Very secure FTP daemon (vsftpd) is a piece of widely used, open source FTP server software. vsftpd is known for its high performance, high security, and high stability and supports a variety of FTP-related protocols, such as FTP, SFTP over SSH, and FTP over SSL/TLS. This topic describes how to install and configure vsftpd on a Linux Elastic Compute Service (ECS) instance.
Quick deployment
Click here to go to Terraform Explorer, where you can view and run Terraform code to automatically build an FTP site on an ECS instance.
Prerequisites
An ECS instance is created and has the following settings. If no ECS instance is created, create an ECS instance. For more information, see Create an instance on the Custom Launch tab.
Operating system: Alibaba Cloud Linux 3, Alibaba Cloud Linux 2, CentOS 7.x 64-bit, Ubuntu, or Debian.
IP address: The instance is assigned a static public IP address (also known as auto-assigned or system-assigned public IP address) or is associated with an elastic IP address (EIP). For more information, see EIPs.
Benefits
vsftpd is open source FTP server software designed for Unix and Linux. vsftpd provides the following benefits:
High security: vsftpd undergoes strict security audits and uses a variety of security mechanisms to effectively prevent common attacks and vulnerabilities.
Superior performance: vsftpd provides high-performance file transfer capabilities and supports a large number of concurrent connections.
Simple configuration: vsftpd provides flexible and easy-to-understand configuration options to suit a variety of user needs.
IPv6: vsftpd provides support for next-generation network protocols.
Build the VSFTP service
Alibaba Cloud Linux 2, Alibaba Cloud Linux 3, and CentOS 7.x
Step 1: Install vsftpd
Run the following commands to update the Yellowdog Updater Modified (YUM) repository and install vsftpd:
sudo yum update sudo yum install -y vsftpdRun the following command to configure vsftpd to automatically start on system startup:
systemctl enable vsftpdRun the following command to start FTP:
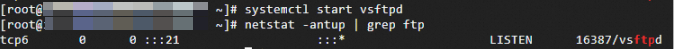
systemctl start vsftpdRun the following command to check whether FTP starts:
netstat -antup | grep ftpIf the following command output is returned, FTP is started as expected.
By default, vsftpd is enabled in anonymous mode, which allows you to log on to the FTP server without entering the username or password. Users who log on to the FTP server in anonymous mode cannot modify or upload files.
Step 2: Configure vsftpd
Run the following command to create a Linux user for the FTP service. In this example, the ftpuser user is created.
useradd ftpuserRun the following command to specify a password for the ftpuser user:
passwd ftpuserEnter the password and press the Enter key. The password is not displayed by default.
Run the following command to create a file directory used by the FTP service. In this example, the /var/ftp/test directory is used.
mkdir /var/ftp/testRun the following command to modify directory permissions:
chown -R ftpuser:ftpuser /var/ftp/testRun the following command to open the vsftpd.conf file:
vim /etc/vsftpd/vsftpd.confPress the I key to enter Insert mode, select an FTP mode based on your business requirements, and then modify the vsftpd.conf file.
NoteAn FTP server allows an FTP client to connect in active or passive mode to transfer files. We recommend that you specify the passive mode to build the FTP service. This prevents the issues caused by firewall settings on FTP client machines and IP address translation. In the following example, the passive mode is used.
Run the following command to back up the
vsftpconfiguration file:sudo cp /etc/vsftpd/vsftpd.conf /etc/vsftpd/vsftpd.conf.bakModify the following parameters to grant the access permissions to anonymous users and local users, specify the path in which the exception user list file is stored, and then listen on IPv4 sockets.
anonymous_enable=NO local_enable=YES write_enable=YES chroot_local_user=YES chroot_list_enable=YES chroot_list_file=/etc/vsftpd/chroot_list listen=YESAdd a number sign (#) to the beginning of the line to comment out the listen_ipv6=YES parameter to disable the instance from listening on IPv6 sockets.
#listen_ipv6=YESAdd the following parameters to enable the passive mode, and specify the directory that a local user accesses after the local user logs on to the FTP server and a port range that the instance can use to establish FTP connections.
local_root=/var/ftp/test allow_writeable_chroot=YES #If pasv_enable is set to YES, the passive mode is enabled. If pasv_enable is set to NO, the active mode is used. pasv_enable=YES #Replace the value with the public IP address of your Linux ECS instance. pasv_address=xxx.xx.xxx.xx pasv_min_port=40000 pasv_max_port=40100NoteFor information about the reasons for opening specific ports and suggestions on how to open ports in passive mode, see Build an FTP site on a Windows instance.
Press the Esc key, enter :wq, and then press the Enter key to save and close the file.
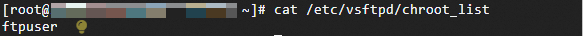
Run the following commands to create and open the chroot_list file:
vim /etc/vsftpd/chroot_listPress the I key to enter Insert mode and enter a username. One username occupies one line. After you configure all settings, press the Esc key, enter :wq, and then press the Enter key to save and close the file. The configured user is locked to the home directory. If you do not want to specify an exception user, skip this step and enter :q to close the file.
Run the following command to restart FTP:
systemctl restart vsftpd
Step 3: Configure security group rules
After you build the FTP service, you must add inbound security group rules to the security groups to which the Linux ECS instance belongs based on the FTP mode. For more information, see Add a security group rule.
Most client machines reside on local area networks (LANs), and their IP addresses are translated. If you specify the FTP active mode, make sure that the client machines can use the actual IP addresses to initiate connections to the FTP server. Otherwise, the clients may fail to connect to the FTP server. Make sure that the configurations are correct to prevent connection issues and improve the stability and availability of the FTP service.
Active mode: Open port 21.
Passive mode: Open port 21 and all ports from the start port (pasv_min_port) to the end port (pasv_max_port) specified in the /etc/vsftpd/vsftpd.conf file. In this example, ports 40000 to 40100 are opened.
Step 4: Verify the FTP service
You can use FTP client software, a browser, or a file resource manager to verify the FTP service. In this example, File Explorer is used as the FTP client.
On the computer that serves as an FTP client, access the following address in the address bar, as shown in the following figure.
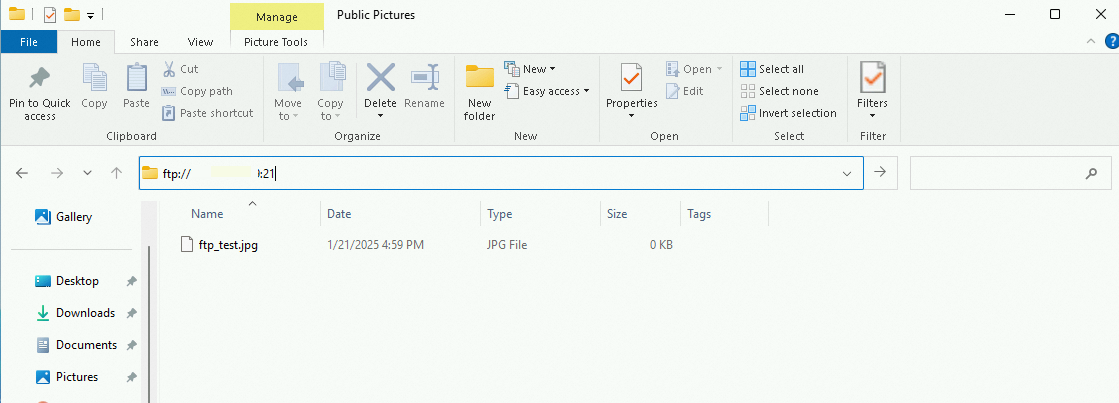
In the dialog box that appears, enter the username and the password that you specified in Step 2.2.
After you log on to the FTP server, you can upload and download files.
Ubuntu and Debian
Step 1: Install VSFTP
Run the following command to install
vsftpd:# Update the Advanced Packaging Tool (APT) repository. sudo apt-get update sudo apt-get install vsftpdRun the following command to back up the original configuration file:
sudo cp /etc/vsftpd.conf /etc/vsftpd.conf.bak
Step 2: Configure VSFTP
Run the following command to open the configuration file of
vsftpd:sudo vim /etc/vsftpd.confModify configurations in the configuration file.
Modify the following configurations to configure FTP access permissions. Allow only local users to access FTP and disable any anonymous access
anonymous_enable=NO local_enable=YESModify the following configuration to enable file upload:
write_enable=YESRemove the number sign (#) at the beginning of the following lines to use chroot jails to restrict FTP user access and configure accessible FTP user files.
chroot_local_user=YES chroot_list_file=/etc/vsftpd.chroot_listAdd the following configurations to the configuration file to create an FTP service directory and allow users to write in the attached chroot directory. By default, users cannot write in the chroot directory that is writable.
local_root=/home/ftp allow_writeable_chroot=YES(Optional) Modify the following configurations to configure the FTP passive mode. vsftpd can use any port to establish passive FTP connections. You can specify the minimum and maximum port numbers to define a port range that vsftpd can use.
Add the following lines to the configuration file to allow passive FTP connections:
pasv_min_port=35000 pasv_max_port=40000Run the following command to restart vsftpd for the configurations to take effect:
sudo systemctl restart vsftpd
Step 3: Configure an FTP user directory
After you install FTP, the system automatically creates a user named ftp, and no password is specified. Run the following command to change the password of the default username:
sudo passwd ftpSpecify a strong password and skip all prompts.
Run the following command to add the user to the list of allowed FTP users:
echo "ftp" | sudo tee -a /etc/vsftpd.userlistCreate an FTP file directory and grant access to the user.
Run the following command to create an FTP directory:
sudo mkdir /home/ftpRun the following command to grant the user the access to the directory. In this example, full permissions on the directory, such as read and write permissions, are granted to the user. You can modify the permissions based on your business requirements.
sudo chmod 777 /home/ftp
Step 4: Configure security group rules
After you build the FTP service, you must add inbound rules to the security groups to which the Linux ECS instance belongs based on the FTP mode.
Most client machines reside on a LAN, and their IP addresses are translated. If you specify the FTP active mode, make sure that the client machines can use the actual IP addresses to initiate connections to the FTP server. Otherwise, the clients may fail to connect to the FTP server. Make sure that the configurations are correct to prevent connection issues and improve the stability and availability of the FTP service.
Active mode: Open port 21.
Passive mode: Open port 21 and all ports from the start port (pasv_min_port) to the end port (pasv_max_port) specified in the /etc/vsftpd/vsftpd.conf file. For information about the reasons for opening specific ports and suggestions on how to open ports in FTP passive mode, see Build an FTP site on a Windows instance.
Step 4: Verify the FTP service
You can use FTP client software, a browser, or a file resource manager to verify the FTP service. In this example, File Explorer is used as the FTP client.
On the computer on which the FTP client resides, access the following address in the address bar, as shown in the following figure.
In the dialog box that appears, enter the username and the password that you specified in Step 2.2.
After you log on to the FTP server, you can upload and download files.
Appendix
vsftpd configuration file and parameters
The following section describes the files in the /etc/vsftpd directory:
/etc/vsftpd/vsftpd.confis the core configuration file of vsftpd./etc/vsftpd/ftpusersis the blacklist file. Users specified in this file are not allowed to access the FTP server./etc/vsftpd/user_listis the whitelist file. Users specified in this file are allowed to access the FTP server.
The following tables describe the parameters that are used in the vsftpd.conf configuration file.
The following table describes the parameters for logon control.
Parameter
Description
anonymous_enable=YES
Accepts anonymous users.
no_anon_password=YES
Allows anonymous users to log on to the FTP server without the need to enter a password.
anon_root=(none)
Specifies the home directory of anonymous users.
local_enable=YES
Accepts local users.
local_root=(none)
Specifies the home directory of local users.
The following table describes the parameters that are used to manage the permissions of users.
Parameter
Description
write_enable=YES
Allows all users to upload files.
local_umask=022
Grants local users permissions to upload files.
file_open_mode=0666
Uses umask to grant permissions to upload files.
anon_upload_enable=NO
Allows anonymous users to upload files.
anon_mkdir_write_enable=NO
Allows anonymous users to create directories.
anon_other_write_enable=NO
Allows anonymous users to modify and delete files.
chown_username=lightwiter
Specifies the ownership of files that are uploaded by anonymous users.