Referer-based hotlink protection refers to access control based on the Referer header. You can configure a Referer whitelist or blacklist to control access, protecting your resources from unauthorized access. After you configure a Referer whitelist or blacklist, DCDN allows or rejects requests based on the Referer header.
By default, Referer-based hotlink protection is not enabled in DCDN. This means that all websites can access your resources.
Referer-based hotlink protection is a method to prevent data transmission abuse. For more information about protection methods, see Prevent data transmission abuse.
After you add a domain name to the Referer whitelist or blacklist, the wildcard domain name that matches the domain name is automatically added to the whitelist or blacklist. For example, if you add
aliyundoc.comto the Referer whitelist or blacklist, hotlink protection takes effect for all domain names that match*.aliyundoc.com.
Scenarios
A Referer whitelist or blacklist is suitable for the following scenarios:
Copyright protection: To safeguard copyrighted content on your website, you can use a Referer whitelist or blacklist to allow only authorized websites to access the content.
Hotlink protection: Referer whitelists or blacklists can prevent your resources from being used by other websites.
Enhanced website security: Only domain names that are included in the Referer whitelist are allowed to access your website resources. This prevents malicious hotlinking or theft of sensitive information.
Traffic source management: You can manage the domains that are authorized to use your resources. This ensures the security and stability of your website.
You can use the hotlink protection feature in different scenarios to protect your website assets, manage traffic, and improve website security.
How it works
The server checks the Referer field of each request and rejects a request if the Referer field in the request does not match the pre-configured whitelist. This helps save bandwidth and server resources. Referer rules in DCDN:
If the Referer header in the request is included in the Referer blacklist or is not included in the Referer whitelist, DCDN rejects the request.
If the Referer header in the request is included in the Referer whitelist, DCDN allows the request.

Procedure
Log on to the DCDN console.
In the left-side navigation pane, click Domain Names.
On the Domain Names page, find the domain name that you want to manage and click Configure.
In the left-side navigation tree of the domain name, click Access Control.
On the Hotlink Protection tab, turn on Hotlink Protection.
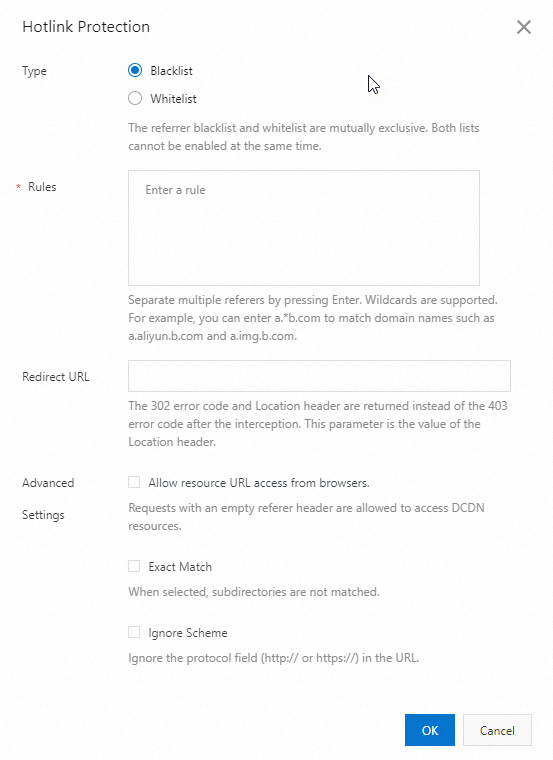
Select Blacklist or Whitelist based on your business requirements.
Parameter
Description
Type
Blacklist
Requests from domain names in the blacklist cannot access your resources.
Whitelist
Only requests from domain names in the whitelist can access your resources.
NoteThe blacklist and whitelist are mutually exclusive. You can configure only one type of list at a time.
Rules
You can add multiple domain names to the Referer whitelist or blacklist. Enter one domain name per line. Do not add a space in front of the domain names.
You can use asterisks (*) as wildcards. For example, if you add
*.developer.aliyundoc.comto the whitelist or blacklist,image.developer.aliyundoc.comandvideo.developer.aliyundoc.comcan be matched.
NoteThe content that you enter in the Rules field cannot exceed 60 KB.
Redirect URL
If a request is blocked, HTTP status code 302 and the Location header are returned. This parameter is the value of the Location header. The value must start with
http://orhttps://, such ashttp://www.example.com.Advanced Settings
Allow resource URL access from browsers.
By default, the check box is not selected. If you select the check box, requests that contain an empty Referer header are allowed to access DCDN resources, regardless of whether you configure a Referer whitelist or blacklist. An empty Referer header may suggest one of the following scenarios:
The Referer header is not included in the requests.
The Referer header is included in the requests, but the value is empty.
Exact Match
The check box is not selected by default. If you select this check box, subdomains cannot be matched. For example, if you add
example.comto the whitelist or blacklist, onlyexample.comis matched.Ignore Scheme
If you do not select Ignore Scheme, the value of the Referer header must start with http:// or https://.
If you select Ignore Scheme, the value of the Referer header does not need to start with http:// or https://.
Click OK.
Matching logic
The following table describes the matching logic of the Referer header. If the Referer header in a request does not match the whitelist or matches the blacklist, DCDN rejects the request and returns HTTP status code 403.
Configured domain name | Referer header value in a request | Matched | Description |
| http://www.example.com/img.jpg | Yes | The domain names in the Referer header match the domain names in the Referer whitelist or blacklist. |
http://www.example.com:80/img.jpg | Yes | ||
www.example.com | No | The value of the Referer header in the request does not include the HTTP or HTTPS string. | |
http://aaa.example.com | Yes | The subdomains in the Referer header are covered by the wildcard domain name in the Referer whitelist or blacklist. | |
http://aaa.bbb.example.com | Yes | ||
http://example.com | No | The domain name in the Referer header does not match the wildcard domain name in the Referer whitelist or blacklist. This is because a wildcard domain matches subdomains but does not cover the root domain. | |
http://www.example.net | No rules matched | The domain name in the Referer header is not included in the blacklist or whitelist. Therefore, the request is allowed according to the default rule. |