and data pipeline architectures where IoT Platform, Flink, MaxCompute, and DataV each require authenticated access to the next service in the chain, managing credentials as static values in connector configuration files is not just risky; it is operationally unsustainable. The connector configuration between Flink and MaxCompute requires an AccessKey. The DataV dashboard requires credentials to query MaxCompute. The IoT Platform Rule Engine requires authorisation to forward messages to Flink source tables. As the device fleet and pipeline scale, so does the credential sprawl.
Alibaba Cloud KMS resolves this by providing a centralised managed service for cryptographic key management, secret storage, and access control. Rather than distributing credentials across service configurations, applications retrieve secrets at runtime through authenticated API calls to KMS, with every retrieval logged in ActionTrail. Key material never leaves the KMS boundary in plaintext. Rotation is automated. Access is scoped through RAM policy bindings. This article documents how KMS works, how it integrates with a production IoT data pipeline, and the operational considerations that determine whether key management remains sustainable at scale.
Manual key and secret management does not scale. Configuration files get shared, spreadsheets go stale, and rotation scripts get skipped during incidents. KMS centralises cryptographic key management, secret storage, and access control as a managed service with hardware security module support, covering the full lifecycle from key creation through rotation, access scoping, and deletion.
KMS organises cryptographic material around two key types. Customer Master Keys (CMKs) sit at the top of the hierarchy; they are never exported, and their key material never leaves the KMS service boundary. CMKs are used to protect Data Encryption Keys (DEKs), not to encrypt application data directly. This design limits the volume of data encrypted under any single CMK and isolates key material from the data it protects.
CMKs are created as either symmetric or asymmetric keys. Symmetric CMKs use AES-256 and are the right choice for at-rest encryption across MaxCompute, OSS, and RDS. Asymmetric CMKs support RSA 2048/4096 and EC P-256/P-384, and are suited for digital signature operations and public-key distribution scenarios, for example, verifying firmware image authenticity on IoT edge devices, or encrypting payloads that must be decryptable only by a specific service holding the corresponding private key.
Key versions are a first-class concept in KMS. Each rotation event produces a new key version, while the previous version remains available for the decryption of data encrypted under it. This non-destructive rotation model ensures that data encrypted before a rotation cycle stays accessible, with no re-encryption of existing MaxCompute tables required. The primary version handles all new encryption operations; older versions are retained for decryption only.
For regulated workloads that require hardware-backed key material, KMS supports HSM-protected keys generated and stored within FIPS 140-2 Level 3 validated hardware. Cryptographic operations are performed within the HSM boundary, satisfying compliance requirements in financial services, healthcare, and government contexts where software-based key storage is not acceptable. The KMS API is identical for HSM-backed and software-backed keys; the distinction is made at key creation time through the Protection-Level parameter.
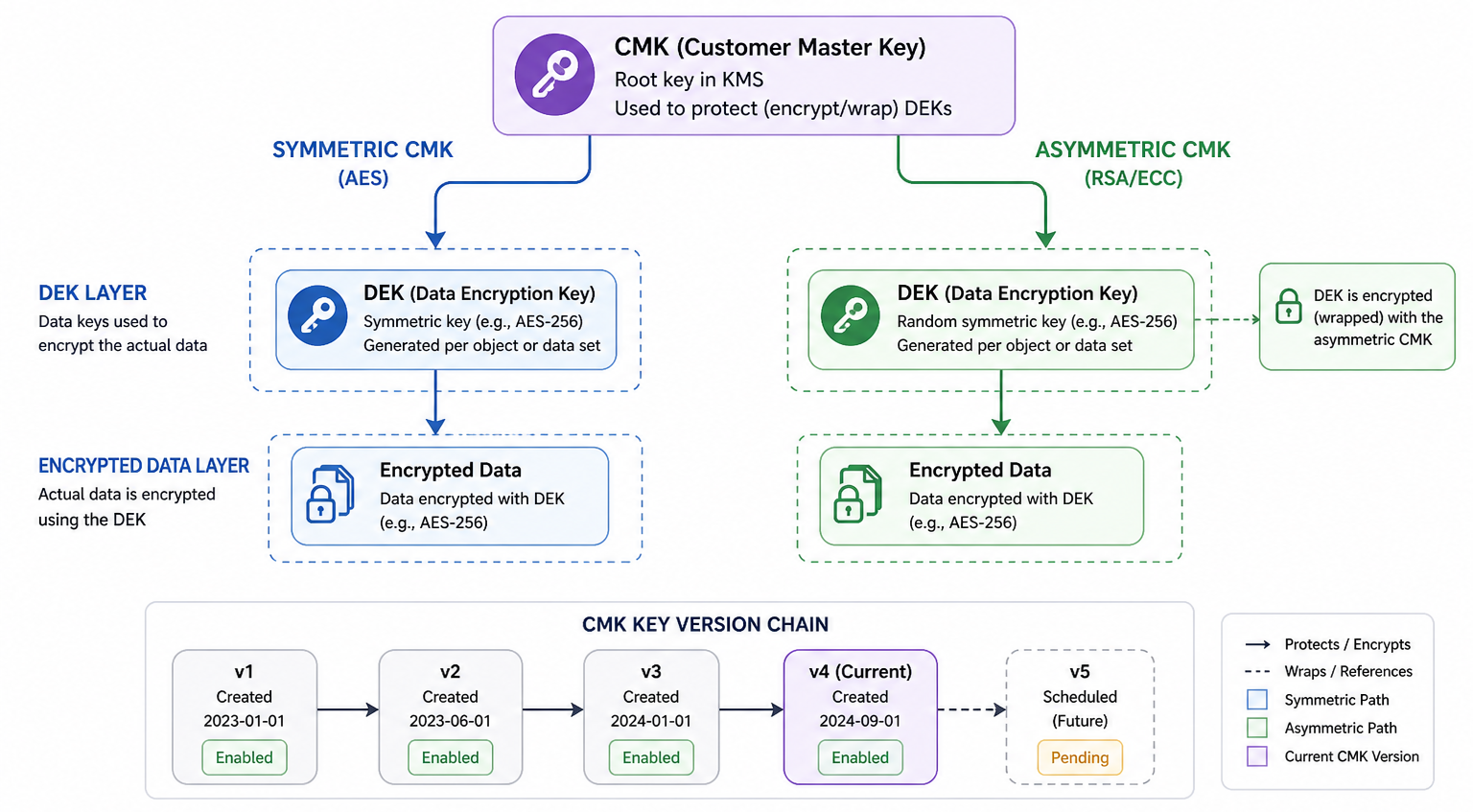
Figure 1: KMS Key Hierarchy — CMK, DEK, and Key Version Chain
Envelope encryption is the standard pattern for applying KMS to data at rest. Rather than sending raw data to the KMS API, which would impose per-operation latency and cost on every write, the application generates a DEK locally, uses it to encrypt the data, and then calls KMS to encrypt the DEK itself using a CMK. The encrypted DEK is stored alongside the encrypted data. The CMK never touches the raw data.
The KMS API exposes this through two calls. Generate DataKey returns both a plaintext DEK and a ciphertext blob of the DEK encrypted under the CMK. The application encrypts data using the plaintext DEK, discards the DEK from memory, and persists only the ciphertext blob. On read, a Decrypt call returns the plaintext DEK; the application decrypts the data, then discards the plaintext DEK again. At no point is the plaintext DEK written to disk.
For MaxCompute, OSS, and RDS, this pattern is implemented through native integration. A CMK ARN is specified at the table, bucket, or instance level, and the service handles DEK generation and envelope encryption transparently for all data written to it. The CMK is managed in KMS and controls access through key policies and RAM role bindings. The service handles the rest.
There is also a significant compliance implication. Revoking access to a CMK renders the data it protects inaccessible without deleting the data itself. Scheduling CMK deletion achieves cryptographic erasure: the data remains in storage but becomes permanently unreadable once the key material is destroyed. This is faster and more reliable than attempting to locate and delete every copy of a dataset across distributed storage.
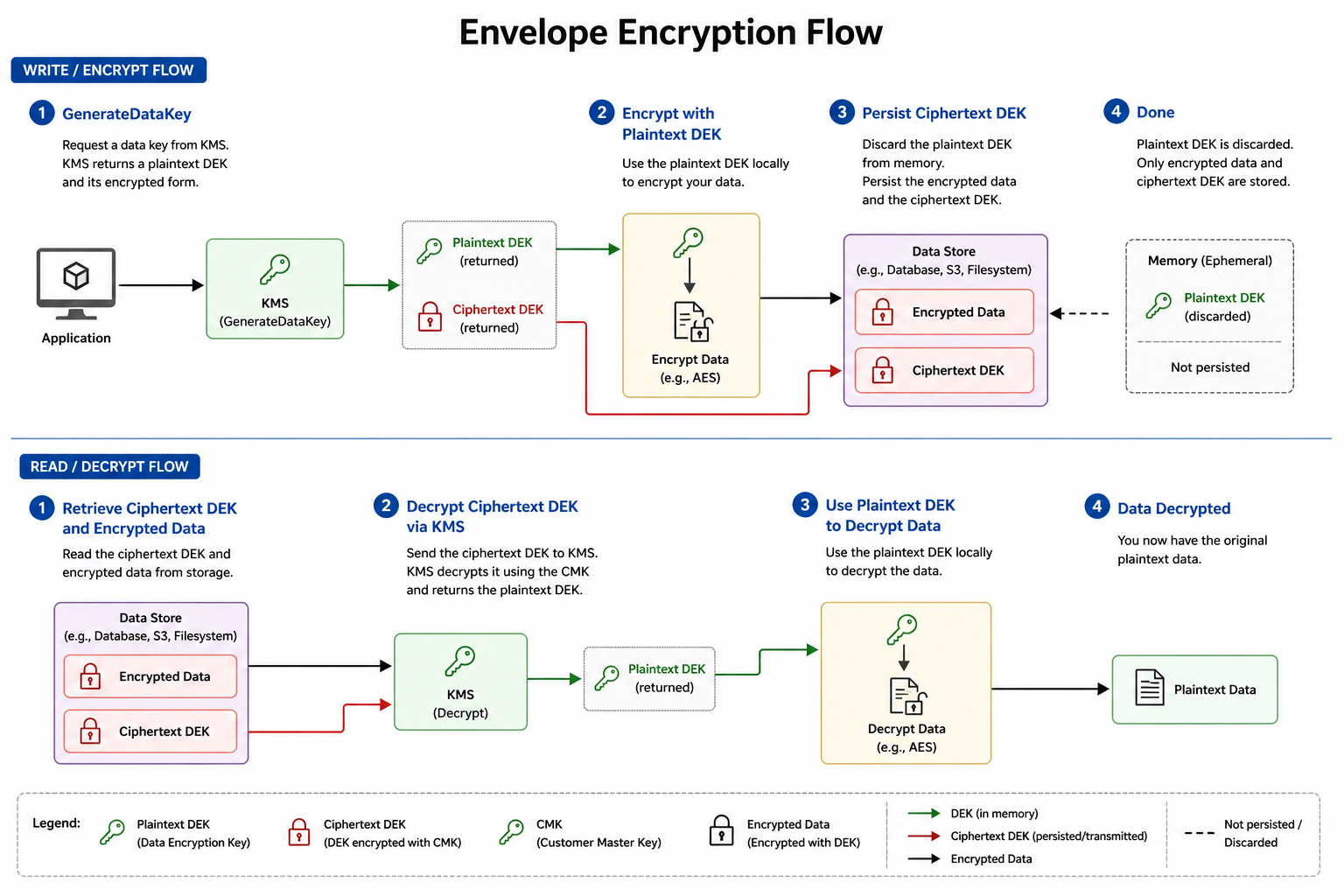
Figure 2: KMS Envelope Encryption — Encrypt and Decrypt Flow
KMS Secrets Manager extends the service beyond key management to cover the full lifecycle of credentials, AccessKey pairs, database passwords, API tokens, and any structured secret workloads require at runtime. Secrets are stored as KMS-encrypted values and are accessible only through authenticated API calls. No plaintext credentials in config files, no secrets in version control.
Automatic rotation is configured per secret. For database credentials, KMS rotation functions update the credentials in both the secret store and the target database atomically. The running application always retrieves a valid credential, with no authentication failure window during rotation. For AccessKey pairs, rotation generates a new key, updates the secret value, and schedules the prior key for deletion after a configurable overlap period to allow in-flight requests to complete cleanly.
At runtime, instead of reading a hardcoded AccessKey from a Flink connector configuration file, the application calls GetSecretValue at initialisation, retrieves the current credential, and uses it for the session. On the next rotation cycle, the updated credential is available immediately from the next call, no job redeployment, no manual intervention. This eliminates the class of credential exposure incidents that originate from configuration files being logged, committed, or accessed by unauthorised processes.
Integration with ECS, Function Compute, and ACK container workloads follows the RAM role attachment model. The compute resource is assigned a RAM role that grants GetSecretValue on the specific secrets it requires. It then retrieves a temporary STS credential from the instance metadata endpoint and uses it to call KMS; no long-lived credential is ever stored on the compute resource itself.
Access to KMS keys is governed by two complementary mechanisms: key policies attached directly to a CMK, and RAM policies attached to identities. Key policies define which Alibaba Cloud accounts and principals can use or administer a specific key. RAM policies define what KMS actions an identity can perform. Both must permit an action for it to proceed. A RAM policy granting kms: Decrypt alone is not sufficient if the CMK’s key policy does not include the requesting principal.
In a production IoT pipeline, least-privilege scoping looks like this: the Flink job’s RAM role receives Decrypt and GenerateDataKey permissions on the specific CMK used for MaxCompute table encryption, and nothing else. The DataV service account receives GetSecretValue only for the secret containing MaxCompute query credentials. The IoT Platform Rule Engine role has no KMS permissions, since it does not perform encryption operations directly. Each service’s access scope is bound to the minimum set of KMS operations required for its function.
With cross-account key sharing, the security account acts as the owner of the CMKs which are then used by the service account in another workload account. The key policy of the CMK allows the root user of the target account to assume the key, and access is delegated to certain roles within the target account via RAM policies. This solution works well for a multi-account landing zone environment where security controls are maintained in one account while the workload accounts operate without owning any keys.
KMS provides two distinct mechanisms for removing key access. Disabling a key suspends all cryptographic operations immediately and reversibly; it can be re-enabled at any time without data loss. Scheduling deletion imposes a mandatory 7-to-30-day waiting period before key material is permanently destroyed, providing a window to detect and abort accidental deletions. Once that period expires, the key material is gone, and all data encrypted under it becomes permanently inaccessible. Both operations are logged in ActionTrail with the full identity of the initiating principal.
Three operational factors determine whether KMS remains manageable under production load.
Key rotation: A 90-day automated rotation cycle is the baseline for CMKs used in service connector configuration. KMS generates a new key version on schedule without application downtime, since the prior version remains available for decryption. For Secrets Manager credentials, automated rotation should be enabled for all AccessKey pairs and database passwords. The rotation function updates both the KMS secret value and the target service credential atomically. Manual rotation is appropriate for CMKs protecting archived datasets where a rotation event has no operational impact on running workloads.
Audit via ActionTrail: ActionTrail logs every KMS API call, Encrypt, Decrypt, GenerateDataKey, GetSecretValue, and administrative operations, including CreateKey and ScheduleKeyDeletion. Each entry records the calling principal, source IP, timestamp, key ARN, and operation result. Monitoring these logs for any abnormal spike in decrypts, access from unknown IP addresses, and GetSecretValue calls from compute resources which have never made use of the secret before forms part of routine operational activities for pipelines handling sensitive information.
Region-bound keys and data sovereignty: KMS keys are region-scoped. A CMK created in China (Shanghai) cannot be used by a service operating in Singapore. For cross-region pipeline architectures, CMKs must be provisioned in each region where encryption or decryption occurs, and key policies replicated accordingly. Where data sovereignty requirements mandate that data remain within a specific jurisdiction, region-bound keys provide an enforceable technical control: data encrypted in a region cannot be decrypted outside it.
CloudMonitor and API rate management: CloudMonitor surfaces KMS API call rate, error rate, and throttle events per key. For pipelines where GenerateDataKey is in the critical write path, called per Flink checkpoint or per MaxCompute table write monitoring, KMS API latency and throttle rate are essential. KMS enforces per-account API rate limits; high-frequency write pipelines should batch DEK generation where possible, caching the plaintext DEK in memory for the duration of a processing window rather than generating a new DEK per record.
Alibaba Cloud KMS is the security foundation layer that sits beneath every service covered in this blog series. IoT Platform device credential storage, Flink connector authentication, MaxCompute at-rest encryption, and DataV data source credentials are all manageable through a single KMS control plane, replacing static credentials distributed across configuration files with runtime-retrieved, automatically rotated, and fully audited secrets. The four-layer IoT pipeline architecture is operationally complete only when the credential lifecycle across all four services is managed with the same rigour applied to the data pipeline itself.
Two extension patterns address advanced requirements. Bring Your Own Key (BYOK) allows organisations with existing HSM infrastructure to import key material into KMS CMKs, retaining control of the underlying cryptographic material while using KMS for lifecycle management and access control. For regulated industries requiring formal HSM certification, Alibaba Cloud Managed HSM provides a dedicated partition with exclusive key ownership provisioned directly within your VPC. Both patterns integrate with the same KMS API and RAM policy model described in this article, with no changes required to application-layer secret retrieval logic.
Disclaimer: The views expressed herein are for reference only and don't necessarily represent the official views of Alibaba Cloud.
End-to-End MLOps Pipeline with Alibaba Cloud: PAI-DSW, PAI-DLC, OSS and PAI-EAS

109 posts | 2 followers
FollowAlibaba Cloud Community - March 16, 2022
Farah Abdou - January 29, 2026
Léon Rodenburg - December 24, 2019
Rupal_Click2Cloud - December 14, 2023
Alibaba Cloud Community - November 12, 2024
Alibaba Cloud Community - November 7, 2024

109 posts | 2 followers
Follow Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Cloud Hardware Security Module (HSM)
Cloud Hardware Security Module (HSM)
Industry-standard hardware security modules (HSMs) deployed on Alibaba Cloud.
Learn More Security Solution
Security Solution
Alibaba Cloud is committed to safeguarding the cloud security for every business.
Learn More Security Overview
Security Overview
Simple, secure, and intelligent services.
Learn MoreMore Posts by PM - C2C_Yuan