在配置DTS執行個體時,若源庫或目標庫為Microsoft Azure平台的資料庫,您需要進行相應的配置,以允許DTS伺服器的訪問。通常可以選擇使用公網IP或VPC,將Azure平台的資料庫接入至阿里雲。本文為您介紹相關操作的步驟。
通過公網IP接入
在Azure平台中將資料庫開通公網存取權限,並將根據您的任務類型(資料同步、資料移轉或資料校正等)將DTS伺服器所在地區的IP地址添加至相應資料庫的安全設定(安全性群組規則、防火牆、白名單等)中。
若源庫為Azure SQL Managed Instance,請選擇此方案接入到阿里雲。
通過VPC接入
情境樣本

以上圖情境為例,某企業:
在Azure平台的Germany West Central地區擁有一個VNet,VNet中建立了VM執行個體。
在阿里雲德國(法蘭克福)地區建立了一個VPC,並且VPC下已建立了ECS執行個體。
可使用阿里雲IPsec-VPN(綁定VPN網關),在Azure虛擬網路和阿里雲VPC之間建立網路連接,實現相互連信。
前提條件
在開始操作前,請確保您已經擁有以下環境並且已獲得對應的資源資訊:
在Azure平台Germany West Central地區擁有一個虛擬網路,虛擬網路下部署了Azure VM執行個體。具體操作,請諮詢Azure平台。
在阿里雲平台德國(法蘭克福)地區擁有一個VPC,VPC下已建立ECS執行個體。
您已知Azure虛擬網路和阿里雲VPC間要互連的網段資訊:
重要您可以自行規劃網段,請確保Azure虛擬網路和阿里雲VPC間要互連的網段沒有重疊。
資源
網段
資源IP地址
阿里雲VPC
10.0.0.0/16
ECS執行個體地址:
10.0.0.1
Azure虛擬網路
192.168.0.0/16
VM執行個體地址:
192.168.0.1
步驟一:在阿里雲建立VPN網關執行個體
您需要先在阿里雲建立一個VPN網關執行個體,VPN網關執行個體建立完成後,系統會為VPN網關執行個體分配2個IP地址,這2個IP地址用於與Azure平台虛擬網路建立IPsec-VPN串連。
前往VPN網關管理主控台,配置以下參數:
以下僅列舉本文強相關的配置,其餘配置項保持預設值或為空白。各選項的詳細解釋,請參見建立和管理VPN網關執行個體。
配置項
說明
本文樣本值
執行個體名稱
輸入VPN網關執行個體的名稱。
輸入VPN網關。
地區
選擇VPN網關執行個體所屬的地區。
選擇德國(法蘭克福)。
網關類型
選擇VPN網關執行個體的網關類型。
選擇普通型。
網路類型
選擇VPN網關執行個體的網路類型。
選擇公網。
隧道
系統直接展示當前地區IPsec-VPN串連支援的隧道模式。
雙隧道
單隧道
關於單隧道和雙隧道的說明,請參見綁定VPN網關。
本文保持預設值雙隧道。
專用網路
選擇VPN網關執行個體關聯的VPC執行個體。
選擇阿里雲德國(法蘭克福)地區的VPC執行個體。
虛擬交換器
從VPC執行個體中選擇一個交換器執行個體。
IPsec-VPN串連的隧道模式為單隧道時,您僅需要指定一個交換器執行個體。
IPsec-VPN串連的隧道模式為雙隧道時,您需要指定兩個交換器執行個體。
IPsec-VPN功能開啟後,系統會在兩個交換器執行個體下各建立一個彈性網卡ENI(Elastic Network Interfaces),作為使用IPsec-VPN串連與VPC流量互連的介面。每個ENI會佔用交換器下的一個IP地址。
說明系統預設幫您選擇第一個交換器執行個體,您可以手動修改或者直接使用預設的交換器執行個體。
建立VPN網關執行個體後,不支援修改VPN網關執行個體關聯的交換器執行個體,您可以在VPN網關執行個體的詳情頁面查看VPN網關執行個體關聯的交換器、交換器所屬可用性區域以及交換器下ENI的資訊。
選擇VPC執行個體下的一個交換器執行個體。
虛擬交換器2
從VPC執行個體中選擇第二個交換器執行個體。
您需要從VPN網關執行個體關聯的VPC執行個體下指定兩個分布在不同可用性區域的交換器執行個體,以實現IPsec-VPN串連可用性區域層級的容災。
對於僅支援一個可用性區域的地區 ,不支援可用性區域層級的容災,建議您在該可用性區域下指定兩個不同的交換器執行個體以實現IPsec-VPN串連的高可用,支援選擇和第一個相同的交換器執行個體。
說明如果VPC執行個體下沒有第二個交換器執行個體,您可以建立交換器執行個體。具體操作,請參見建立和管理交換器。
選擇VPC執行個體下的第二個交換器執行個體。
IPsec-VPN
選擇開啟或關閉IPsec-VPN功能。預設值:開啟。
選擇開啟IPsec-VPN功能。
SSL-VPN
選擇開啟或關閉SSL-VPN功能。預設值:關閉。
選擇關閉SSL-VPN功能。
返回VPN網關頁面,查看建立的VPN網關執行個體
剛建立好的VPN網關執行個體的狀態是準備中,約1~5分鐘左右會變成正常狀態。正常狀態表明VPN網關已經完成了初始化,可以正常使用。
系統為VPN網關執行個體分配的2個IP地址如下表所示:
VPN網關執行個體的名稱
VPN網關執行個體ID
IP地址
VPN網關
vpn-gw8dickm386d2qi2g****
IPsec地址1(預設為主隧道地址):8.XX.XX.130
IPsec地址2(預設為備隧道地址):8.XX.XX.75
步驟二:在Azure平台部署VPN
為在Azure虛擬網路和阿里雲VPC之間建立IPsec-VPN串連,您需要根據以下資訊在Azure平台部署VPN,配置需要的具體操作請諮詢Azure平台。
在虛擬網路中建立網關子網。建立虛擬網路網關時將會使用到該子網。

建立虛擬網路網關。
虛擬網路網關關聯至需要和阿里雲互連的虛擬網路上。本文中虛擬網路網關啟用主動-主動模式,並建立2個公網IP地址,其餘配置採用預設值。

虛擬網路網關建立完成後,您可以在公用IP地址頁面查看系統為虛擬網路網關分配的公用IP地址。本文中系統分配的公用IP地址為4.XX.XX.224和4.XX.XX.166。

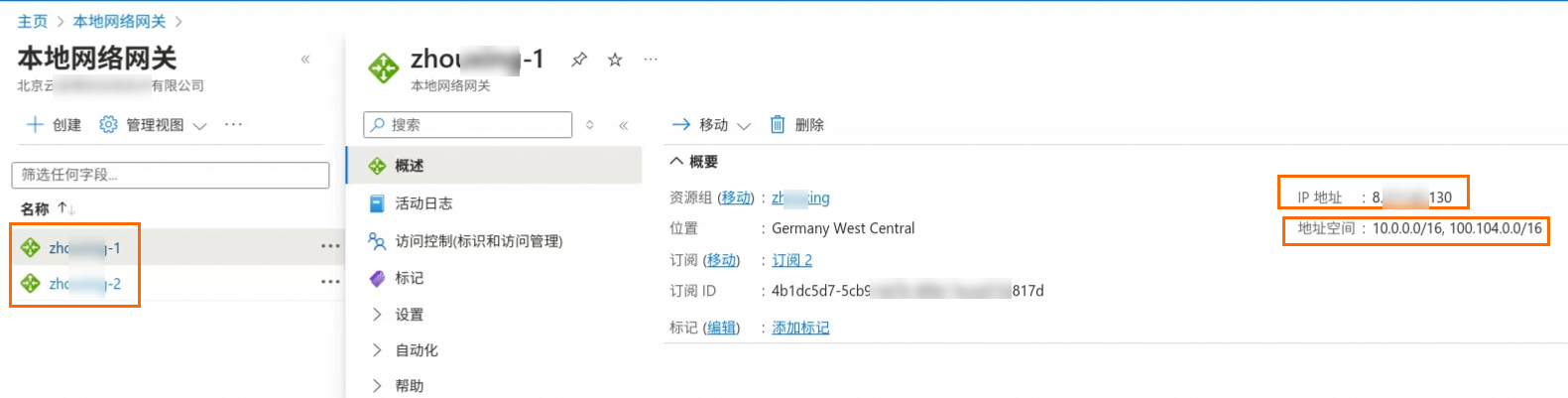
建立本網網關。
您需要在Azure側建立2個本網網關,每個本網網關配置阿里雲VPN網關執行個體的一個IP地址,並將阿里雲側的VPC網段配置到每個本網網關上。
重要針對使用DTS從Azure向阿里雲同步資料的情境,您還需要添加100.104.0.0/16網段,DTS將使用該網段下的地址遷移資料。
關於DTS位址區段的更多資訊,請參見添加DTS伺服器IP地址白名單。
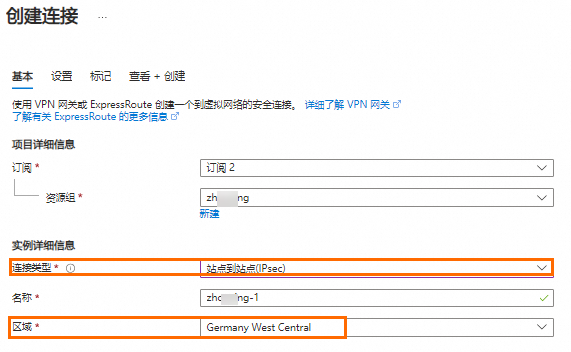
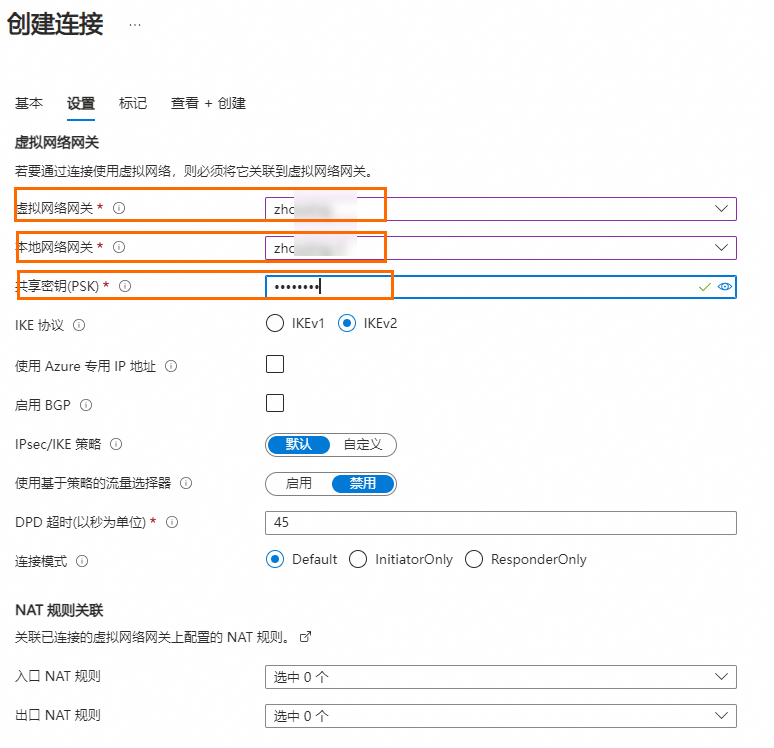
建立網站到網站VPN串連。
重要阿里雲和Azure平台下的IPsec-VPN串連均支援雙隧道模式,但由於Azure平台的兩條隧道預設關聯至同一個本網網關,而阿里雲側兩條隧道擁有不同的IP地址,導致Azure平台和阿里雲側的兩條隧道無法做到一一對應建立串連。為確保阿里雲側IPsec-VPN串連下兩條隧道同時啟用,您需要在Azure平台建立兩個網站到網站的VPN串連,每個網站到網站VPN串連關聯不同的本網網關。
下圖展示其中一個網站到網站VPN串連的配置,建立VPN串連時選擇網站到網站(IPsec)類型,並關聯需要和阿里雲建立VPN串連的虛擬網路網關,然後選擇一個本網網關並設定共用密鑰,其餘配置項使用預設值。另一個網站到網站VPN串連關聯與當前VPN串連不同的本網網關,其餘配置與當前VPN串連相同。
步驟三:在阿里雲部署VPN網關
在Azure平台完成VPN配置後,請根據以下資訊在阿里雲側部署VPN網關,以便Azure虛擬網路和阿里雲VPC之間建立IPsec-VPN串連。
建立使用者網關。
建立IPsec串連。
在左側導覽列,選擇。
在IPsec串連頁面,單擊綁定VPN網關。
在建立IPsec串連(VPN)頁面,根據以下資訊配置IPsec串連,然後單擊確定。
配置項
說明
本文樣本值
IPsec串連名稱
輸入IPsec串連的名稱。
輸入IPsec串連。
地區
選擇IPsec串連要綁定的VPN網關執行個體的地區。
IPsec串連建立完成後所屬地區與VPN網關執行個體地區相同。
選擇德國(法蘭克福)。
資源群組篩選
選擇VPN網關執行個體所屬的資源群組。
選擇預設資源群組。
綁定VPN網關
選擇IPsec串連關聯的VPN網關執行個體。
選擇已建立的VPN網關。
路由模式
選擇路由模式。
目的路由模式:基於目的IP地址路由和轉寄流量。
感興趣流模式:基於源IP地址和目的IP地址精確的路由和轉寄流量。
選擇感興趣流模式。
本端網段
輸入VPN網關執行個體關聯的VPC執行個體下的網段。
輸入VPC網段:10.0.0.0/16
重要針對使用DTS從Azure向阿里雲同步資料的情境,您還需要添加100.104.0.0/16網段,DTS將使用該網段下的地址遷移資料。
對端網段
輸入VPN網關執行個體關聯的VPC執行個體要訪問的對端的網段。
輸入192.168.0.0/16。
立即生效
選擇IPsec串連的配置是否立即生效。取值:
是:配置完成後立即進行協商。
否:當有流量進入時進行協商。
選擇是。
啟用BGP
如果IPsec串連需要使用BGP路由協議,需要開啟BGP功能的開關,系統預設關閉BGP功能。
本文保持預設值,即不開啟BGP功能。
Tunnel 1
為隧道1(主隧道)添加VPN相關配置。
系統預設隧道1為主隧道,隧道2為備隧道,且不支援修改。
使用者網關
為主隧道添加待關聯的使用者網關執行個體。
選擇使用者網關1。
預先共用金鑰
輸入主隧道的認證密鑰,用於身份認證。
密鑰長度為1~100個字元,支援數字、大小寫英文字母及右側字元
~`!@#$%^&*()_-+={}[]\|;:',.<>/?。若您未指定預先共用金鑰,系統會隨機產生一個16位的字串作為預先共用金鑰。
重要隧道及其對端網關裝置配置的預先共用金鑰需一致,否則系統無法正常建立IPsec-VPN串連。
當前隧道的認證密鑰需和串連的Azure平台VPN串連的密鑰一致。
加密配置
添加IKE配置、IPsec配置、DPD、NAT穿越等配置。
本文保持預設值。關於預設值的說明,請參見IPsec串連(VPN網關)。
Tunnel 2
為隧道2(備隧道)添加VPN相關配置。
使用者網關
為備隧道添加待關聯的使用者網關執行個體。
選擇使用者網關2。
預先共用金鑰
輸入備隧道的認證密鑰,用於身份認證。
當前隧道的認證密鑰需和Azure平台VPN串連的密鑰一致。
加密配置
添加IKE配置、IPsec配置、DPD、NAT穿越等配置。
本文保持預設值。關於預設值的說明,請參見IPsec串連(VPN網關)。
在建立成功對話方塊中,單擊取消。
配置VPN網關路由。
建立IPsec串連後需要為VPN網關執行個體配置路由。建立IPsec串連時,如果路由模式您選擇了感興趣流模式,在IPsec串連建立完成後,系統會自動在VPN網關執行個體下建立策略路由,路由是未發布狀態。您需要執行本操作,將VPN網關執行個體下的策略路由發布至VPC中。
在左側導覽列,選擇。
在頂部功能表列,選擇VPN網關執行個體的地區。
在VPN網關頁面,單擊目標VPN網關執行個體ID。
在VPN網關執行個體詳情頁面單擊策略路由表頁簽,找到目標路由條目,在操作列單擊發布。
在發布路由對話方塊,單擊確定。
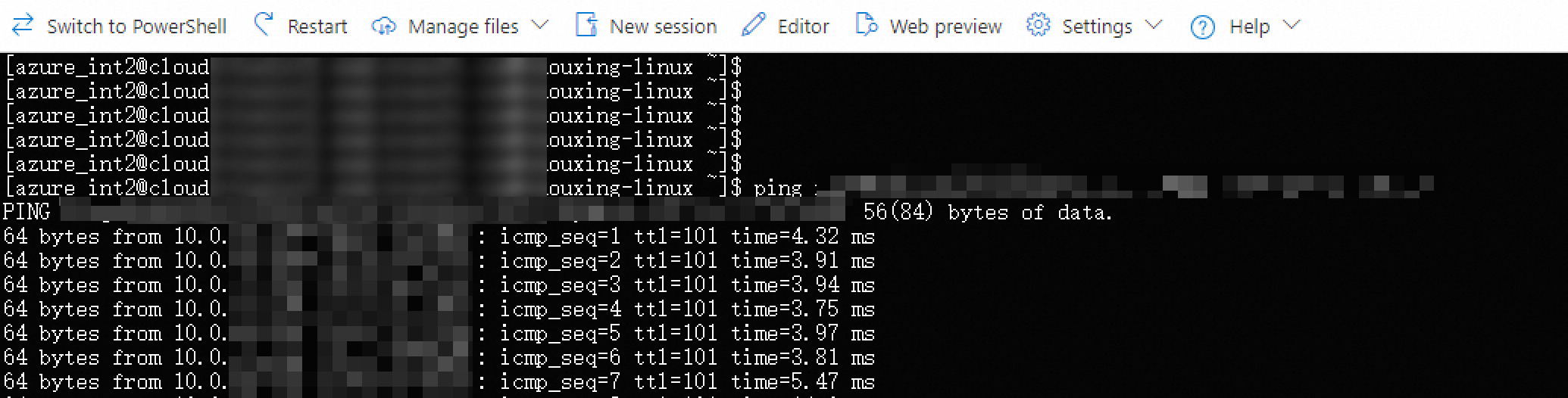
步驟四:測試網路連通性
完成上述配置後,阿里雲VPC和Azure虛擬網路下的資源已經可以互相通訊了,您可以通過以下步驟驗證阿里雲VPC和Azure虛擬網路之間的網路連通性。
在Azure虛擬網路中建立並登入Azure VM執行個體。具體操作,請諮詢Azure平台。
在VM執行個體中執行
ping命令,訪問阿里雲ECS執行個體的內網地址。ping 10.0.0.1如果VM執行個體可以收到如下所示的回複報文,則證明阿里雲VPC和Azure虛擬網路下的資源可以正常通訊。
後續步驟
根據您的任務類型(資料同步、資料移轉或資料校正等)將DTS伺服器所在地區的IP地址添加至相應資料庫的安全設定(安全性群組規則、防火牆、白名單等)中。