By default, all virtual private clouds (VPCs) attached to a Cloud Enterprise Network (CEN) instance can communicate with each other. As your network grows, this full-mesh connectivity can become difficult to manage and may not meet your security requirements. This topic describes how to configure routing policies to restrict connectivity so that only specific VPCs can communicate.
This feature is supported only by Basic Edition transit routers.
Deny-all-then-allow-specific pattern
This approach works like a firewall rule set:
Deny all -- Create low-priority routing policies (priority 100) on each transit router to reject all VPC-bound routes. This blocks communication between all attached VPCs.
Allow specific pairs -- Create higher-priority routing policies (priority 50) that allow routes between specific VPC pairs. Because these policies have a lower priority value (higher precedence), they override the deny-all policies for the specified VPCs.
To allow additional VPC pairs to communicate later, add more high-priority allow policies without modifying the existing deny-all policies.
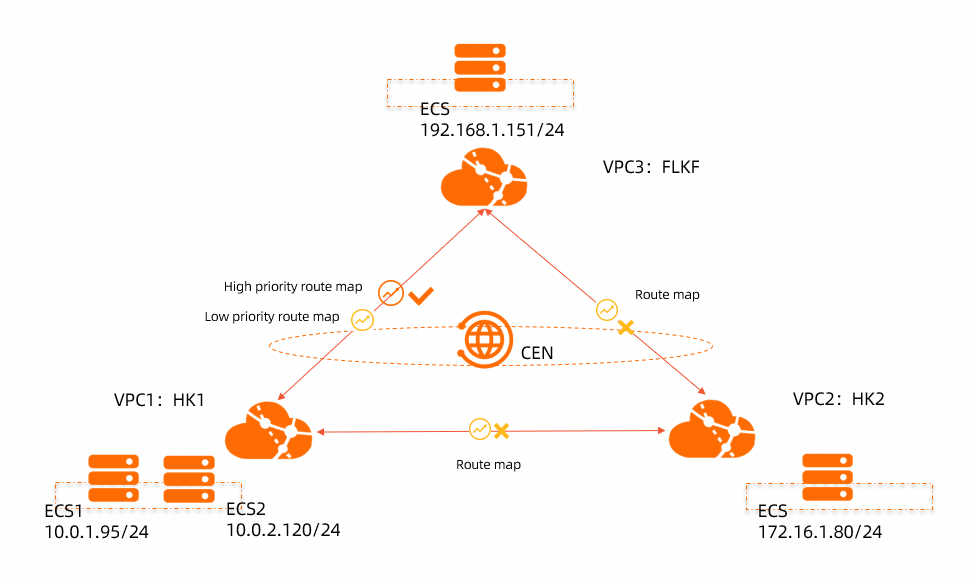
Scenario
In this example, three VPCs are attached to the same CEN instance:
VPC1 and VPC2 are in the China (Hong Kong) region.
VPC3 is in the Germany (Frankfurt) region.
Goal: Allow only VPC1 and VPC3 to communicate. Block all other VPC-to-VPC communication, including VPC1-VPC2 and VPC2-VPC3.
Connectivity matrix
| VPC1 | VPC2 | VPC3 | |
|---|---|---|---|
| VPC1 | -- | Denied | Allowed |
| VPC2 | Denied | -- | Denied |
| VPC3 | Allowed | Denied | -- |
Network topology
Prerequisites
Before you begin, make sure that you have:
A CEN instance. For more information, see CEN instances
Network instances that need to communicate attached to the same CEN instance. For more information, see Manage network instance connections
A bandwidth plan with inter-region bandwidth allocated. For more information, see Use bandwidth plans and Manage inter-region connections
Network details
| VPC | Region | CIDR block | vSwitch CIDR | ECS instance IP |
|---|---|---|---|---|
| VPC1 | China (Hong Kong) | 10.0.0.0/8 | vSwitch1: 10.0.1.0/24 | ECS1: 10.0.1.95 |
| vSwitch2: 10.0.2.0/24 | ECS2: 10.0.2.120 | |||
| VPC2 | China (Hong Kong) | 172.16.0.0/12 | 172.16.1.0/24 | 172.16.1.80 |
| VPC3 | Germany (Frankfurt) | 192.168.0.0/16 | 192.168.1.0/24 | 192.168.1.151 |
Step 1: Create deny-all routing policies
Create two routing policies -- one on each regional transit router -- to block all VPC-bound routes. Both policies use the same configuration but apply to different regions.
To add a routing policy:
Log on to the CEN console.
On the Instances page, click the ID of the CEN instance.
On the instance details page, click the ID of the transit router in the target region.
On the transit router details page, click the Route Table tab, and then click Routing Policies.
On the Routing Policies tab, click Add Routing Policy.
Deny-all policy for Germany (Frankfurt)
On the Add Routing Policy page, configure the following settings and click OK:
| Parameter | Value |
|---|---|
| Routing Policy Priority | 100 |
| Description | VPCs in the Germany (Frankfurt) region reject routes from the transit router |
| Region | Germany (Frankfurt) |
| Policy Direction | Egress Regional Gateway |
| Match Conditions | Destination Instance Type: VPC |
| Action Policy | Reject |
Deny-all policy for China (Hong Kong)
Navigate back to the Routing Policies tab, click Add Routing Policy, and configure the following settings:
| Parameter | Value |
|---|---|
| Routing Policy Priority | 100 |
| Description | VPCs in the China (Hong Kong) region reject routes from the transit routers |
| Region | China (Hong Kong) |
| Policy Direction | Egress Regional Gateway |
| Match Conditions | Destination Instance Type: VPC |
| Action Policy | Reject |
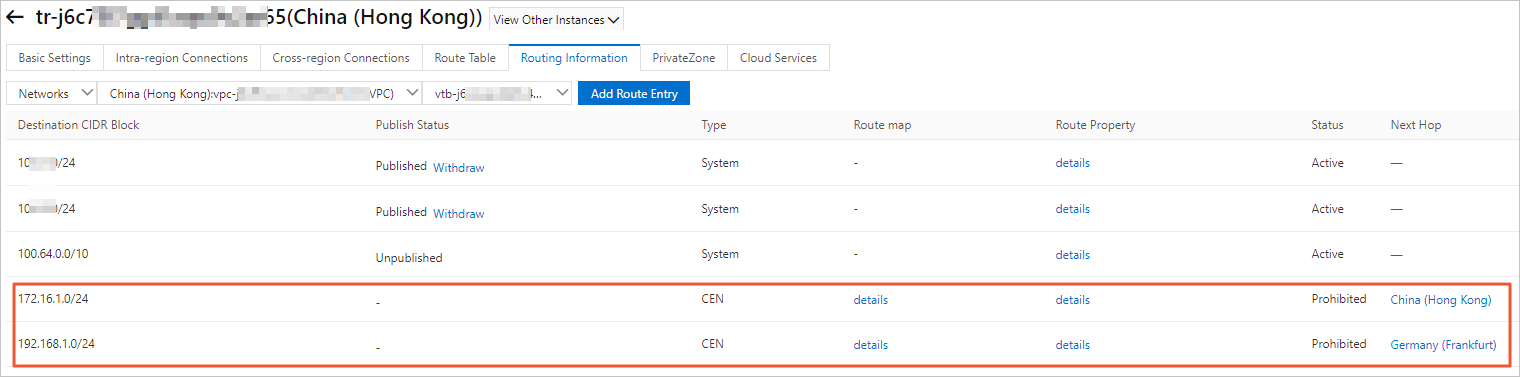
Verify the deny-all policies
After you add both policies, click the Network Routes tab to confirm that VPC1, VPC2, and VPC3 all reject routes from the transit routers. The following screenshot shows VPC1 rejecting routes from the transit routers in the China (Hong Kong) and Germany (Frankfurt) regions.
Step 2: Create allow policies for VPC1 and VPC3
To enable bidirectional communication between VPC1 and VPC3, create two allow policies -- one on each regional transit router. These policies have a higher priority (lower value) than the deny-all policies, so they take precedence for the specified VPC pair.
Allow VPC1 to receive routes from VPC3
Navigate to the routing policies page for the China (Hong Kong) transit router. Click Add Routing Policy and configure the following settings:
| Parameter | Value |
|---|---|
| Routing Policy Priority | 50 |
| Description | Allow VPC1 to accept routes from VPC3 |
| Region | China (Hong Kong) |
| Policy Direction | Egress Regional Gateway |
| Match Conditions | Source Region: Germany (Frankfurt) |
| Source Instance ID List: ID of VPC3 | |
| Destination Instance ID List: ID of VPC1 | |
| Action Policy | Allow |
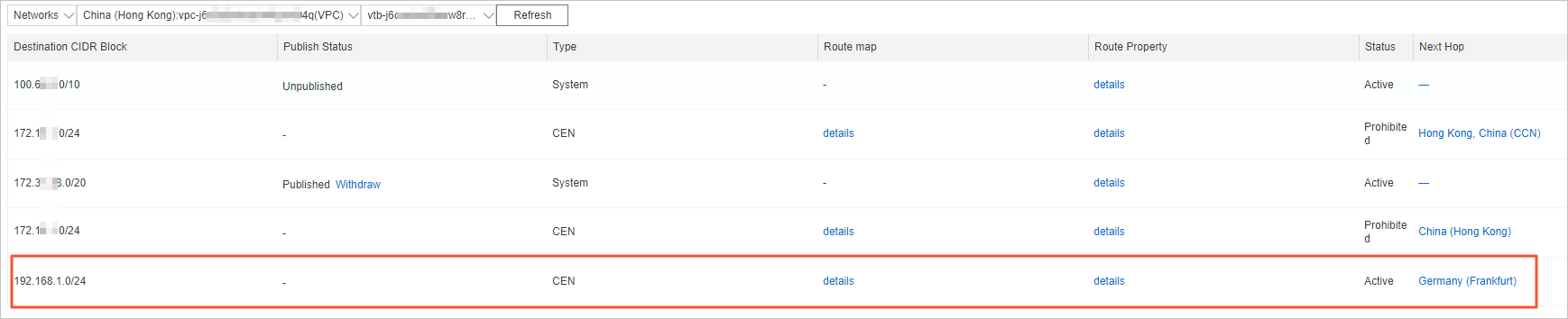
After you add this policy, click the Network Routes tab to confirm that VPC1 now accepts routes from VPC3.
Allow VPC3 to receive routes from VPC1
Navigate to the routing policies page for the Germany (Frankfurt) transit router. Click Add Routing Policy and configure the following settings:
| Parameter | Value |
|---|---|
| Routing Policy Priority | 50 |
| Description | Allow VPC3 to accept routes from VPC1 |
| Region | Germany (Frankfurt) |
| Policy Direction | Egress Regional Gateway |
| Match Conditions | Source Region: China (Hong Kong) |
| Source Instance ID List: ID of VPC1 | |
| Destination Instance ID List: ID of VPC3 | |
| Action Policy | Allow |
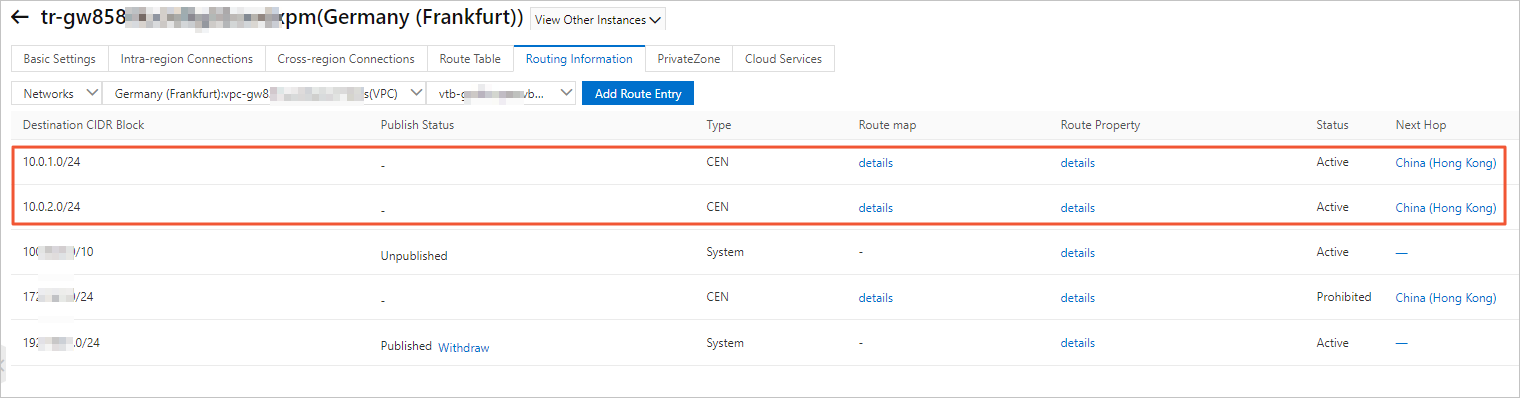
After you add this policy, click the Network Routes tab to confirm that VPC3 now accepts routes from VPC1.
Routing policy summary
The following table lists all routing policies created in this example:
| Region | Priority | Direction | Match condition | Action | Purpose |
|---|---|---|---|---|---|
| Germany (Frankfurt) | 100 | Egress Regional Gateway | Destination Instance Type = VPC | Reject | Block all VPC communication in Frankfurt |
| China (Hong Kong) | 100 | Egress Regional Gateway | Destination Instance Type = VPC | Reject | Block all VPC communication in Hong Kong |
| China (Hong Kong) | 50 | Egress Regional Gateway | Source Region = Frankfurt, Source = VPC3, Destination = VPC1 | Allow | VPC1 receives VPC3 routes |
| Germany (Frankfurt) | 50 | Egress Regional Gateway | Source Region = Hong Kong, Source = VPC1, Destination = VPC3 | Allow | VPC3 receives VPC1 routes |
Step 3: Test connectivity
Log on to the ECS instances and run ping commands to verify the routing policies work as expected.
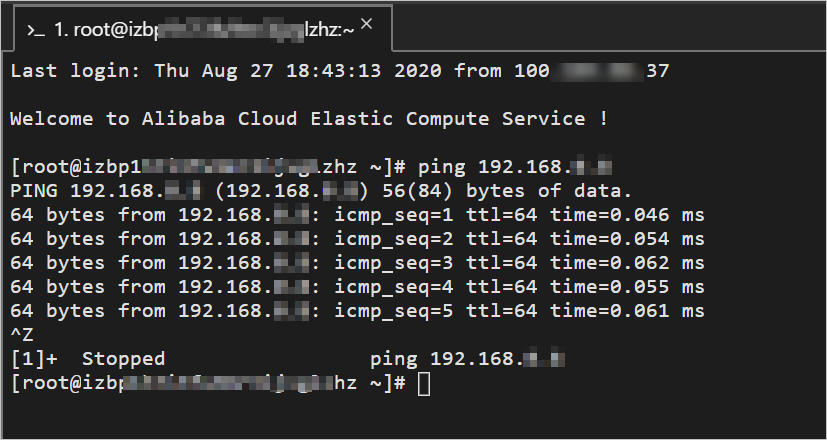
Test 1: VPC1 to VPC3 (expected: success)
Log on to ECS1 in VPC1.
Ping the ECS instance in VPC3:
ping 192.168.1.151VPC1 can reach the ECS instance in VPC3. This confirms that VPC1 and VPC3 can communicate.
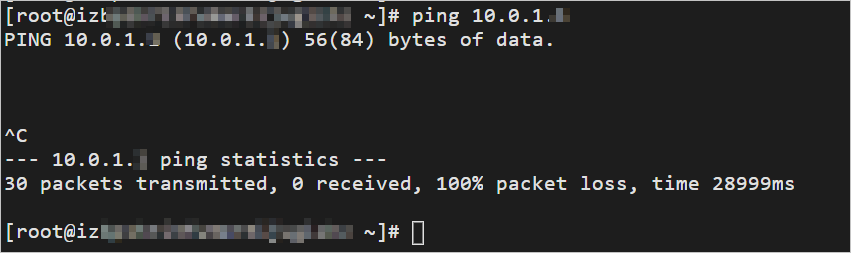
Test 2: VPC2 to VPC1 (expected: failure)
Log on to the ECS instance in VPC2.
Ping ECS1 in VPC1:
ping 10.0.1.95The ping fails. This confirms that VPC2 cannot communicate with VPC1.
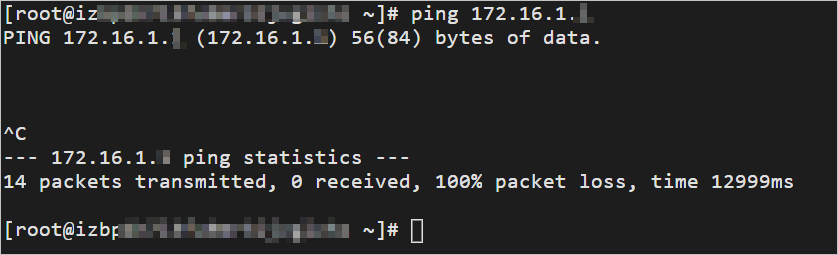
Test 3: VPC3 to VPC2 (expected: failure)
Log on to the ECS instance in VPC3.
Ping the ECS instance in VPC2:
ping 172.16.1.80The ping fails. This confirms that VPC3 cannot communicate with VPC2.
Troubleshooting
| Symptom | Possible cause | Solution |
|---|---|---|
| VPCs still communicate after adding deny-all policies | Incorrect policy configuration | Verify that the Policy Direction is set to Egress Regional Gateway and the Destination Instance Type is set to VPC. Make sure you created deny-all policies on both regional transit routers. |
| VPCs cannot communicate after adding allow policies | Incorrect priority or VPC IDs | Verify that the priority value of the allow policies (50) is lower than the deny-all policies (100). A lower value means higher precedence. Check that the Source Instance ID List and Destination Instance ID List contain the correct VPC IDs. |
| Unexpected routing behavior | Policy evaluation order misunderstanding | Policies are evaluated from the lowest priority value (highest precedence) to the highest. When a route matches a policy, the action is applied and no further policies are evaluated for that route. |